Table of Contents
Toggle- Why Automating SAMA CSF Matters For Saudi Businesses?
- What is SAMA CSF Compliance and What are its Requirements in Saudi Arabia?
- Common Compliance Challenges in Saudi Arabia
- Best Tools for Automating SAMA CSF Compliance
- Implementation Strategies for Automating SAMA CSF Compliance
- Real-World Use Cases from Saudi BFSI
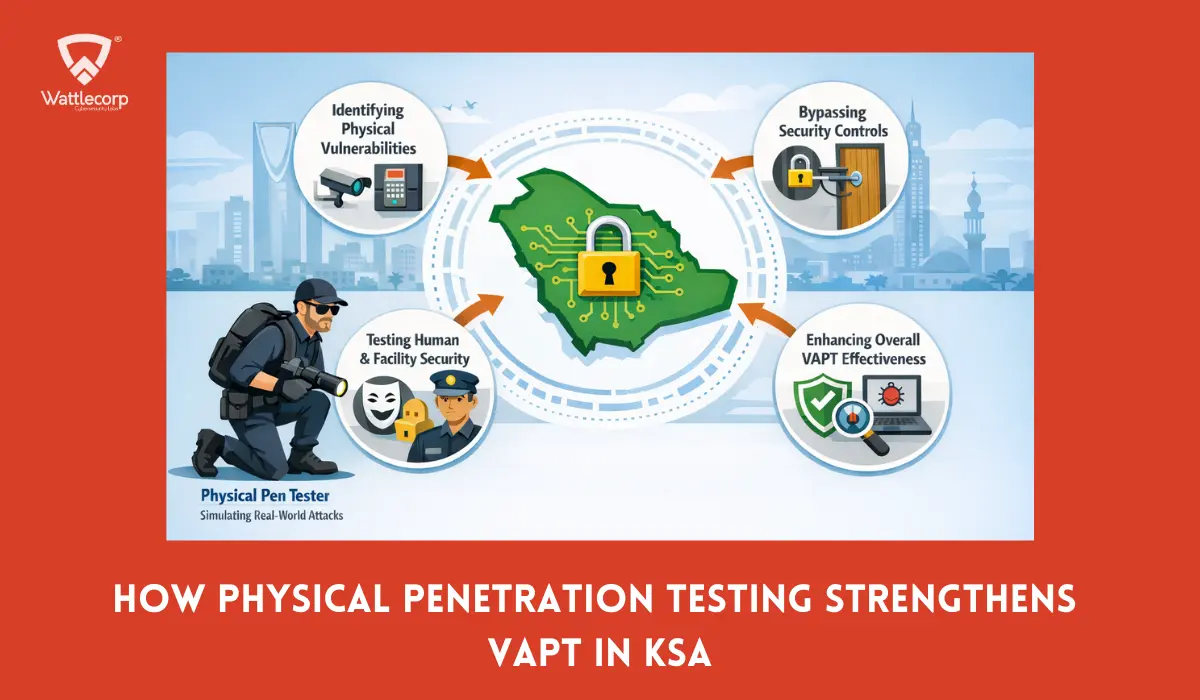
- The Role of Penetration Testing in Automating SAMA CSF Compliance
- SAMA CSF FAQs
Why Automating SAMA CSF Matters For Saudi Businesses?
Manual compliance efforts are becoming costly and error-prone, with regulators demanding continuous monitoring. A sure-shot reminder that urges Saudi Arabia’s financial sector to undergo a complete rewiring of their existing compliance practices.
Considering the different regulatory frameworks that the Kingdom necessitates to comply with, the SAMA CSF happens to be the most challenging. First of all, it’s the financial service enterprises who should oblige with this regulation. Heeding to vital business operations at the same time makes it even more complicated.
As per statistics, an average financial organization in Saudi Arabia spends a good 40% of their earnings to achieve compliance. However, they still face regulatory penalties and reputational damage. Again an urgent reminder to automate their SAMA CSF compliance process.
