Key Takeaways:
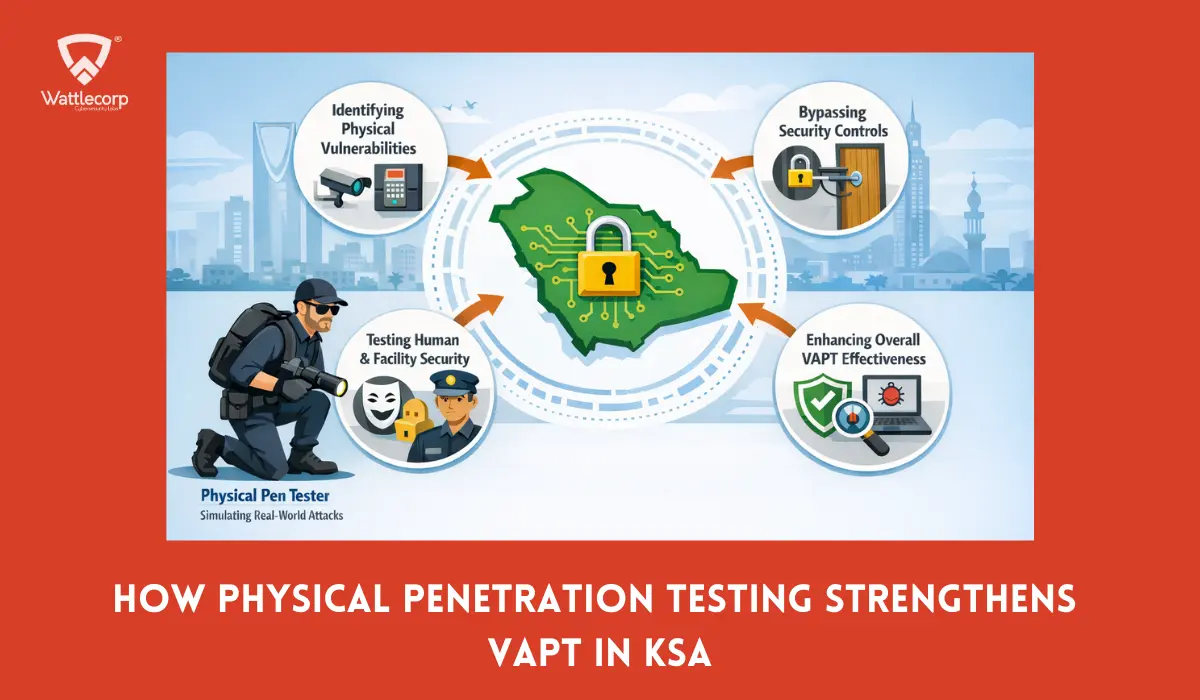
- Physical penetration testing identifies security vulnerabilities in physical access controls that cyber-focused VAPT cannot detect, and it provides actionable methods for preventing unauthorized physical access to facilities, which helps stop attackers from gaining direct access to network infrastructure or data centers.
- The physical vulnerabilities quickly lead to cyber breaches, threatening BFSI, SaaS, and healthcare operations with data theft and downtime. The fast infrastructure growth amplifies these dangers across Saudi Arabia.
- Integrating physical security assessment with VAPT ensures full compliance with Saudi Arabia’s NCA ECC, SAMA CSF, and ISO 27001 standards. It provides auditors with clear evidence of end-to-end safeguards.
- Common methods in physical penetration testing like tailgating and lock picking, pair with tools in physical security testing to reveal how physical gaps fuel cyber attacks. These techniques identify overlooked paths to sensitive assets.
- Businesses in Saudi Arabia gain technical advantage by selecting a penetration testing service that offers combined physical security testing with VAPT for defence and local expertise aligns the tests with regional regulations and threats.
Table of Contents
Toggle- Why Physical Security Matters in Cybersecurity
- What Is Physical Penetration Testing and Why It Matters for Cybersecurity
- How Physical Vulnerabilities Lead to Cyber Breaches
- Integrating Physical Penetration Testing with Cyber VAPT
- Common Physical Weaknesses Found in Saudi Organizations
- Why Saudi Firms Must Meet NCA, SAMA & ISO 27001 Standards
- Benefits of Combined Physical–Cyber VAPT
- How to Choose a Penetration Testing Service in Saudi Arabia
- Case Examples
- Integrate Physical and Cyber Testing for Complete Security
- Physical Penetration Testing FAQs
Why Physical Security Matters in Cybersecurity
Major cyber breaches often start with a simple oversight, not with malware but with a badge swipe, a propped door, or a tailgater who should never be inside.
