Key Takeaways:
- Compliance with cybersecurity in the UAE has been elevated to the board level because of the high breach rates and stringent regulation practices.
- The interpretation of the relevant frameworks, such as PDPL, NESA/SIA IAS, DIFC/ADGM laws, and ISO 27001 clarifies the actual range of compliance requirements.
- Business cases succeed when cybersecurity risk is expressed in financial, regulatory, and revenue impact terms rather than technical language.
- An organised and systematic approach will allow UAE organisations to defend and gain board support on compliance investments.
- Cybersecurity compliance is a continuous commitment that requires sustained investment. Boards must recognize the long-term nature of cybersecurity efforts, ensuring consistent protection against evolving threats and regulatory changes.
Table of Contents
Toggle- Why UAE Businesses Can No Longer Treat Cybersecurity Compliance as Optional
- The UAE Cybersecurity Compliance Landscape in 2026
- Why Most Business Cases for Cybersecurity Fail and How to Avoid It
- Step-by-Step: How to Build a Cybersecurity Compliance Business Case in UAE
- Cybersecurity Compliance Checklist for UAE Companies
- How VAPT Strengthens Your Cybersecurity Compliance Position in the UAE
- How Wattlecorp Helps UAE Businesses Build and Execute a Compliance Strategy
- Turn Compliance From a Checkbox into a Competitive Advantage
- Cybersecurity Compliance FAQs
Why UAE Businesses Can No Longer Treat Cybersecurity Compliance as Optional
A single cyber breach can create immediate financial, operational, and regulatory consequences for an organization.
According to the IBM Cost of a Data Breach Report 2024, the average cost of a data breach in the Middle East is estimated at USD 8.75 million (approximately AED 32 million) per incident covering investigation, containment, system recovery, and business disruption.
This figure does not include potential regulatory penalties, licensing restrictions, legal claims, or the long-term reputational damage and customer attrition that often follow a major security incident.
The PDPL (Personal Data Protection Law) penalties relate specifically to non-compliance in areas such as breach notifications, lawful processing, and data subject rights violations.
NESA/SIA (Signals Intelligence Agency) enforces compliance for critical infrastructure with penalties tied to sector-specific requirements.
Enforcement of PDPL violations can involve financial penalties, corrective action orders, and potentially operational restrictions, with the severity of the penalty dependent on the nature of the violation, such as missing breach notification deadlines or failing to protect personal data.
Most UAE executives already know cybersecurity matters. What they can’t figure out is how to make a compelling case for investment when competing with a dozen other budget priorities.
The IT team speaks in CVEs (Common Vulnerabilities and Exposures) and control domains. The board speaks in dirhams and risk exposure. Those conversations rarely go well without a bridge.
A practical, board-ready cybersecurity compliance business case framework written specifically for how UAE companies actually operate. You can start using it this quarter.
The UAE Cybersecurity Compliance Landscape in 2026
If you haven’t reviewed your regulatory obligations recently, there’s a good chance your picture is already outdated. The cybersecurity compliance environment across UAE has changed considerably, and the direction of travel is tighter enforcement, not looser.
Here’s where most organizations need to focus:
- UAE PDPL is the federal baseline for personal data protection, requiring lawful processing and breach reporting within timelines defined by the Executive Regulations, and requiring a Data Protection Officer when processing meets specific high-risk thresholds.
- Data Protection Laws, DIFC and ADGM (Abu Dhabi Global Market) have separate data protection regimes for entities operating in those financial free zones, and some groups can face overlapping compliance obligations depending on entity structure and where processing occurs.
- ISO 27001 is not a UAE statute, but it is frequently used as the default evidence standard in enterprise procurement and vendor due diligence across the UAE.
- NIST Cybersecurity Framework, NIST-based approaches are commonly used alongside ISO 27001 in UAE GRC programs, and the UAE IA Regulation itself cross-references NIST publications in its control mapping context.
Knowing which of these apply to your specific structure and in what combination determines the entire scope of your cybersecurity compliance program. Get this wrong and you’ll either over-invest in areas that don’t matter or leave genuine gaps that auditors will find.
