Table of Contents
Toggle- Why Should Indian DevOps Teams Consider Shift-Left Security?
- What Is Shift-Left Security And Why Do The Indian DevOps Teams Need It?
- How Does VAPT Enhance DevOps Security For Indian Tech Teams?
- What Are the Key Security Risks In DevOps Pipelines For Indian Businesses?
- How Can Indian DevOps Teams Implement VAPT From Day One?
- How VAPT Enhances Cloud DevOps Security For The Indian DevOps Teams?
- How VAPT Strengthens Cloud Security In DevOps For Indian businesses?
- Ensuring Security At Every Stage Through The Shift-Left VAPT Approach For Indian Business Applications
- Shift-Left Security With VAPT as a Game Changer For Indian DevOps Teams
- VAPT In DevOps FAQs
Why Should Indian DevOps Teams Consider Shift-Left Security?
Security is no longer something you patch at the end of the development cycle.
In DevOps, waiting until deployment to address vulnerabilities is a mistake that can cost you a fortune.
With Shift-Left Security, you don’t have to wait till the end to think about security. What it requires for you is to start at the first line of code. Shift-Left Security doesn’t technically convey an afterthought. It’s something you bake into your software development lifecycle, right from the beginning.
When DevOps teams use VAPT from day one, things change.
You catch bugs and weak spots early before they sneak into production and cause a mess.
You save time, money, and a lot of firefighting at the end. Not to mention how fixing issues at the end can turn out way too expensive.
You derive enhanced cloud security, even when your teams are moving fast and deploying daily.
And you keep your CI/CD pipelines flowing without surprise attacks slowing things down or breaking builds.
It’s simple Identifying threats early helps you save millions by avoiding costly breaches.
In this blog, we’re diving into a few things that matter to you, especially if you’re running DevOps at speed.
Reading this far, you must’ve realized why Shift-Left Security isn’t just a buzzword, but something that DevOps teams like you actually need, especially when you’re functioning in India.
In a 2024 report, over 65% of Indian firms got hit by ransomware attacks due to DevOps misconfigurations, cited The Economic Times. Among those getting highly included fintechs, finance, and e-commerce organizations.
The seriousness of these occurrences strategically demands implementing VAPT early on in the SDLC to achieve and maintain software compliance and resilience. This is critical as far as it concerns strongly adhering to relevant cybersecurity laws and regulations in a country like India. Also, frequent publishing of guidelines and undergoing regular VAPT audits have become mandatory.
How VAPT fits into that picture and makes cloud environments less risky, even when everything’s moving fast.
And how using VAPT from day one protects your CI/CD pipeline before anything slips through the cracks? This is what we need to find out.
What Is Shift-Left Security And Why Do The Indian DevOps Teams Need It?
Understanding Shift-Left Security
Shift-Left Security is about moving security to where it belongs right at the start of development. Instead of waiting until an app is ready to ship and then running checks.
Security becomes part of the process from the moment code is written.
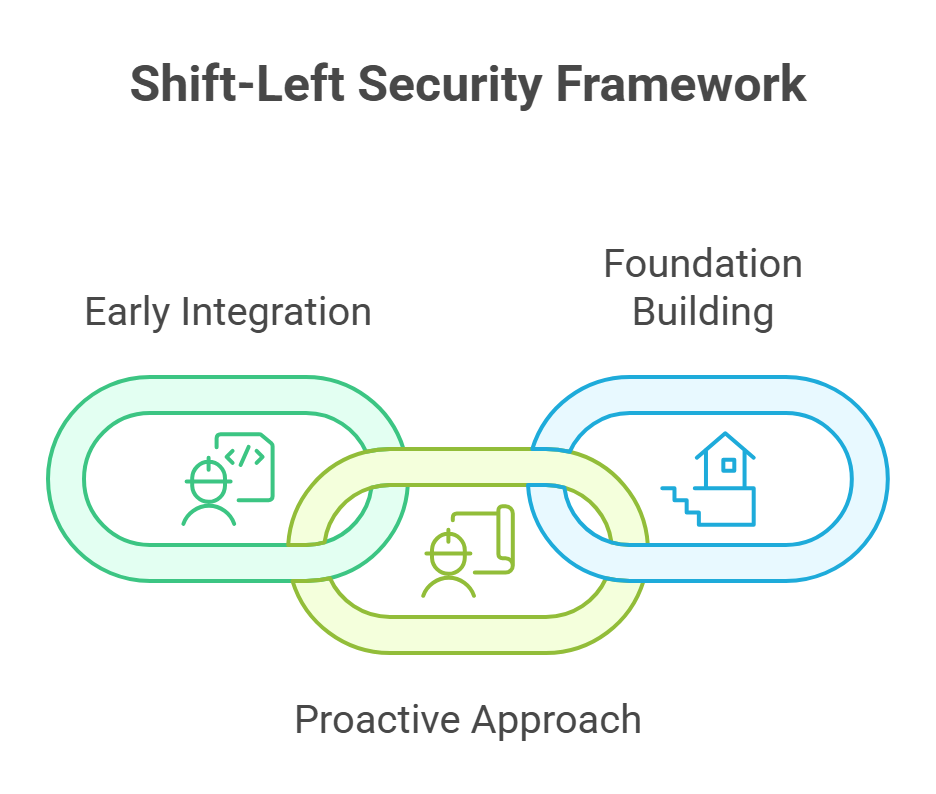
Think of it this way: you wouldn’t build a house and check for cracks after moving in. You’d lay a solid foundation first. Same idea here.
