Table of Contents
Toggle- Why VAPT is Essential for Saudi Businesses to Meet PDPL’s Technical and Security Requirements
- What is VAPT?
- Why VAPT is Critical for PDPL Compliance in Saudi Arabia
- How VAPT Maps to PDPL Articles & Requirements
- Running VAPT in the Saudi’s PDPL Context
- Why Saudi Businesses Choose VAPT Services for PDPL Compliance
- Best Practices & Frequency for VAPT
- Case Study Demonstrating VAPT Services-Enhanced PDPL Compliance in Saudi Arabia
- PDPL Saudi Arabia FAQs
Why VAPT is Essential for Saudi Businesses to Meet PDPL’s Technical and Security Requirements
With Saudi Arabia tightening the belt on managing and securing sensitive personal data, this surely calls for robust technical and security measures adoption to curb unauthorized access and data misuse to prevent data breaches.
To effectively meet these critical requirements, Saudi business organizations have increasingly resorted to implementing VAPT (vulnerability assessment and penetration testing).
But how does VAPT help fulfil this purpose to make businesses stay compliant with PDPL? Well regarded as the “Cornerstone of Compliance”, it’s VAPT’s proactive aptitude that helps Saudi organizations identify weaknesses within critical systems, applications, and networks.
Read on further to explore how implementing and integrating VAPT can make your business stay protected and compliant with Saudi Arabia’s evolving personal data protection regulations.
What is VAPT?
VAPT, an advanced cybersecurity method, is a comprehensive security testing approach that combines vulnerability assessment (VA) and penetration testing (PT).
- Vulnerability Assessment: Involves identifying, assessing, and addressing potential security vulnerabilities by utilizing automated tools.
- Penetration Testing: Takes a manual testing route to simulate real-world attacks.

Both vulnerability assessment and penetration testing are complementary to each other despite their specific security testing features, for they work together to strengthen an organization’s security posture.
In short, vulnerability assessment helps identify inherent security weaknesses, but penetration testing goes a step further to confirm the exploitability of those flaws.
VAPT, through these security testing processes, allows Saudi businesses to better understand where they stand in regards to their security posture.
Why VAPT is Critical for PDPL Compliance in Saudi Arabia
Gone are the days when achieving compliance merely meant ‘ticking’ boxes one after the other.
With cybersecurity threats relentlessly surging across the globe and checkbox practices becoming rather obsolete, regulatory frameworks like Saudi’s PDPL are increasingly demanding validated security practices.
These, besides delivering measurable outcomes, should be continuous enough to determine real-time visibility, thereby improving audit-readiness for security and compliance. Ongoing security assessments with VAPT remarkably fulfils this requirement.
The proactive nature of VAPT allows businesses to identify and mitigate potential security vulnerabilities. A tactical, yet prudential approach, VAPT effectively prevents data exposure and compliance breaches associated with that. Regular VAPT analysis allows Saudi businesses to improve their overall security posture and strengthen their chances for achieving PDPL compliance through confidently preparing for security and compliance audits.
Also Read : Recent Amendments to Saudi Arabia’s PDPL: What Businesses Need to Know
Lastly, and most importantly, Saudi’s PDPL mandatorily requires businesses to implement proper technical and security controls for safeguarding personal data. Here again, VAPT’s effectiveness in aptly validating the same deserves a good deal of appreciation.
It was after a one-year transition period that the PDPL became fully enforceable on 14 September 2024. It exists as a comprehensive data privacy law designed to protect personal data of Saudi Arabian citizens. A key factor in driving the Kingdom’s Vision 2030 goals, PDPL imposes fines up to SAR 5,000,000 and possible imprisonment (up to 2 years) if organizations fail to abide by its rules. Violations also include unlawful disclosure of sensitive data knowingly or unknowingly.