Why Most Business Cases for Cybersecurity Fail and How to Avoid It
Security teams lose budget battles for a few consistent reasons, and they’re worth naming directly.
- The first is leading with technology. Boards don’t fund firewalls; they fund risk reduction. When a CISO walks into a board meeting and starts explaining threat vectors and patch cycles, the room checks out within five minutes.
- The second is skipping the cost-of-doing-nothing calculation. Every cybersecurity compliance investment proposal needs to answer a simple question before anything else: what is this organisation’s financial exposure right now, today, if we change nothing? Without that anchor, any spend figure sounds arbitrary.
- Third and this one kills more proposals than anything else is presenting compliance as a project with an end date. Boards that have been around long enough know there’s no finish line in security. The better framing is sustained risk management, not a one-time fix.
A board-level cybersecurity compliance justification framework works because it meets executives where they are. Liability.
Regulatory exposure, Reputation, Revenue protection, Contract eligibility. These are the levers that move decisions, and the six-step approach below addresses each of them directly.
Step-by-Step: How to Build a Cybersecurity Compliance Business Case in UAE
Step 1: Define the Regulatory Scope That Applies to Your Organisation
Clarity on which UAE laws and frameworks actually apply to your business is essential. This is where a surprising number of organisations get it wrong either assuming they’re out of scope when they’re not, or preparing for requirements that don’t apply to their sector.
Work through your classification first. Are you a critical infrastructure entity under NESA? A licensed financial institution under DIFC? A general commercial business handling personal data of UAE residents? Each carries different obligations and different risk profiles.
A proper cybersecurity compliance checklist for UAE companies starts here, before any technical assessment begins.
Step 2: Conduct a Risk Assessment and Gap Analysis
A formal risk assessment UAE organisations should conduct here covers your actual security posture controls you have, controls you’re missing, and controls that exist on paper but aren’t functioning as intended.
Map those gaps against control domains and ISO 27001 requirements, then do something that most technical teams skip: translate each gap into a business consequence.
This gap gives an attacker a viable path to our financial systems and exposes sensitive customer financial data to unauthorised access.
Step 3: Quantify the Cost of Non-Compliance
This step is the engine of the entire business case. Regulatory fines under the UAE Information Assurance Regulation can be significant and are determined by sector-specific enforcement mechanisms. PDPL violations carry their own penalty structure. But the fine is often the smallest number in the room.
Add breach remediation costs, legal fees, third-party forensic investigation, customer notification, credit monitoring obligations, and the longer-term revenue impact of damaged client trust. For organisations in regulated sectors, factor in licence complication risk and the cost of emergency consultancy to get back into compliance under pressure.
When you lay all of that out in a single table, the investment case for proactive cybersecurity compliance stops looking expensive. It starts looking rational. That’s the shift you need.
Step 4: Build the ROI Case for Compliance Investment
Here’s where cybersecurity ROI gets interesting. The direct comparison with compliance program cost versus breach cost is powerful on its own. But the indirect returns often end up being just as significant over a 2-3 year window.
Organisations with demonstrable cybersecurity compliance credentials move through enterprise sales cycles faster.
Vendor onboarding that used to take months clears in weeks when your security posture is documented. Government contract bids become accessible in ways they weren’t before. Audit preparation time drops substantially when you’ve been maintaining continuous compliance rather than scrambling every 12 months.
A unified compliance framework built around overlapping controls typically reduces that redundancy. That’s a recoverable budget sitting inside your existing operations.
Also Read : VAPT Metrics That Matter: How to Measure and Report Security Testing ROI to Leadership
Step 5: Map Compliance to Your Business Goals
A cybersecurity compliance program that exists in isolation from the rest of the business will always be a hard sell. Connect it to what the organisation is already committed to achieving.
UAE Vision and the country’s digital economy agenda create real market incentives for security-mature businesses.
