Table of Contents
Toggle- What is the GRC strategy in the context of SAMA & NCA?
- Why Should Businesses in Saudi Arabia Prioritize a GRC Strategy?
- Preparatory Steps Before Implementing GRC Strategy in Saudi Business
- How to Implement a GRC Strategy in Saudi Arabia for SAMA and NCA Alignment
- Benefits of a GRC Framework in Saudi Arabia’s business
- GRC Strategy FAQs
What is the GRC strategy in the context of SAMA & NCA?
A GRC strategy, or otherwise “Governance-Risk-Compliance,” is a well-organized structure to monitor and put into practice how a business governs its operations, assesses, and mitigates risks. This ensures that the ongoing compliance is in line with the respective regulations.
When it is applied in Saudi Arabia’s financial sector, SAMA compliance means aligning with the SAMA Cyber Security Framework requirements, which are particularly designed for fintech organizations. It is defined by Saudi Arabia’s Monetary Authority.
Another regulation, NCA, refers to following the cybersecurity measures that the National Cyber Security Authority declared. This deals with cybersecurity in broader terms. The purpose behind the GRC strategy is to combine SAMA compliance and NCA regulations smoothly to form a unified cybersecurity approach.
Why Should Businesses in Saudi Arabia Prioritize a GRC Strategy?
Regulatory alignment
Based on the kingdom’s cybersecurity approach, it is a legal requirement for every financial institution and fintech firm to abide by the SAMA CSF.
When considering the NCA, it enforces national cybersecurity standards. It might audit or penalize businesses for failing to comply with it. So to avoid these hurdles, businesses can adhere to a strong GRC strategy so that it complies with both the SAMA and NCA regulations.
Combining both for efficiency
It would be complex to apply both the compliance programs with separate efforts. When combining SAMA and NCA, it lets you reuse controls, governance structures, and monitoring across both regimes. This combined initiative costs less and minimizes internal friction.
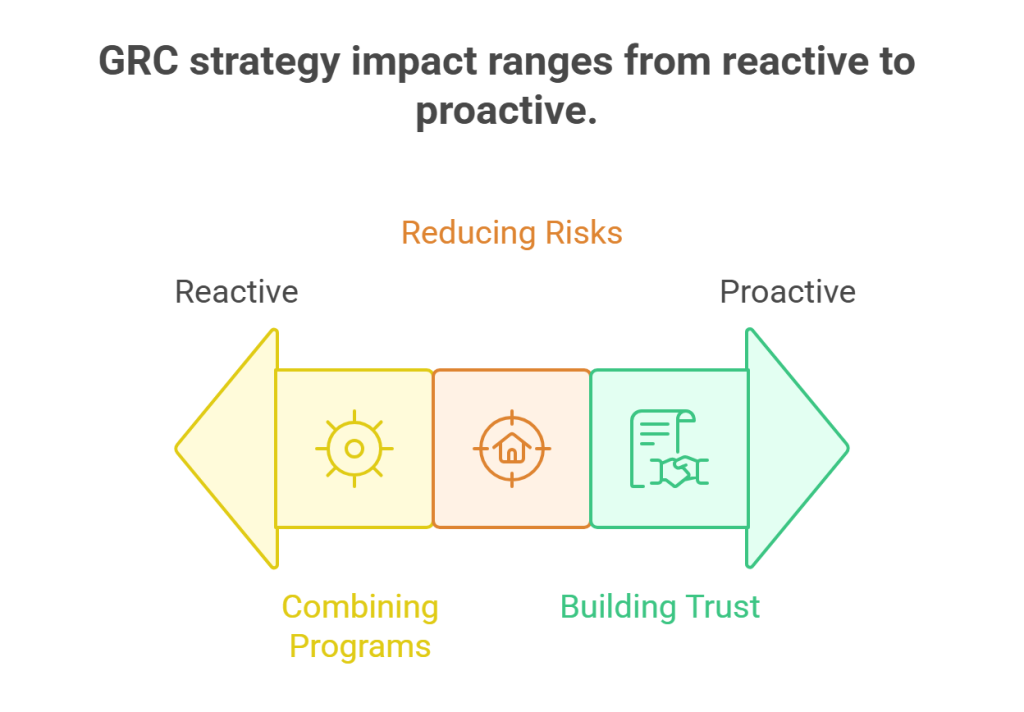
Reducing risks
Following a well-defined GRC strategy helps businesses proactively identify, manage, monitor, and report risks. This means the risks are detected earlier and a stronger cybersecurity posture is established.