How VAPT Maps to PDPL Articles & Requirements
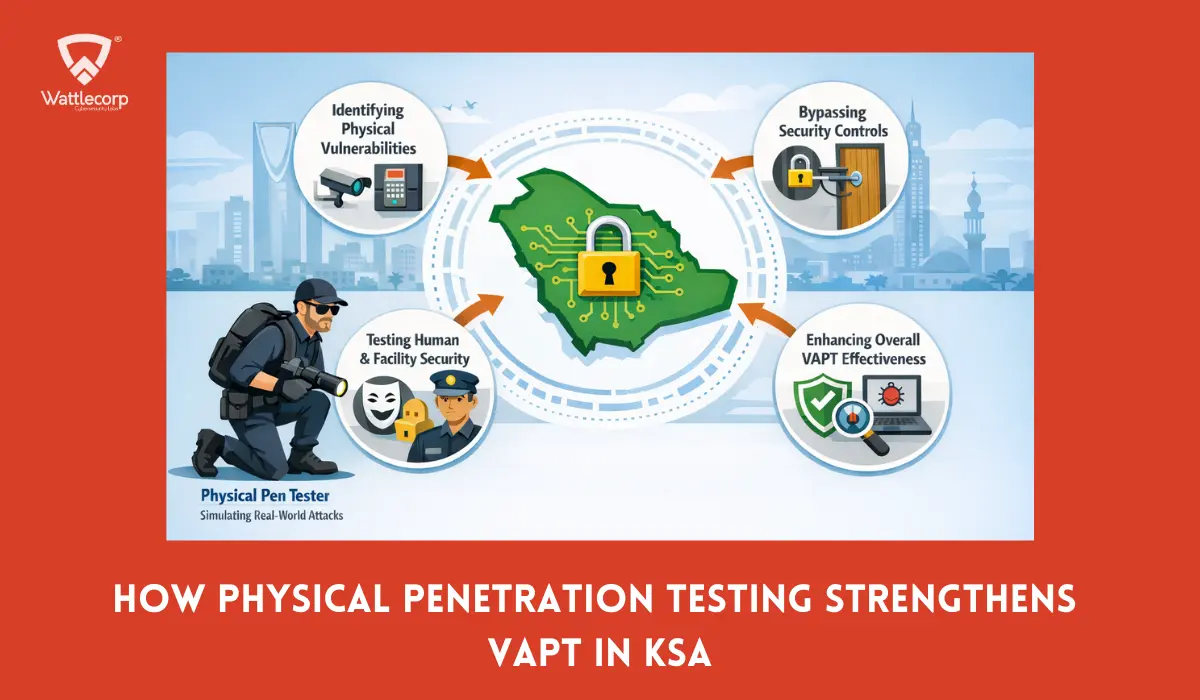
Understanding VAPT’s pivotal role in validating the Saudi’s PDPL-enforced technical and security measures, we now move forward to learn how VAPT maps to PDPL’s specific articles and requirements.
Under the PDPL, Saudi businesses should exercise strict personal data confidentiality, integrity, and availability. This is critical as far as protecting its citizens’ data is concerned. Henceforth, the law demands robust technical, organizational, and administrative measures for this purpose. When aligning VAPT’s core objectives directly with PDPL, this should effectively safeguard personal and sensitive data.
VAPT integration simulates real-world cyberattacks to uncover hidden vulnerabilities and gauge their level of exploitability. This helps businesses determine whether or not the technical safeguards implemented can effectively provide resilience against potential threats and attacks.