Compliant organisations are winning UAE government contracts that non-compliant competitors can’t even bid on. Companies expanding into GCC markets are finding that ISO 27001 certification accelerates partner due diligence significantly.
Reframe the conversation with your board: compliance isn’t a constraint on growth. It’s increasingly a condition for it.
Step 6: Present a Phased Investment Plan
Boards don’t just need to know what you’re asking for, they need to understand what they’re getting and when. A phased approach makes the cybersecurity compliance program feel manageable rather than overwhelming.
Year 1 typically covers gap remediation, closing the most critical control deficiencies identified in your assessment. Year 2 moves into formal certification or regulatory alignment, whether that’s NESA audit readiness, ISO 27001 certification, or both. Year 3 focuses on continuous monitoring, GRC maturity, and embedding compliance into operational processes rather than treating it as a periodic exercise.
Map resource requirements across each phase internal team time, external consulting hours, and tooling. For most UAE businesses, engaging a specialist partner at this stage delivers stronger outcomes than building an in-house GRC team from scratch, and at considerably lower cost.
Cybersecurity Compliance Checklist for UAE Companies
- Identify applicable UAE frameworks- PDPL, DIFC, ISO 27001, and any sector-specific requirements
- Conduct a formal, documented compliance gap assessment against applicable regulatory and contractual control requirements
- Document current security controls versus what’s actually required
- Calculate your total financial exposure from breach and non-compliance scenarios
- Build a side-by-side comparison of compliance investment cost versus risk reduction value
Also Read : Why Managed VAPT Is the Future of Cybersecurity in the UAE: Continuous Testing vs One-Off Audits
- Appoint or designate a Data Protection Officer if PDPL obligations apply
- Establish a board reporting structure for ongoing cyber risk metrics
- Include VAPT as a compliance validation step, not an afterthought
- Build a phased roadmap with milestones the board can track
- Identify a cybersecurity compliance consulting partner to drive faster implementation
How VAPT Strengthens Your Cybersecurity Compliance Position in the UAE
Vulnerability Assessment and Penetration Testing (VAPT) answers a different question than gap analysis alone: not just what controls are missing, but what an attacker could actually do with those gaps today.
That distinction matters enormously in a board presentation. A gap analysis tells you where you’re exposed. A VAPT report shows you what that exposure looks like when someone actively tries to exploit it. Third-party verified findings carry a weight that internal assessments simply don’t.
Also Read : Aligning VAPT Practices with UAE’s Data Protection Regulations
For the practical side of cybersecurity compliance, VAPT outputs feed directly into your risk quantification and remediation planning. They also serve as auditable evidence during NESA assessments and ISO 27001 certification reviews documentation that regulators actually want to see.
Working with a reputable VAPT company in Dubai like Wattlecorp means your testing methodology meets regulatory expectations and the documentation produced holds up during a formal audit, not just an internal review.
How Wattlecorp Helps UAE Businesses Build and Execute a Compliance Strategy
Wattlecorp works with UAE organisations at every stage of the cybersecurity compliance journey from the initial risk assessment and gap analysis right through to NESA alignment, ISO 27001 certification support, GRC program development, and VAPT.
What makes the approach different is integration. Rather than treating each compliance requirement as a separate workstream, Wattlecorp builds unified programs that satisfy multiple frameworks simultaneously, reducing cost and eliminating duplication.