Automation has significantly replaced manual efforts in this digital era. However, with evolving cyber threats in the region, which automation tools will offer you the visibility and trust that emerging SAMA CSF regulations demand? Definitely, as a business operating within the finance sector, you’ll need one that ensures security at every step of attaining and staying compliant. This is where Penetration Testing comes to your aid.
That being said, we will walk you through the essential steps therein while explaining how penetration testing plays a significant role in automating and securing SAMA CSF Compliance.
What is SAMA CSF Compliance and What are its Requirements in Saudi Arabia?
The SAMA CSF, established in 2017, is a mandatory set of guidelines established by the Saudi Arabian Monetary Authority aka Saudi Central Bank. Introduced to protect the Saudi financial sector from potential cyber threats, SAMA CSF’s core requirements include strictly ensuring security, transparency, and resilience.
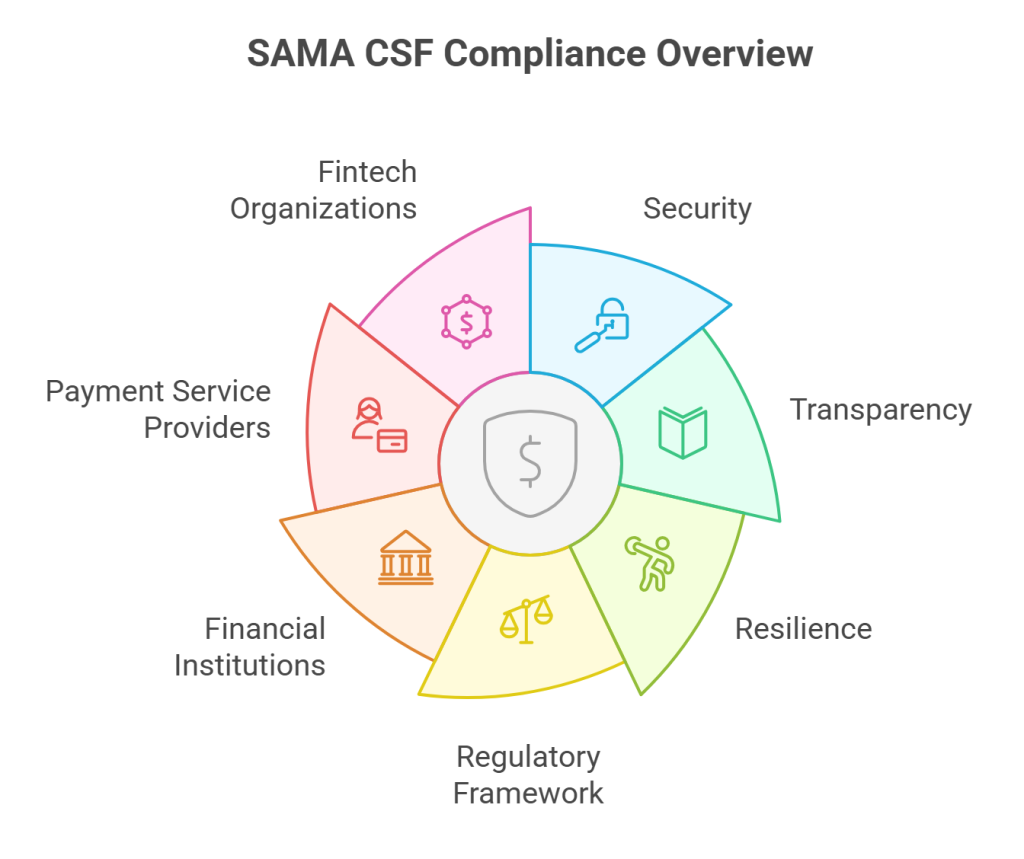
The SAMA CSF regulatory framework undergoes regular updates by setting stringent cybersecurity standards. Every financial institution, be it an investment agency, bank, or an insurance company, is expected to oblige by these regulations.