Building Trust
Putting into practice a valid GRC strategy particularly aligned with SAMA and NCA adds credibility for your business. A strong infrastructure improves trust among partners, customers, and investors. In other terms, complying with these regulations is not a method applied to deter fines; instead, it serves in building reputation.
Preparatory Steps Before Implementing GRC Strategy in Saudi Business
Assessing Risk
Do a thorough risk assessment to identify and find the threat factor that targets your organization. Here you must know about the essential VAPT practices, as they involve vulnerability assessment and penetration testing in business activities and systems.
Once you recognize the unique attack patterns and vulnerabilities that are affecting your organization, it is easy to prioritize the area to pay attention to the most. This evaluation helps in preparing a custom GRC strategy based on the needs.
Conducting a Gap Analysis
The next step is to assess where your organization currently stands. Conduct a review to know the existing governance and risk management structures. This will help spot the gaps against the SAMA CSF and NCA’s Essential Cybersecurity Controls domains. So, performing a proper gap analysis highlights what’s missing in policies, risk registers, or technical safeguards.
Also Read : Achieving SAMA CSF Compliance: Step-by-Step Implementation for Fintechs
Identify Assets to be protected
Before implementation, you must define the assets of an organization you are aiming to protect. It can be the company’s data, networks, and systems. Most of these assets involve holding sensitive data, and identifying such major assets is important to pay more focus on building security measures for effective protection.
Policy Harmonization
To implement a combined approach, both SAMA CSF and NCA must be combined into one unique strategy. This policy preparation benefits by avoiding conflicts in terms of applying the regulatory rules. A combined policy framework allows easy management of governance, risks involved, and cybersecurity handled across the organization.
How to Implement a GRC Strategy in Saudi Arabia for SAMA and NCA Alignment
Prepare Governance Structure
Initially you have to set up a governance framework clearly defining responsibilities for each role. By sharing controls among respective authorities like compliance officers and security managers, it defines clear accountability for all GRC activities. Framing this structure serves as the main pillar in building an effective GRC strategy that aligns with the SAMA & NCA.
A Unified Cybersecurity Strategy
Cyberattacks are a major threat, especially in data-involved organizations. So, it’s important to prepare a comprehensive cybersecurity strategy that aligns perfectly with the SAMA cybersecurity framework and NCA ECC.
This strategy should address risk management, policy implementation, and incident response in accordance with the governance-risk-compliance framework.

Implement Risk Management Controls
Once the approach is fixed, organizations need to put in place both technical and administrative controls. This includes monitoring systems, access management, and measures to reduce operational and cyber risks.
Along with this, continuous evaluation should be processed at regular intervals. It helps in verifying if the GRC implementation adapts to new threats and maintains compliance with both regulators.
Monitor Compliance
Post-implementation process, it is essential to regularly monitor and issue reports on the current compliance status. Using dashboards and automated tools, experts should keep track of compliance status, risk levels, and control effectiveness.
These activities are to be documented, and the reports generated must be clearly recorded, as those are evidence of the consistent processes undertaken.
Train Employees
Employees must understand their role in maintaining compliance. Conduct regular training so staff can identify cyber threats, follow policies correctly, and respond to incidents when they spot them. By training them, businesses prepare a strong environment to identify misalignment and threats before they can harm or turn into threats to the systems.
Also Read : Preparing for NCA ECC Audits: Implementation Guide for Your Business
Regular Review
After implementation, regular reviews should be conducted on the GRC framework. Continuous assessments must include periodical audits, risk evaluation, and updates on policies and controls whenever required.
Such analysis keeps the governance, risk, and compliance framework effective, and the business remains fully aligned with SAMA CSF and NCA ECC requirements.