Physical security testing helps reveal these weak entry points before attackers turn them into digital compromise using physical penetration testing.
In sectors like BFSI, SaaS, and healthcare across Saudi Arabia, the SOC team assists to monitor networks relentlessly while physical access remains under-tested, which leaves critical assets, data, and systems exposed.
Therefore, penetration testing services help to identify and fix these hidden physical gaps and at the same time provide strong cyber defenses for complete protection.
This blog explains how physical security testing guides to stop attackers early, before they can turn a small weakness into a major breach.
What Is Physical Penetration Testing and Why It Matters for Cybersecurity
Do you know how physical security vulnerabilities affect cyber security?
Physical security and cybersecurity are interconnected; each enhances the other to prevent attackers who take advantage of both areas simultaneously.
Physical penetration testing is more like a controlled attempt to breach physical security testing controls, using real-world tactics to reach sensitive locations, devices, and information.

In order to determine how quickly an attacker might jump into networks, professionals may imitate attackers during physical penetration testing by tailgating, lock picking, RFID cloning, or exploiting unsecured systems.
Physical security testing for offices, branches, and data centres for Saudi Arabian organisations shows how physical vulnerabilities impact cyber security and how physical penetration testing enhances VAPT results in real-world scenarios.
How Physical Vulnerabilities Lead to Cyber Breaches
Physical security testing checks doors, cameras, guards, ID badges, and how people act on site. But any flaw found in physical penetration testing can give attackers a way into your digital systems.
An unlocked server room, open network plug, or empty computer with high access often starts data theft, jumping between systems, or taking over the whole network.

CISA says physical protection must guard people, gear, and supplies. In Saudi Arabia, this matters more as key systems go digital.
Therefore, it is essential to know how physical checks differ from VAPT supports to build stronger, step-by-step protection. It ensures both digital and physical protection.
Integrating Physical Penetration Testing with Cyber VAPT
Combining physical security testing with VAPT provides a complete view of how attackers progress from physical entry to network domains.
Physical penetration testing proves if firewalls, alerts, and locked devices fail once someone’s inside with access to cables, ports, and machines.
Also Read : Top Penetration Testing Methodologies to Protect Your Business
For Saudi Arabia organizations, integrating the combination of both physical penetration testing and VAPT demonstrates how physical vulnerabilities impact cybersecurity and tests if monitoring, segmentation and identity controls resist blended attacks.
Common Physical Weaknesses Found in Saudi Organizations
Physical security testing across Saudi Arabia frequently identifies the recurring gaps that physical penetration testing can exploit with minimal tools.
The most common weaknesses include poor visitor checks, unlocked or empty workspaces and weak outer defenses.

- Poor visitor checks: Shared badges, unchecked guests and slipping into secure areas unnoticed.
- Unlocked or empty workspaces: Open computers, printed papers and marked cabinets easy to steal from.
- Weak outer defenses: Hidden camera blind spots, held-open emergency doors and unwatched loading areas that attackers use for secret entry.
These physical security testing findings ties in Saudi Arabia’s fast growth under Vision 2030, where new buildings open before safety rules catch up.
Why Saudi Firms Must Meet NCA, SAMA & ISO 27001 Standards
In Saudi Arabia, physical security testing goes beyond best practices, it ensures to meet key regulations.
The NCA ECC Framework requires strong physical access controls as a core part of national cybersecurity. And the SAMA’s Cybersecurity Framework includes physical and environmental security for banks and financial firms.
Also Read : Integrating GRC with SAMA & NCA Frameworks: A Holistic Approach for Saudi Enterprises
ISO 27001 views physical penetration testing and site controls as essential to overall information security. Companies integrating VAPT must also show their physical protection work can be checked and watched closely.
Benefits of Combined Physical–Cyber VAPT
When physical security testing works together with cyber VAPT, company leaders get a clearer and more real-world understanding of how attackers move and succeed.