In essence, shift-left security implies moving security ‘left’-right where the software development process begins.
Why Shift-Left Security For Indian DevOps Teams?
Shift-left security can prove to be a boon for Indian DevOps teams due to:
●Improved security posture
That means less exposure. Fewer windows for attackers to sneak in. And more peace of mind knowing your team is catching things before they become problems.
● Cost-effective security measures
Fixing bugs early is easier. And cheaper. If you catch a vulnerability while you’re still writing code, it takes minutes to fix. If it slips into production, it might cost hours or worse, real money.
● Enhanced development speed
With Shift-Left, security doesn’t slow things down. It becomes part of every commit, every build, every release.
And if you care about ISO 27001, SOC 2, GDPR (and you probably do), Shift-Left makes it way easier to stay compliant without scrambling at the last minute.
How Does VAPT Enhance DevOps Security For Indian Tech Teams?
What Is VAPT In DevOps?
VAPT in DevOps is all about staying ahead. It’s not just a scan at the end. It’s a continuous loop find the risks, test them, fix them, repeat.
For DevOps teams, VAPT is crucial to scan code right from day one. You catch misconfigurations, weak spots, and logic flaws before they become live problems.
It also means your CI/CD pipeline isn’t just fast it’s safe. You’re checking the build, test, and deployment stages for anything that could go wrong from a security standpoint.
Then there’s threat simulation. Ethical hackers step in to do what real attackers might do except they’re on your side. They find the holes so you can close them.
Also Read : DevSecOps vs. DevOps: What’s the Difference and Why It Matters?
And with more teams moving to the cloud, VAPT helps you validate everything from cloud configs to API access controls—because securing cloud infrastructure isn’t optional anymore.
If you’re building fast, VAPT makes sure you’re also building smart.
Both CERT-In guidelines (as per MeitY) and the Information Technology Act, 2000 in India require regular VAPT implementations for organizations handling sensitive data. such as banking, insurance (IRDAI), and payments (RBI & NPCI).
How VAPT Helps Secure DevOps Pipelines From Day One For Indian Firms?
Security flaws don’t just show up in the final product. They creep in quietly—during development, testing, or even while pushing code live. And if you’re moving fast, it’s easy to miss them. That’s where VAPT comes in. It gives DevOps teams a way to catch threats early, not after something breaks.
What Are the Key Security Risks In DevOps Pipelines For Indian Businesses?
A CERT‑In Advisory CIAD‑2025‑0014 that was issued in April 2025 flagged high-severity vulnerabilities across Microsoft products (Windows, Azure, SQL Server, etc.). These being actively exploited in India highly demand conducting early-stage VAPT across all layers
DevOps moves fast, which means there’s a lot of room for missteps if you’re not careful. CI/CD tools like Jenkins or GitHub Actions? If misconfigured, they can leak secrets in plain sight.

Access controls? Too often, they’re either too loose or not enforced at all giving attackers a chance to escalate and move deeper into your systems.
APIs? They’re powerful, but also risky. If you do not validate them the way they should be, there’s a possibility for attackers to directly step in and steal vital and sensitive data.
Then there’s third-party code. You trust it, but do you verify it? If someone slips in something malicious, your entire app is at risk.
How Can Indian DevOps Teams Implement VAPT From Day One?
The best way to implement VAPT early on in the software development process is by running Static Application Security Testing (SAST) to scan source code as soon as it’s written.
Use Dynamic Application Security Testing (DAST) to simulate attacks on your running app and catch what SAST misses.
If you’re using Infrastructure as Code Terraform, Kubernetes, CloudFormation scan it too. Misconfigurations there can break everything.
And don’t skip full-blown penetration testing of your CI/CD pipelines. You need to know exactly where the cracks are before someone else finds them.
In order to meet official standards, many Indian organizations have chosen CERT‑In–empaneled VAPT vendors, who follow a defined methodology that involves both automated scanning (SAST/DAST) and manual pen testing. These also include internal/external scope, configuration reviews, and compliance reporting.
How VAPT Enhances Cloud DevOps Security For The Indian DevOps Teams?
With cloud-native DevOps, you’re not just securing code—you’re securing the entire environment. That means cloud infrastructure, APIs, containers, all of it.
Unsecured S3 buckets? They’re still a thing. Public blobs leaking data? Happens more than you’d think.