SAMA CSF rules also apply to the payment service providers, financial service enterprises, and fintech organizations, which are programmed to maintain customer data integrity and ensure allround stability for the growing economy of Saudi Arabia
SAMA CSF Compliance Key Requirements
The SAMA CSF cybersecurity framework essentially encompasses 5 key domains with respective controls and corresponding requirements. Here are they for your quick reference:

- Cybersecurity Governance: Sets robust governance structures and defines clear roles and responsibilities from a cybersecurity standpoint.
- Cybersecurity Defense: Involves adding multiple security layers that include network security controls, secures system configurations, deploys vulnerability management programs, and offers endpoint protection. Also helps you stay ahead of cyber incidents while updating baseline security measures through advanced threat alerts and prevention systems.
- Cybersecurity Incident Management: To promptly detect, respond, and recover from cyber threats.
- Third-Party Cybersecurity Risk Management: Involves continuously identifying, assessing, and addressing the cybersecurity risks posed by your vendors and partners.
- Cybersecurity Resilience: Improves and enhances business continuity through a comprehensive incident response plan that involves installing and maintaining backup systems. This not only strengthens resilience, but also fosters disaster recovery capabilities for financial institutions when struck by cyber incidents.
Meeting these core SAMA CSF requirements is critical for Saudi Arabia’s financial sector when it regards achieving the Vision 2030 goal of becoming a global hub of technology.
The regulatory weightage of the SAMA CSF framework strongly implies that it’s an obligation that every business entity in Saudi Arabia should continuously adhere to.
Common Compliance Challenges in Saudi Arabia
The Kingdom of Saudi Arabia is all set to transform on economic, technology, and innovative grounds, thanks to its Vision 2030 goals again. While these efforts necessitate complying with essential legal and cybersecurity frameworks, particularly SAMA CSF, there do exist specific factors that make achieving compliance challenging.
Here are the major ones:
Complexities in Meeting Regulatory Requirements
The dynamic nature of Saudi Arabia’s regulatory environment is one major challenge. Take for instance the latest amendments to the Personal Data Protection Law (PDPL) made by Saudi’s SDAIA (Saudi Data and AI Authority). While these are meant to secure personal data, these are likely to create conflicts between the need to achieve robust data protection and heeding to the specific operational objectives.
Technology and Digital Transformation
Saudi Arabia’s rapid digitization of its economy can impact compliance achievement. Emerging technologies happen to be the real culprits in this regard, due to businesses adopting artificial intelligence (AI) in the Kingdom.
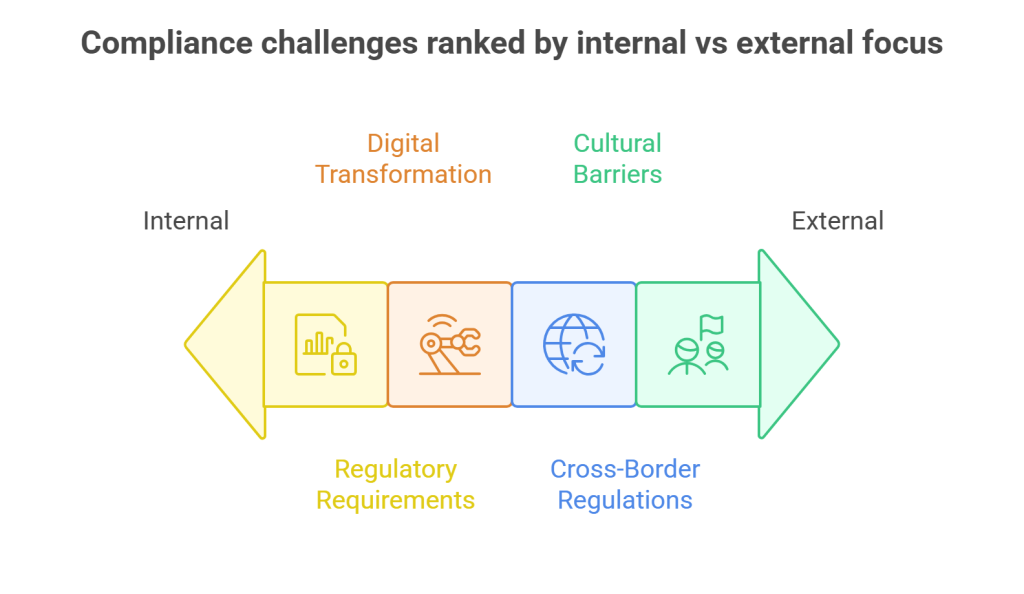
Difficulties in Aligning with Cross-Border and International Regulations
The nation’s connection with global enterprises has been seen to affect meeting regulatory compliance in Saudi Arabia. The need to align local compliance requirements with international standards, such as GDPR, ISO 27001, NIST, SOX, is the most challenging one in this regard.