PDPL’s mandate on “technical measures”
PDPL in Saudi highly necessitates adopting appropriate technical and organizational measures to safeguard personal data. Key requirements entail:
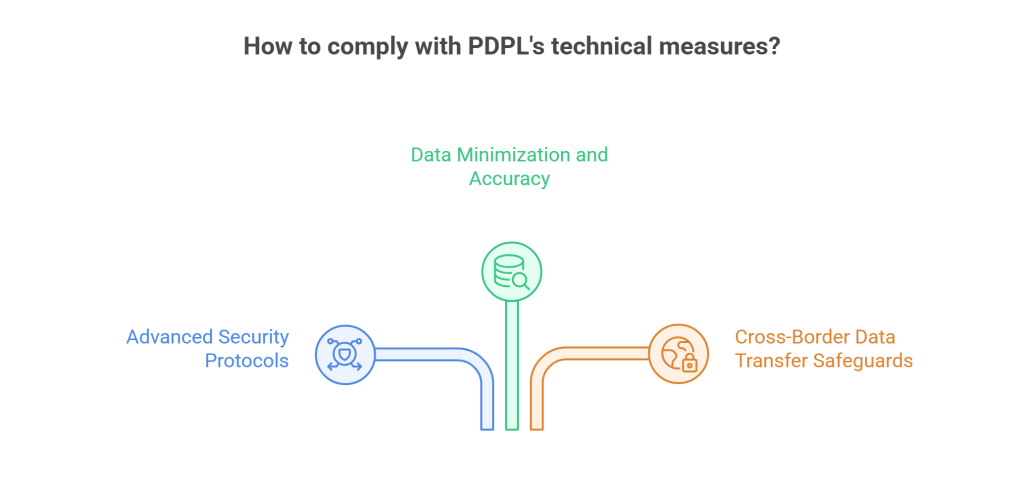
- Establishing advanced security protocols
- Enforcing data minimization and accuracy
- Implementing safeguards for data transfers across borders.
Apart from this, it would also be worth undertaking regular risk assessments and maintaining records of their processing activities for compliance demonstration.
Cross-boundary transfer and encryption
Cross-boundary data transfers In Saudi Arabia undergo strict PDPL scrutiny with robust safeguards by way of encryption and mandatory risk assessments.
VAPT integration with mapping proves considerably helpful for organizations in demonstrating compliance through a proactive security strategy to identify and mitigate security weaknesses.
Encryption on the other hand is the fundamental security control placed for cross-border data transfers as part of the technical measure requirements of PDPL for data protection.
It is the SDAIA (Saudi Data and Artificial Intelligence Authority) that exclusively oversees cross-border data transfer policies and requirements of Saudi’s PDPL. The PDPL instils that data protection during data flows shouldn’t be any less than what it offers.
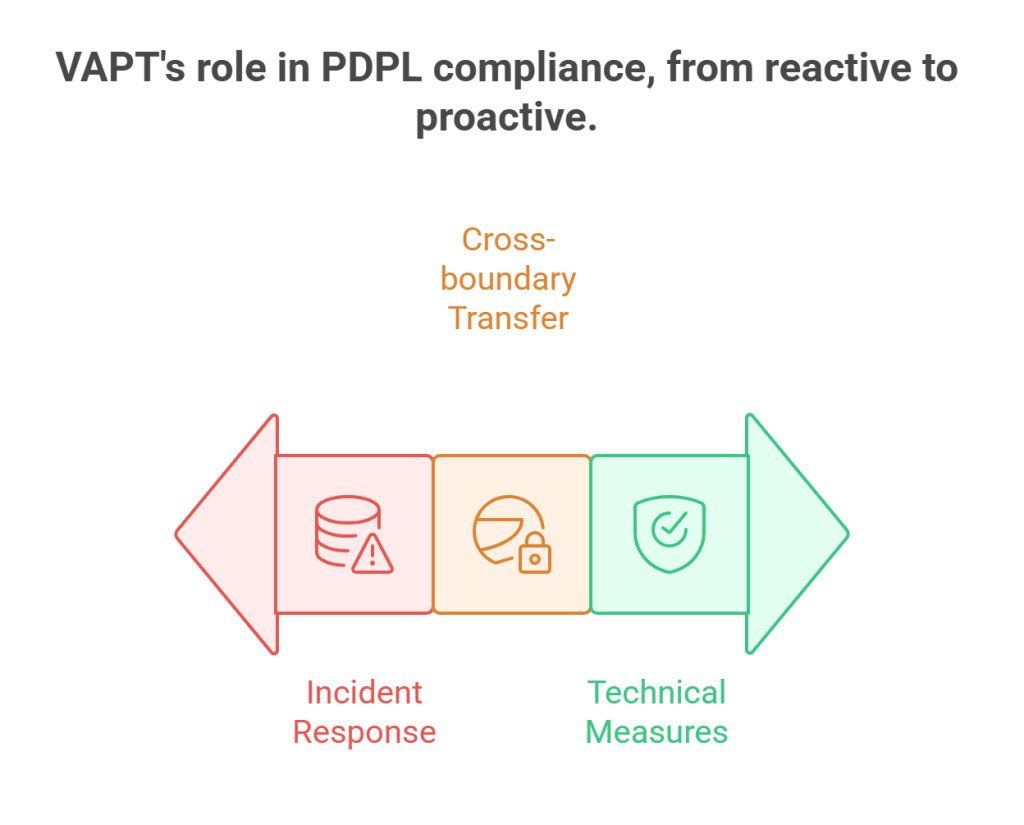
Breach detection & incident response
The PDPL for Saudi organizations entails a comprehensive framework for detecting and responding to breach incidents by urgently implementing strong security measures. These include proactive detection and robust response measures to protect personal data.
VAPT mapping in these scenarios helps monitor the mandatory security controls and practices that the PDPL framework emphasizes.
Running VAPT in the Saudi’s PDPL Context
Vulnerability assessment and penetration testing under the Saudi’s PDPL context has been recognized as a vital and more so, mandatory security protocol for safeguarding personal data.
This protocol is chiefly meant for organizations that collect, handle (process), and store Saudi citizen’s personal data.
However, these should take into account the below-mentioned aspects when implementing VAPT into your organizational processes.
Regulatory considerations & local constraints