Benefits of a GRC Framework in Saudi Arabia’s business
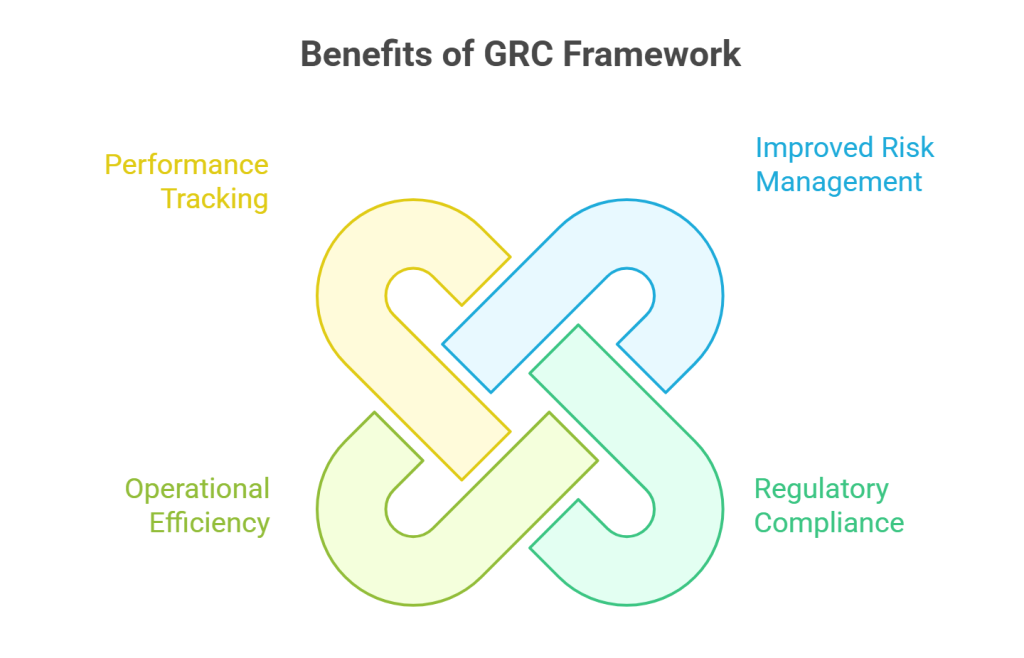
Improved Risk Management
A GRC framework-enabled business environment can be easy to identify and manage risks proactively. It unifies cybersecurity, legal, and operational controls under one framework.
Aligning with regulatory Compliance
Integrating GRC practice in a business can help comply with regulatory rules in daily operations. It allows organizations to follow the mandatory rules, especially the SAMA and NCA guidelines, without the need for constant manual checks.
Better Operational Efficiency
By addressing risks and staying committed to alignment with GRC practices, businesses improve their operations. The workflow gets smooth and improves collaboration across departments
Performance Tracking
With continuous monitoring and report generation, businesses can track the health of their GRC strategy and make necessary improvements over time.
Every organization work differently and has different operational challenges, and implementing a regulatory framework into action can be a hurdle sometimes, especially when they lack proficient people in-house. They need an expert who can plan and put it into action.
Choosing a well-trained professional is essential, as they can only smoothly define a GRC strategy aligned to the industry’s needs and processes. Wattlecorp has well-trained risk and compliance experts who have experience dealing with complex business environments
With a proven record, they have tightened the security using a customized GRC strategy that perfectly aligns with the SAMA Cybersecurity Framework and NCA’s Essential Cyber Security Controls.
GRC Strategy FAQs
1.How can organizations align their GRC strategy with SAMA and NCA?
First, your organization must perform gap analysis and identify the potential weak areas. Then, with expert assistance, prepare a unified compliance map that can comply with both SAMA CSF and NCA and implement it. Following this, do regular checks and document the results.
2.Why is regulatory alignment important for Saudi banks?
Banks are the crucial source of huge data, and it is critical business. Aligning to regulatory rules helps businesses stay in terms with the updated compliance, avoid penalties, and build trust among customers. The operations also run efficiently through unified risk and control management.
3.How does penetration testing support GRC compliance?
Penetration testing validates technical controls. Starting with the vulnerability assessment, it follows up with penetration testing and provides evidence of continuous improvement for SAMA and NCA audits.