Cultural and Language Barriers
The unique linguistic and cultural context of Saudi Arabia can make it difficult for companies operating there to meet compliance standards. International businesses serving their Saudi clients will definitely find it difficult to understand regulatory requirements published in the Arabic language.
Coupled with these are the stakeholder expectations and cultural nuances affecting compliance strategies.
Shortage of Resource and Expertise
A business lacking the needed expertise and resources to navigate efficiently across different regulatory standards will indeed find it hard to comply with the diverse regulatory standards in Saudi Arabia. The shortage of compliance professionals coupled with the rapid pace at which regulatory requirements are changing makes it even more challenging.
Organizations lack the capabilities to hire and retain qualified compliance officers makes it even more complex.
Best Tools for Automating SAMA CSF Compliance
The complexities associated with meeting SAMA CSF Compliance requirements need a streamlined process. You need to, therefore, utilize proper tools and platforms to carry out a successful automation.
Listed and explained below are a comprehensive suite of the applicable ones to reduce your manual efforts for achieving compliance.
Governance, Risk Management, and Compliance Platforms (GRC)
The Governance, Risk Management, and Compliance Platforms or GRC have been recognized as one of the most popular software solutions providers to help you automate your compliance process for SAMA CSF. These offer specialized tools for various compliance-related tasks. Among these include the RSA Archer, the leading enterprise-level GRC Solution, which helps meet specific Saudi Arabian Monetary Authority’s CSF requirements. These comprise policy management, risk assessment, and real-time monitoring throughout the CSF domain.

While GRC platforms help ensure compliance with every aspect of SAMA CSF requirements, the RSA Archer aids in efficiently automating the compliance process.
Utilized by Fortune 500 Companies and also some forward-thinking GCC enterprises, RSA Archer remains as the most-preferred GRC tool for automating the SAMA CSF Compliance process.
Identity and Access Management (IAM) Solutions
The IAM-driven solutions are yet another vital compliance automation tool that help manage and secure sensitive data and resources. by applying features like Multi-factorial Authentication (MFA), Privileged Access Management (PAM), and Single Sign-On (SSO).
Tools include Microsoft Entra ID (Azure Active Directory/Azure AD), which offers a robust IAM solution for Saudi organizations to achieve SAMA CSF Compliance. By utilizing the aforementioned key components, Microsoft Entra ID effectively helps determine who can access what data and when.