VAPT incorporation into Saudi-based business is governed by a series of complex regulatory frameworks and systems that include cybersecurity controls, data protection laws, and sector-specific requirements.
While the frameworks mostly cover SAMA (Saudi Arabian Monetary Authority) and CMA (Capital Market Authority).
With the National Cybersecurity Authority (NCA) and the Saudi Data & Artificial Intelligence Authority (SDAIA) primarily overseeing all these requirements, specific local constraints also exist therein. These are the strict data residency requirements that determine how VAPT security assessment should be performed.

VAPT scope: Systems, Apps, and Infrastructure
Aligning VAPT scope with Saudi Arabia’s PDPL majorly involves prioritizing on securing personal data in all confidentiality and privacy.
Note that a well-structured VAPT scope is primal to integrating it into PDPL compliance requirements. This specifically takes into account prompt identification, assessment, and addressing of vulnerabilities to prevent breach incidents manifested as unauthorized access, sensitive data disclosure, or personal data abuse.
The knowledge that data breach can affect your systems, applications, and infrastructure anytime mandates you to undertake regular VAPT checks embedded into compliance frameworks.
Reporting, evidence, and remediation
The VAPT process, when complying with Saudi Arabia’s PDPL, should consider offering a thorough documentation of evidence.
This, no doubt, requires preparing a clear and structured report that provides actionable insights for remediation, backed by a robust plan.
VAPT procedures should sync with PDPL’s core principles to help Saudi businesses successfully comply with data protection regulations. From mapping to execution, VAPT enables organizations to become compliant through enhanced personal data security throughout its lifecycle.
Why Saudi Businesses Choose VAPT Services for PDPL Compliance
VAPT services in Saudi Arabia are directly linked with attaining PDPL compliance.
It’s obvious that the core purpose of VAPT is to proactively identify and mitigate security flaws before they turn into real threats for hackers to exploit.
However, VAPT services are not confined to ensure security, for they also have been recognized to help meet Saudi-based strict regulatory requirements like NCA ECC, SAMA CSF, and PDPL.