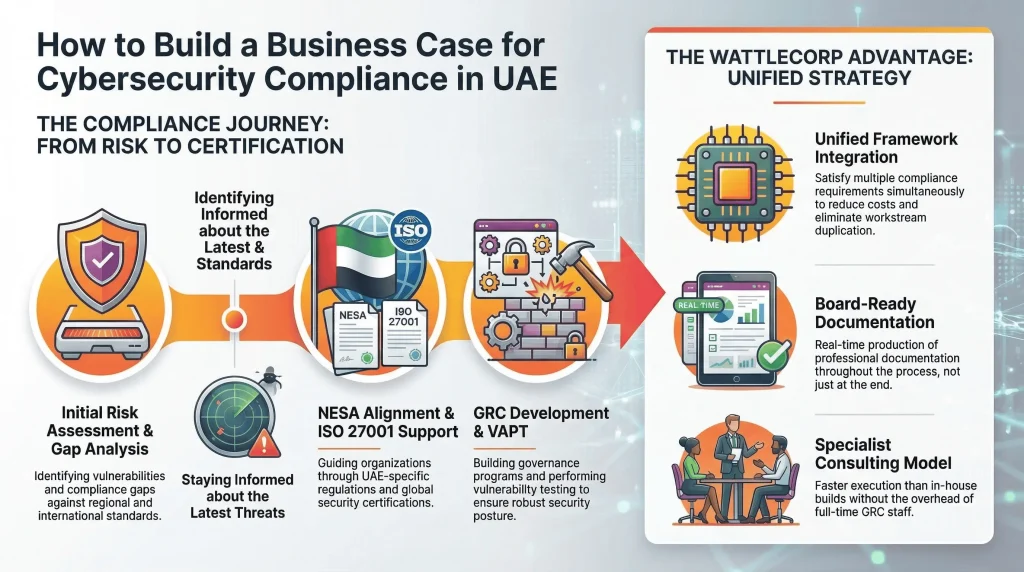
Our team produces board-ready documentation throughout, not just at the end.
For UAE businesses that need to move faster than an in-house build allows, or that want specialist expertise without the overhead of a full-time GRC function, the consulting model delivers both.
Turn Compliance From a Checkbox into a Competitive Advantage
Boards that understand cybersecurity compliance in UAE as purely a cost-avoidance exercise are working with an incomplete picture.
Yes, the fines are real and the breach costs are significant. But the organisations gaining genuine competitive advantage from compliance aren’t doing it to avoid penalties, they’re doing it because a strong security posture opens doors that would otherwise stay closed.
At Wattlecorp, we see this advantage firsthand across UAE organisations that treat compliance as a strategic growth driver rather than a regulatory burden.
The six-step framework here regulatory scoping, risk assessment, non-compliance cost modelling, ROI analysis, business goal alignment, and phased investment planning gives your executive team a structured, credible foundation to make that decision with confidence.
The best starting point is always a cybersecurity risk assessment and gap analysis. It gives you the facts, sets the baseline, and makes every subsequent step easier to justify.
Ready to build your cybersecurity compliance business case? Wattlecorp’s expert team is here to help.
Cybersecurity Compliance FAQs
1. Why is cybersecurity compliance mandatory in the UAE?
UAE regulations including NESA (now operating as SIA) and the PDPL place binding legal obligations on critical sector organisations and businesses that handle personal data. Ignoring these requirements puts organisations at risk of financial penalties, licence revocation, and reputational fallout and UAE regulators have been increasingly active in enforcement.
2. How can UAE businesses justify cybersecurity investment to the board?
The most effective approach ties the investment to numbers the board already cares about: the financial cost of a breach, the scale of potential regulatory fines, the contracts you won’t win without compliance, and the efficiency gains from a properly structured GRC program.
3. What frameworks support cybersecurity compliance in UAE?
The main ones are NESA/SIA IAS for critical infrastructure sectors, UAE PDPL for data protection obligations, ISO 27001 for internationally recognised security management, the NIST Cybersecurity Framework for risk-based governance, and DIFC/ADGM Data Protection Laws for free zone operators. Which applies to your organisation depends on your sector and operating structure.
4. What does a cybersecurity compliance checklist cover?
A cybersecurity compliance checklist ensures adherence to relevant laws, such as PDPL and ISO 27001, by assessing security controls, data protection measures, and incident response plans. It also includes maintaining documentation, ensuring audit readiness, and continuously monitoring security practices for compliance.
5. How does VAPT support regulatory compliance in the UAE?
VAPT goes beyond theoretical gap identification, it tests whether your security controls would actually hold up under attack. The resulting reports give auditors and certification bodies documented evidence of proactive risk management, which matters for NESA assessments and ISO 27001 certification processes in UAE alike.