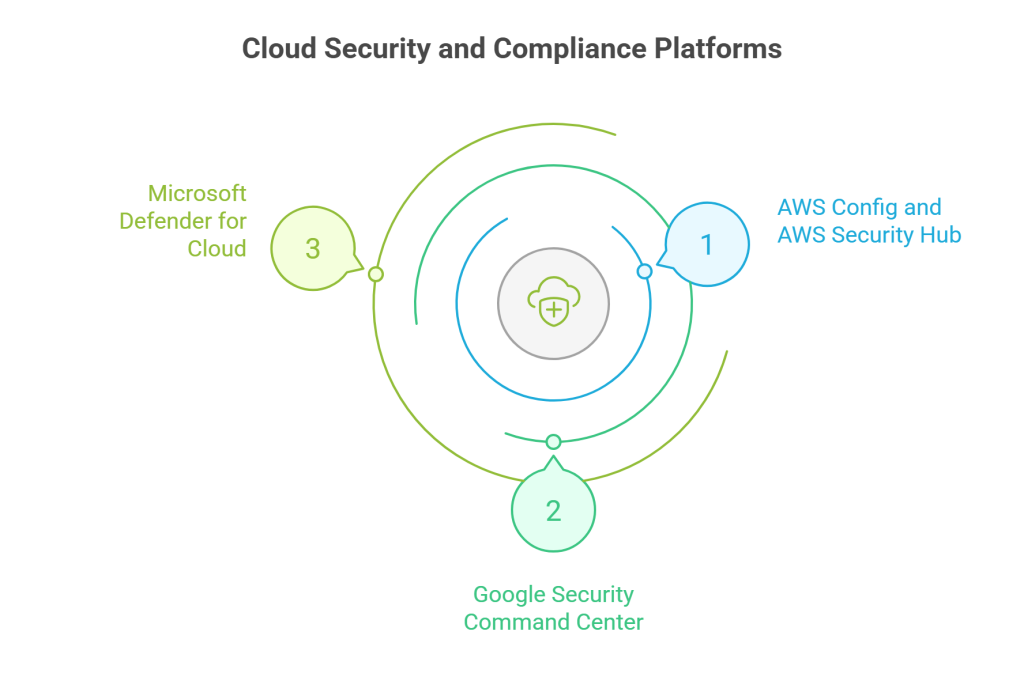
Cloud Security and Compliance Platforms
Dedicated to secure Cloud-native apps and attain compliance, these platforms offer tools, such as AWS Config and AWS Security Hub, Google Security Command Center, and Microsoft Defender For Cloud.
- AWS Config and AWS Security Hub: Consist of rules that can be configured to support alignment with SAMA CSF Compliance requirements.These help automate compliance monitoring for cloud-based infrastructure.
- Google Security Command Center: Helps derive centralized visibility and Google Cloud security control while enabling compliance monitoring that align with SAMA CSF regulatory requirements.
- Microsoft Defender for Cloud: Suitable to enhance cloud security posture management by creating Compliance Dashboards. Customized for meeting SAMA CSF requirements, Microsoft Defender automates security assessments, extending to offering prompt recommendations for improving security posture.
Integration and Orchestration Platforms
The Integration and Orchestration Platforms automate compliance with SAMA CSF by integrating the necessary security tools. What follows is a security orchestration that involves processes, such as evidence collection, risk assessment, and documentation. These simultaneously assist with implementing, monitoring, and management of cybersecurity controls.
The essential tools comprise Phantom and Demisto.
- Phantom: Now called Splunk SOAR (Security Orchestration, Automation, and Response) Phantom helps configure security orchestration, automation, and response capabilities to automate SAMA CSF Compliance processes. These involve incident response, evidence collection, and reporting.
- Demisto (Cortex XSOAR): Helps undertake comprehensive security orchestration for automating complex compliance workflows. Also assists in automating compliance reporting by integrating multiple security tools.

If you wish to effectively automate SAMA CSF Compliance, you should learn to properly and securely configure the tools for this process.
Regular testing and monitoring of the automation process is critical to maintaining successful automation.
Maintaining human oversight is critical to ensure continued compliance of automated systems with evolving SAMA CSF Framework requirements.
Implementation Strategies for Automating SAMA CSF Compliance
The complexities associated with achieving and maintaining SAMA CSF Compliance can be truly overwhelming. Adopting a systematic approach makes the process seem even more tedious.
With automation, you get to simplify everything. Doing so, however, necessitates carefully blending technology, essential processes, and governance structures.
Once you ensure meeting all the above parameters, you’ve a structured process that helps you strategically implement SAMA CSF Compliance automation.