This statement naturally ties with selecting the right VAPT provider for both securing Saudi businesses and making them audit ready for PDPL compliance.
Prioritizing vendors in this regard depends on the key criteria they meet to help organizations achieve compliance. Here are those for your quick reference:
Proven track record of local regulatory knowledge
An ideal VAPT professional protecting critical data should also possess expert knowledge and experience in handling relevant data protection frameworks like the PDPL, Saudi Central Bank (SAMA) Cybersecurity Framework (CSF), and National Cybersecurity Authority’s (NCA) Essential Cybersecurity Controls (ECC), etc.
VAPT assessment goes beyond the technical know-hows of identifying and mitigating risks to offer compliance-specific solutions to businesses operating in Saudi Arabia. This means aligning with the aforementioned regulations issued by the NCA.
Technical Expertise
Judging the technical process of a VAPT provider is highly crucial to obtain expert VAPT solutions. This is specifically important given the cyber risk-prone country or region they’re serving.
This means appointing certified VAPT professionals who can translate advanced technical knowledge to practical insights through a compliance-driven approach. These should go well with a profound understanding of industry-specific cybersecurity practices, not to exclude the compliance factor therein.

Consultative, Compliance-First Approach
Businesses in Saudi Arabia should highly consider adopting a consultative, compliance-first approach when choosing a VAPT (Vulnerability Assessment and Penetration Testing) provider.
This is crucial, especially regarding the ability to navigate the evolving regulatory landscape in the Kingdom along with managing sophisticated cyber threats. A criterion like this stresses the need to adhere to the relevant regulatory frameworks like the PDPL to attain a strategic security partnership.
Best Practices & Frequency for VAPT
The frequency and best practices for VAPT in Saudi Arabia are largely determined by the regulatory frameworks introduced by the NCA and the SAMA. Organizations must also consider their specific risk profile, especially those operating within critical sectors and are largely dealing with personal data processing.
Among these regulatory standards, PDPL is one that doesn’t mandate any specific frequency to undertake VAPT assessments. However, it does lay forth requirements for organizations to implement strong technical security measures for protecting sensitive personal data.
VAPT felt critical to fulfil these purposes simultaneously demands instilling best practices therein.
Without any further delay, let’s go through them in hopes of improving VAPT outcomes.
VAPT Frequency
- VAPT Frequency for Critical Sector: For healthcare and BFSI, consider undertaking VAPT on a quarterly or bi-annual basis.
- Annually: For those operating within non-critical sectors, annual VAPT (at least) would suffice to maintain continuous security.
- Additional VAPT: This is applicable for organizations that have or are planning to undertake major changes, such as deploying a new application, updating systems that are critically required, etc.
- Immediate VAPT: This is required when businesses face major data breach incidents. Immediate VAPT becomes critical to quickly identify and fix hidden vulnerabilities therein.