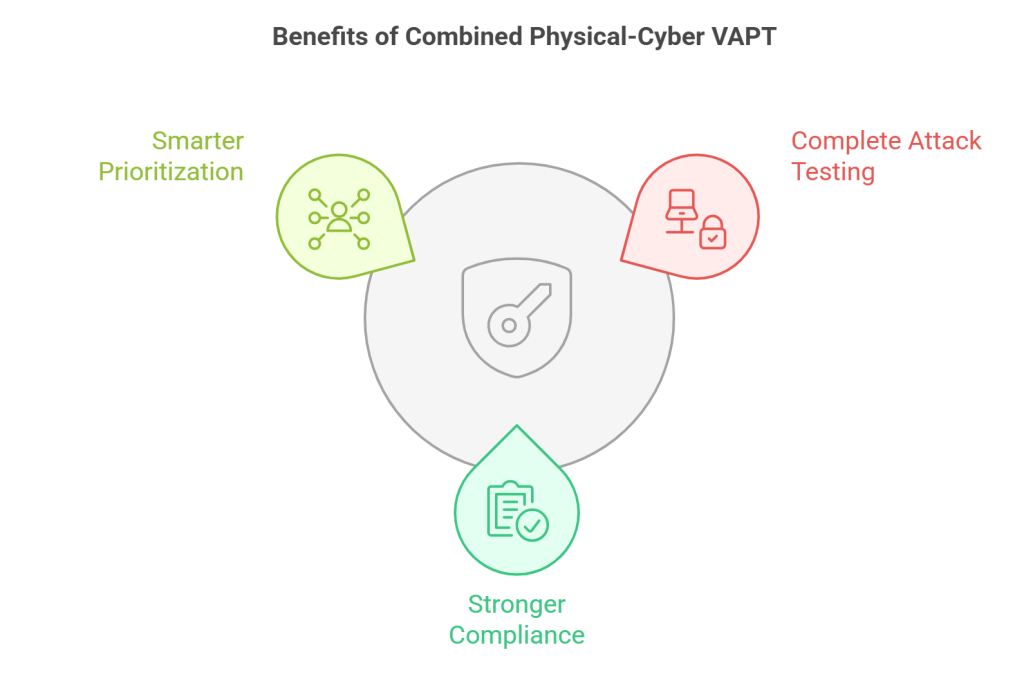
The key benefits of combined Physical– VAPT include:
- Complete attack testing that fully links bypassing doors, gaining access to devices and exploiting networks for a realistic end-to-end simulation of threats.
- Stronger compliance with NCA, SAMA, and ISO 27001 rules, especially vital in highly regulated Saudi Arabia sectors like banking, financial services, insurance (BFSI) and healthcare.
- Smarter prioritization of fixes, as teams clearly see how physical weak spots impact cyber security and identify which vulnerabilities offer attackers the quickest path to major damage.
How to Choose a Penetration Testing Service in Saudi Arabia
Choosing the right partner for physical security assessments in Saudi Arabia demands more than just a standard hacking expertise.
The organizations need assessors with the knowledge of the local regulations, building standards, and those of the industry with the NCA ECC, SAMA CSF, and Vision 2030 infrastructure initiatives.
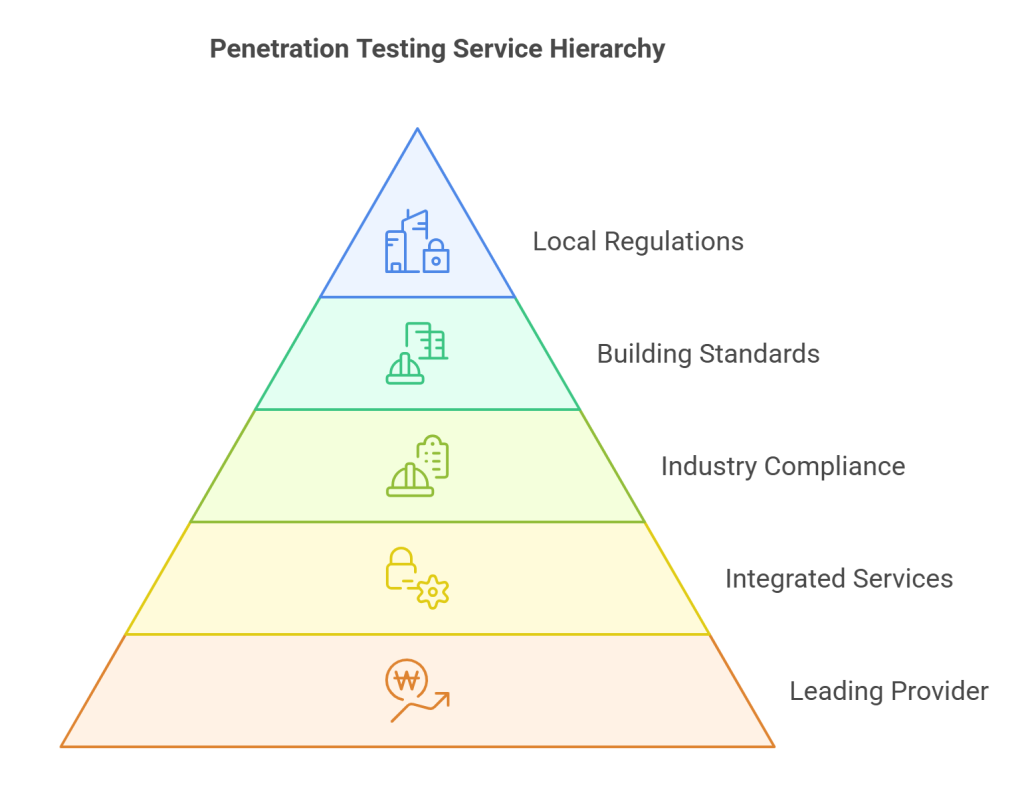
Wattlecorp has been a leading provider of the best penetration testing service in Saudi Arabia, the integrated Penetration Testing alongside VAPT and the physical penetration testing.