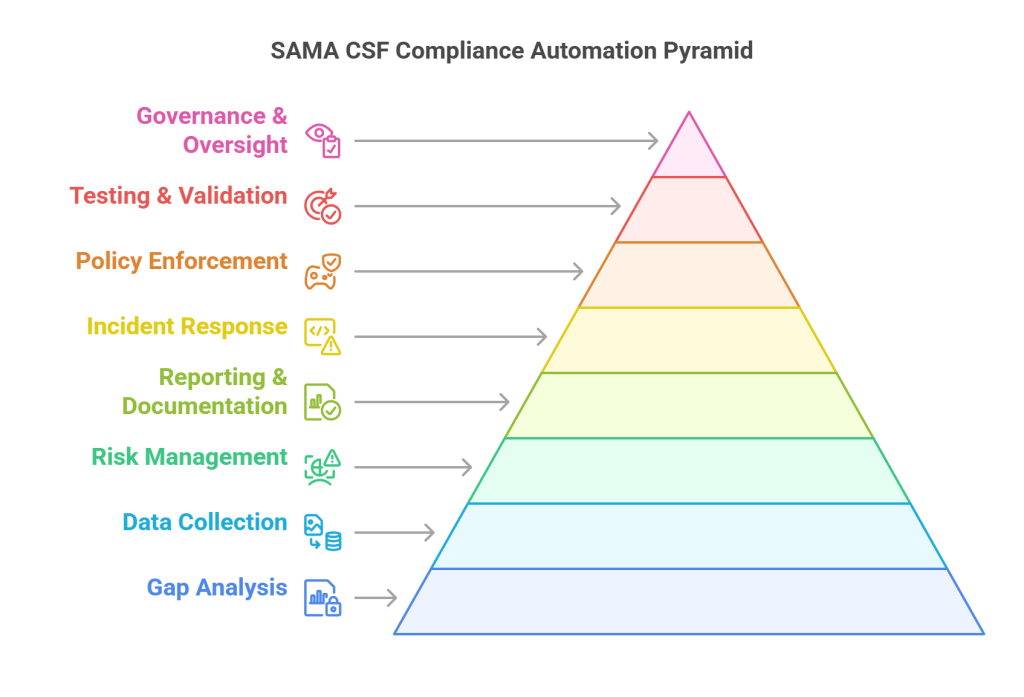
Comprehensive Gap Analysis
Cybersecurity experts opine that understanding your current compliance posture by mapping existing security controls against actual SAMA CSF requirements helps identify existing security gaps.
This will also help you prioritize areas and automate required tasks there to effectively derive improved compliance outcomes.
Also Read : Demystifying the Latest SAMA Cyber Security Framework for Financial Institutions in 2025
That said, you can now focus on undertaking continuous monitoring and risk assessment processes to improve your incident response capabilities.
Establish Automated Data Collection Mechanisms Across Critical Systems and Networks
While SAMA CSF demands extensive logging, monitoring, and reporting capabilities, these cannot be manually maintained. Nor is it possible to virtually manage them at scale.
Deploying automated tools can effectively and significantly help streamline the process to a significant extent by gathering compliance evidence, security metrics, and system performance data in real-time.
Techniques like these can significantly weigh down concerns related to maintaining data integrity and meeting auditability requirements during the process.
Develop Automated Risk Assessment and Management Workflows
In this stage, it’s deemed necessary to align the automated risk assessment process with SAMA CSF’s risk-based approach.
What this expects you to do is to establish systems that can automatically identify, categorize, and prioritize risks according to predefined criteria. Doing so will automatically trigger appropriate response action.
You need to, however, extend this automation to manage vulnerabilities. Doing so will allow systems to automatically detect, assess, and mitigate security flaws.based on their severity and specific time frame.
Implement Automated Compliance Reporting and Documentation Systems
This automation process involves generating required SAMA submissions while also supporting and maintaining audit trails, ensuring data accuracy and integrity, and providing real-time compliance dashboards.
Creating Automated Incident Detection and Response Capabilities
Involves identifying possible security events, assessing and classifying them based on their severity and impact;while creating appropriate responses. These should be in accordance with the set SAMA requirements.
Integrating these systems with existing cybersecurity infrastructure is equally important, taking care to also maintain detailed logging and reporting capabilities.
Establish Automated Policy Enforcement Mechanisms
Here, you should apply the right security controls across your organization on a consistent note.
The proposed systems should also automatically apply security configurations, monitor policy violations, and initiate remediation alerts.