VAPT Best Practices Adhering to PDPL Compliance
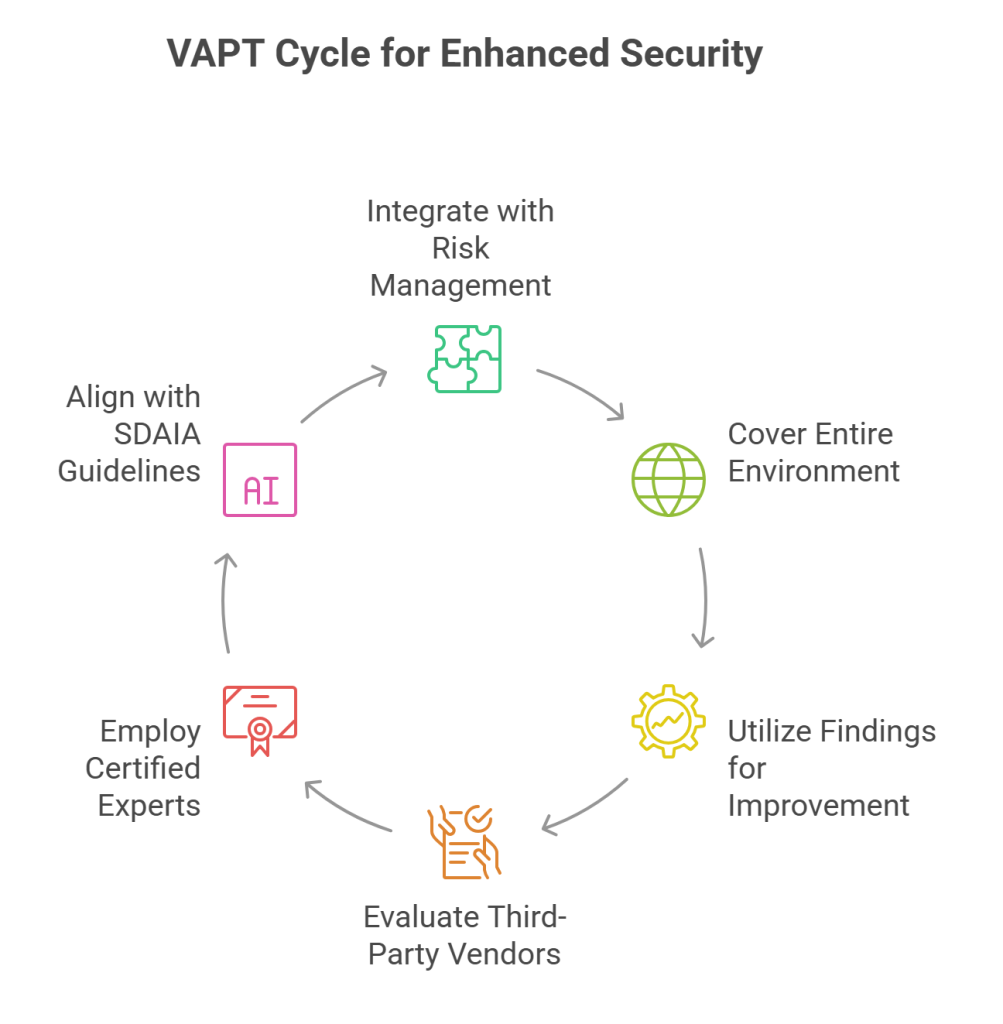
- Risk Management-Integrated Approach: VAPT outcomes serving risk management strategies are the ones that create value for organizations that implement vulnerability assessment and penetration testing to improve their security posture.
- Covers Entire Processing Environment: VAPT scope should broadly cover every aspect of your management. This spans systems and applications that exclusively handle data processing, storing, and transfers. Network infrastructure, mobile and web applications, and third-party systems are also included in there.
- Utilizing Findings for Continuous Improvement: Requires implementing processes that helps with regular reviewing based on findings from VAPT. Efforts like this help improve security control strength and effectively train employees while regularly updating internal policies.
- Evaluating Third-Party Vendors: With organizations held liable or answerable for third-party breaches, VAPT’s intervention in auditing vendors and suppliers can prove truly beneficial in ensuring that the latter is adequately maintaining (managing) data protection measures.
- Employ certified VAPT Experts: It’s always advisable to hire qualified VAPT professionals. Their expertise in solving security-borne issues combined with their knowledge on applicable compliance frameworks can effectively help businesses safeguard their critical assets and data from the clutches of cybercrime.
- Aligning with SDAIA Guidelines: A VAPT provider should make it a point to align their services to relevant regulatory standards and guidelines set by SDAIA, especially when it concerns safeguarding critical personal data.
Under Article 30 and rules published Aug 2024, certain organizations are required to appoint a Data Protection Officer (DPO) under PDPL.
Case Study Demonstrating VAPT Services-Enhanced PDPL Compliance in Saudi Arabia
The below case study depicts how implementing VAPT aligned with PDPL helped companies attain and maintain security-embedded compliance.