Our strategies, techniques and assess reports to local situations, which will allow Saudi businesses to put into practice findings as opposed to completing audit requirements.
Case Examples
Case Study 1: Saudi Data Center
Testers would pass right behind employees who were walking through the doorway into the loading area without being noticed and proceed directly to an unsecured network shelf space and attach a fake device to gain access to the door. The fake attackers rushed directly into key control networks that were initially said to be perfectly safe and harmless by the past VAPT tests.
Key Result: Lock up shelves, install special doors where no one could follow behind, have cameras that were on 24/7 to monitor everything and hands on training to all workers which wiped out every threat of total system break-in in the normal daily critical operations.

Case Study 2: Banking Branch
The testers found a misplaced entry card right next to an unlocked computer workstation location, which made it easy to steal login information, which had eluded firewalls, warning alert systems and additional login procedures.
Key Result: Implemented trackers to never lose a card, self-locking screen after only half an hour of inactivity, daily inspections of all the cards, and comprehensive logs of every door entry to ensure no important customer data is stolen in some surprise inside attack or some follow-behind trickiness when adhering to the strict regulations of the bank.
Integrate Physical and Cyber Testing for Complete Security
Cyber incidents in Saudi Arabia increasingly combine physical and digital tactics, making isolated VAPT insufficient without robust physical security testing.
By adding Wattlecorp’s physical penetration testing to existing VAPT programmes, organisations reduce the chances that a single door, card, or workstation becomes the silent start of a major breach.
For leaders accountable to NCA, SAMA, and ISO 27001, integrated testing also simplifies evidence gathering for audits while strengthening everyday resilience.
Choose your penetration testing assessment with Wattlecorp today and align physical security testing and Penetration Testing with VAPT into one coordinated defence across Saudi Arabia.

Physical Penetration Testing FAQs
1.What is physical penetration testing and how does it work?
Physical penetration testing is a controlled attempt to bypass locks, badges, guards, and surveillance to reach sensitive areas or devices. It uses real-world techniques to evaluate whether physical security testing measures can stop intruders before they trigger cyber impact.
2.Why should Saudi organizations integrate physical testing with VAPT?
In Saudi Arabia, many risks emerge when attackers move from physical access to digital systems. Integrating physical security testing, physical penetration testing, and Penetration Testing with VAPT ensures that compliance, infrastructure growth, and operational realities are tested as one continuous attack path.
3.What are the common vulnerabilities found during physical security assessments?
Typical findings from physical security testing include weak visitor controls, unattended workstations, unsecured server rooms, and blind surveillance spots. Physical penetration testing often shows how these gaps allow intruders to steal credentials, plant hardware, or access internal networks.
4.Does NCA or SAMA require physical security controls?
Yes, Saudi Arabia’s NCA ECC and SAMA Cybersecurity Framework both include requirements around physical and environmental security. Physical security testing and physical penetration testing help demonstrate that access control, monitoring, and facility safeguards work in practice, supporting audit readiness.
5.How do companies select the right penetration testing service in Saudi Arabia?
Organisations should seek providers with proven physical security testing and VAPT experience, plus knowledge of NCA, SAMA, and local regulations. A partner skilled in physical penetration testing within Saudi Arabia can design realistic scenarios aligned with sector risk, not generic checklists.