Deploy Automated Testing and Validation Processes
For regularly verifying the effectiveness of the implemented controls, you should develop:
- Design automated testing and validation processes
- Create systems that can automatically execute compliance checks
- Generate evidence for control effectiveness
- Identify areas for improvement before they create complexities

Implement Automated Governance and Oversight Capabilities
Here, you derive real-time visibility into your compliance status through automatic escalation of vulnerability issues in your systems, apps, and networks.
While automation techniques can effectively reduce the workload, these, nevertheless, require human expertise and intervention to govern the essential processes embedded within.
Real-World Use Cases from Saudi BFSI
The real-world use cases of SAMA CSF by Saudi BFSI presents a handful of examples showcasing successful implementation of this compliance framework.
Case Study #1: Saudi National Bank (SNB) Undergoing a Massive Governance Transformation
Formed from the merging of the National Commercial Bank and Samba Financial Group in 2021, the SNB was reported to have thoroughly implemented SAMA CSF. Willing to know how? Read below.
The Process: The bank implemented a three-tier cybersecurity governance structure that comprised board-level oversight, operational security teams, and executive management committees.They also invested heavily (SAR 500 million) in cybersecurity infrastructure from 2019 to 2023. This comprised advanced threat intelligence platforms, AI-enhanced incident detection systems, and security orchestration tools.
Approaches: By establishing real-time cybersecurity dashboards for executive management and enabling clearer visibility into their security posture post implementation, the bank could finally confirm successful compliance with SAMA CSF.
Case Study #2: Insurance Sector’s Compliance Readiness with SAMA CSF
A Saudi insurance company effectively implemented unique SAMA CSF approaches that reflected their distinct operational models and customer bases.
The Process: This renowned and well-established insurance company installed specialized cybersecurity controls for protecting their customers’ health insurance data. This helped them address compliance requirements specific to both SAMA CSF and healthcare data protection regulations.
The Approach: When implementing advanced data classification systems to automatically identify and protect sensitive healthcare information, this insurer could successfully encrypt sensitive patient records in a specialized manner. Besides these outcomes achieved, the company could also:
- Ensure communication channel security through efficient healthcare providers
- Engage in automated compliance reporting across multiple regulatory frameworks, including SAMA CSF
Also Read : Achieving SAMA CSF Compliance: Step-by-Step Implementation for Fintechs
The Role of Penetration Testing in Automating SAMA CSF Compliance
With digital era evolving faster, traditional security testing methods can no longer tackle rapidly emerging cyber threats. And because Saudi Arabia demands strictly complying with regulations like SAMA CSF, you’re left with no other option than to abide by these requirements. Simultaneously, you should leverage security methods that can effectively keep you ahead of the threat curve while maintaining compliance.
Penetration testing plays an active role in automating SAMA CSF Compliance by proactively helping you identify and exploiting system vulnerabilities before real-world hackers get a chance to. In other words, it helps simulate cyber attacks, enabling you to achieve compliance with relevant cybersecurity frameworks in a region or nation, even from a global perspective.
- Effective Management of Security Controls: Penetration testing helps meet regulatory standards by validating security controls are functioning adequately, thus offering tangible evidence of compliance.
- Ongoing Security and Compliance: From a periodic exercise, penetration testing turns into a continuous validation process to achieve enhanced security and compliance.
- Risk Remediation: Since the SAMA Cybersecurity Framework emphasizes a risk-based security approach, organizations complying with it areduly expected to assess and validate their security controls However, automated penetration testing allows for systematic identification and mitigation of system vulnerabilities to help achieve compliance objectives.
- Proactive Approach: With penetration testing, financial service providers can fix security gaps in advance, also preventing compliance violations and security incidents.
No doubt that automated penetration testing when integrated within the SAMA CSF compliance process extends beyond basic vulnerability identification and mitigation.
Wattlecorp, a pioneer in offering penetration testing services for its clients across the globe,is one such cybersecurity firm that can seamlessly integrate pentesting within the compliance framework.

This cybersecurity service provider is no one’s second when it comes to offering expert penetration testing to help businesses meet varied security and compliance as dictated by national-cum-industrial standards.
Struggles to cope with the pressures of regulations to achieve continued compliance can either make or break a business.