Case Study: How a Healthcare Startup in Saudi Arabia Attained PDPL Compliance With VAPT
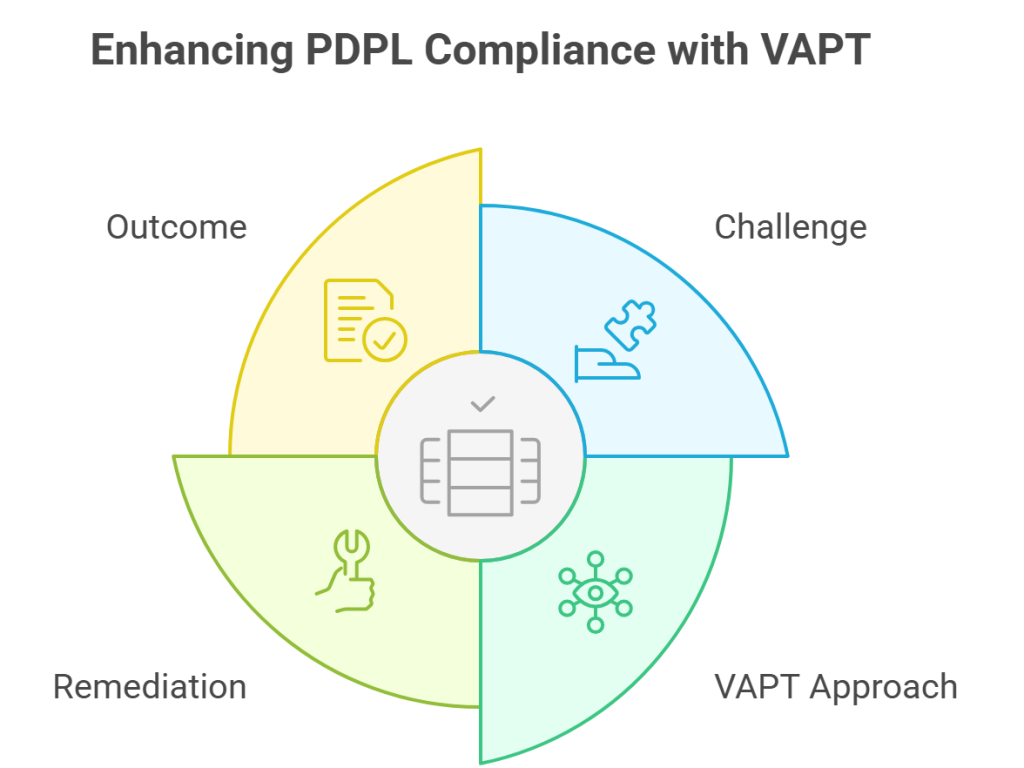
The Challenge: A healthcare startup needing to maintain compliance with PDPL was struggling with effectively handling large chunks of personal data for their patients.
Demonstrating adherence to Personal Data Protection Law felt highly challenging in this regard, for ensuring patient data protection was crucial, failing which will invite penalties, financial loss, and reputational damage.
Also Read : Navigating Saudi Arabia’s Personal Data Protection Law (PDPL ): Key Compliance Requirements for Businesses
VAPT Approach and Implementation
Primarily involved VAPT scoping with the hospital’s DPO,and vendors to map data flows and high-risk systems, including patient portal, connected devices, and API gateway.
A risk-prioritized testing followed that comprised external web application and authenticated API tests with internal network and simulated phishing to test staff controls.
Each VAPT finding was mapped to the PDPL control objective with Red Team handling high-risk vulnerability detection and mitigation, validating the same. This also included improving incident response, with findings ranging from unauthenticated API endpoint to gaps in logging, slowing down breach detection.
VAPT Remediation with PDPL Alignment
VAPT remediation for vulnerabilities involved immediate API fixes, such as limits, enforcing multi-factorial authentication and reduced session lifetimes, and improved logging with SOC alerts for key events like data export.
The idea was to meet PDPL breach response expectations with guidance to implement organizational and technical measures to confirm remediation and retest the results.
The Outcome
With no remaining critical issues found upon remediation confirmation, the PDPL-mapped control matrix was submitted to the regulator for audits.
The concerned healthcare facility was eventually able to improve its breach prevention time, also demonstrating improved technical measures, going by PDPL compliance expectations.
The ultimate result was a substantial reduction in non-compliance risks, financial and legal. This was borne from the technical measures implemented to acquire improved security posture and compliance status.
VAPT is not a standalone activity, but an ongoing process that is part and parcel of a comprehensive security management program.
Considering vulnerability assessment and penetration as a mere checkbox routine is one major mistake you will make as a business. Especially in an era that is marked by digital evolution and simultaneously emerging threats manifested as security vulnerabilities.
Saudi Arabia, a Middle-East land abound with stringent cybersecurity and data protection frameworks like PDPL, NCA, SAMA, etc., emphasizes why it’s critical to abide by these standards to protect personal or sensitive data in the first place.
Where compliance with these regulations highly matters, so does ensuring data protection, especially for critical sectors like BFSI and healthcare that largely deal with handling, storing, and transferring data.
Among the existing and renowned VAPT service companies in the Kingdom, Wattlecorp has been recognized as outstanding. This is particularly true in terms of delivering compliance-driven VAPT assessment services if you’re one operating in Saudi Arabia. Whether you want your API or mobile/application security tested, we’ve got you covered in all these aspects.
Our VAPT services extend past assuring you optimum security,. As a cybersecurity team, we help you navigate the strict, yet evolving Saudi-based regulatory standards. Our PDPL compliance services stem from our knowledge that ensuring data protection is crucial for business continuity and growth. Based on this understanding, our solutions are bound to make you confident and audit-ready every time.
Any queries related to your data protection and compliance needs and how we help you achieve and retain the same, visit our web page, PDPL in Saudi Arabia for more information.
Boost your audit-readiness with Wattlecorp’s VAPT-embedded compliance solutions.
PDPL Saudi Arabia FAQs
1.What is VAPT and how does it relate to PDPL compliance?
Acronym for Vulnerability Assessment and Penetration Testing, is an advanced security testing method that helps organizations in Saudi Arabia identify and address security vulnerabilities before these lead to data breaches. This proactive feature of VAPT can substantially lead to both achieving and retaining PDPL compliance that demands robust data protection as felt appropriate in the Saudi regulatory context.
2.Who must perform VAPT under the Saudi PDPL?
Every public and private organization operating in Saudi Arabia exclusively handling personal data should perform VAPT as per Saudi’s PDPL mandates. This helps ensure appropriate security measures are in place as well as ascertain personal data protection during cross-border transfers.
3.What are the technical measures required by PDPL that VAPT helps validate?
VAPT helps validate the following technical requirements under the PDPL mandates:
● Access control systems: Help ensure that only authorized users can access personal data. VAPT validation for this purpose involves checking for weak credentials, reviewing RBAC (role-based access controls), and testing whether multifactorial authentication mechanisms are aptly implemented or not.
● Application and Network Security: Under PDPL, VAPT directly examines the overall security posture of an organization. These cover web application security, cloud security, and network security.
● Breach detection and incident response: As per the robust breach notification procedure mandates of the PDPL, VAPT helps validate systems supporting such a requirement through attack simulation and network segmentation evaluation.
● Encryption: This is required when personal data is transmitted across borders.
4.How often should we undertake VAPT for PDPL compliance?
The PDPL in Saudi Arabia does not recommend any definite frequency. However, as strict as it is to safeguard personal data, businesses, especially those collecting, processing, storing, (and data transmission) to an extensive degree, regularly undertake VAPT would be more appropriate.