With the right automation tools selected, especially those integrating penetration testing, a financial enterprise can genuinely thrive and succeed in attaining and ensuring compliance.
Every step you put forward to automate compliance saves you from the cost of non-compliance and associated risks.
Compliance is not a one-time achievement, it’s an ongoing commitment that seeks continuous alignment with the evolving security landscape.
The use of applicable tools like Secusy AI, Phantom (SOAR), etc., for automating the compliance process with SAMA CSF are those that actually reduce manual load associated with the process.
Nonetheless, Saudi Arabia’s need to automate its SAMA CSF compliance additionally warrants, integrating penetration testing in all capability and expertise.
Doing so will not only improve its security, but will also help streamline the compliance process, especially for companies operating in critical industrial sectors like BFSI.
At Wattlecorp, our professional pentesters with their knowledge and proven expertise can adeptly simplify the compliance processes for you through penetration testing-integrated compliance automation. This is what makes us the top-ranked penetration testing service providers in Saudi Arabia.
Whether it is achieving SAMA CSF Compliance or other relevant security standards, our pentesters make sure you stay both secure and compliant as per industry and national requirements. This ensures you meet SAMA CSF regulators’ expectations with due diligence.
Want to know more about our SAMA Compliance Services in Saudi Arabia? Visit our corresponding webpage.
SAMA CSF FAQs
1.What is the SAMA CSF and why is it critical for Saudi financial institutions?
SAMA CSF (Saudi Arabian Monetary Authority Cybersecurity Framework) is a mandatory regulatory requirement for the Saudi financial institutions. Issued by the Saudi Central Bank, previously Saudi Arabian Monetary Authority, SAMA CSF primarily serves to protect financial service providers (operating within the BFSI sector) from cyber threats and attacks.
2.What tools can automate SAMA CSF compliance effectively?
Choosing the right automation tools that support SAMA CSF compliance depends on how well they align with your cybersecurity governance and control processes.
Here are some of the key capabilities that you should look for in this regard:
● Simplify and standardize risk assessments
● Automatically collect evidence
● Continuously monitor your security posture and detect control deviations
● Provide centralized dashboards and compliance reporting
There are platforms like CyberArrow, Secusy AI, and EasyAudi that are considered as some of the preferable options to automate the SAMA-aligned compliance process.
Additionally, tools like Splunk SOAR (Phantom), Cortex XSOAR (Demisto), RSA Archer, and AWS Config can further strengthen your cybersecurity framework by enabling:
● Security orchestration and automated incident response
● Cloud infrastructure configuration monitoring and compliance checks
● Continuous cloud security posture management
You should not mistake these tools to make your organization automatically compliant with the SAMA CSF. Rather, these support ongoing compliance by reducing your manual tasks, improving visibility, and ensuring timely control execution. In fact, it is their proper utilization that leads you to achieve and ensure compliance.
3.How does automation reduce the cost of SAMA CSF compliance?
Automating SAMA CSF compliance can benefit your business in a lot of ways. It can:|
● Reduces manual efforts by streamlining repeated tasks
● Decreases operational cost
● Minimizes human errors
● Improves or optimizes resource efficiency
● Prevents reputational damage
● Everts risks related to costly penalties
4.What are some real-world use cases of SAMA CSF automation in Saudi Arabia?
Financial organizations in Saudi Arabia implement SAMA CSF automation to:
● Automate SAMA Compliance management and monitoring
● Improve security controls
● Streamline risk management and reporting processes
● Prove compliance to the regulator or auditor
5.How does penetration testing support SAMA CSF compliance in Saudi organizations?
If financial service enterprises like banks, fintech firms, etc, integrate penetration testing into their SAMA CSF Compliance automation process, this will help them to:
● Mitigate cyber threats by simulating real-world attacks to identify potential security flaws and associate risks, thus preventing cyberattacks in a proactive manner.
● Strengthen an organization’s security posture through regular penetration testing that go in line with the specific criteria set by SAMA. This helps meet regulatory compliance requirements while ensuring sensitive data protection.