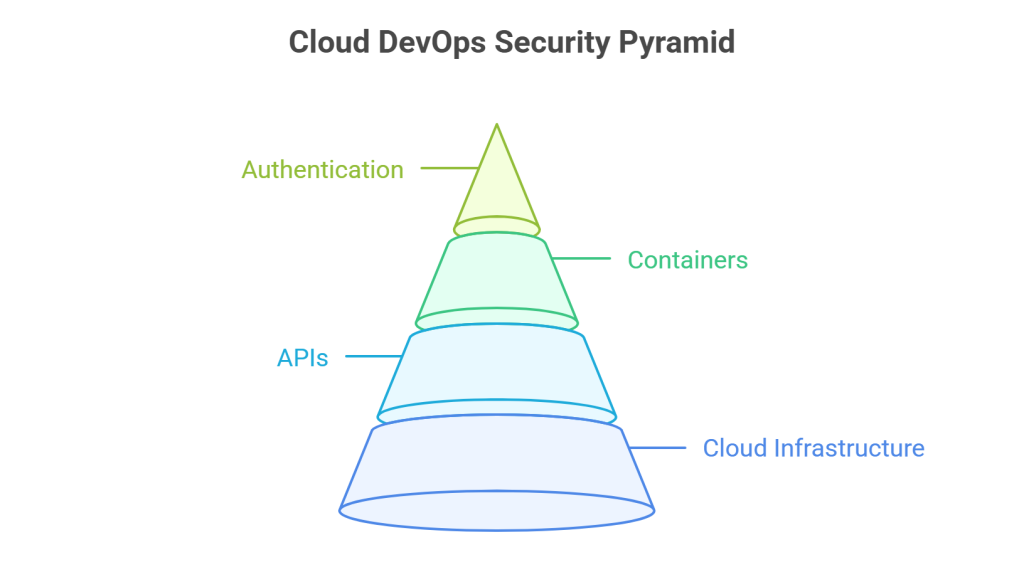
Outdated Docker images or misconfigured Kubernetes clusters? Easy for attackers to exploit.
Weak API authentication? One bad call, and someone’s inside your system.
How VAPT Strengthens Cloud Security In DevOps For Indian businesses?
VAPT checks every moving part of your system to identify and fix security gaps.
Through cloud penetration testing, you simulate real-world attacks—on your actual cloud setup—to see what could go wrong.
API penetration testing makes sure endpoints are locked down and do not expose sensitive operations.
Container security assessments go deep into Docker, Kubernetes, and microservices to look for flaws you can’t afford to ignore.
Ensuring Security At Every Stage Through The Shift-Left VAPT Approach For Indian Business Applications
When you embed VAPT into your pipeline from day one, you stop treating security like a final checkpoint. You actually bake it into the process.
The earlier you catch a flaw, the faster and cheaper you fix them. No wonder for things to slow down entirely when fixing errors in the later stages, with panic and troubles easily flowing in.
Let’s look at how VAPT plugs in across the DevOps lifecycle.
●Code Review & Static Application Security Testing in the Development Phase
When you push code to GitHub or GitLab, merge branches, and move fast, this inadvertently increases the risk of exposing hardcoded secrets. As a developer, this is the first mistake that you typically commit and happens right when you input the source code.
When applying Static Application Security Testing (SAST) into your DevOps process, it proactively helps you detect vulnerabilities, such as hardcoded credentials, API keys, and full-access tokens insertion earlier into your SDLC.
Not only these, for SAST also catches common security flaws like SQL injection and cross-site scripting (XSS) early on way before attackers can use them.
VAPT helps reduce long-term security debts by enforcing secure coding practices right from the early stage of development. This suggests fewer headaches later on.

Real-world incidents like the Elektra Leak campaign in 2023 well exemplify how attackers can exploit leaked AWS credentials on GitHub in no time. These are enough to trigger innumerable EC2 instances for malicious intents like cryptojacking. Incidents like these can potentially invoke costly penalties for organizations, up to thousands of dollars on a weekly basis. Clearly emphasizes the role of integrating VAPT for ensuring security and compliance.
● Build & Integration (CI/CD Security Assessment)
The CI/CD pipeline gets triggered at the point where a code is pushed. Once there, building, testing, and deployment to staging happen automatically.
You should note however that CI/CD pipelines require access permission to sensitive data like API keys authentication tokens, database credentials, etc. This is critical to perform tasks like deploying applications or communicating with cloud providers.
When Jenkins, GitLab CI/CD, GitHub Actions, etc., aren’t secure enough to handle these so-called secrets, they are sure to leak these sensitive pieces of information.
VAPT checks these pipelines end-to-end. It audits configs, permissions, and checks how secrets are handled.
It also inspects third-party libraries because if one of them has a known vulnerability, your app inherits it.
Supply chain attacks are real. Remember SolarWinds? Attackers injected a backdoor into their update process and reached 18,000 companies. That started in the build pipeline.
● Deployment & Production (Cloud & API Security Testing)
At this stage, the app’s live. Cloud infrastructure is up. APIs are exposed. Things are real.
This is where attackers try to exploit whatever they can find weak access controls, open APIs, misconfigured permissions.
VAPT simulates real-world attack scenarios. It looks at how your APIs handle authentication, how your cloud setup handles access, and whether your containers are secure.
Also Read : What is DevSecOps and Why is It Most Needed in 2025?
In 2021, Tesla left their Kubernetes dashboard exposed. Attackers used it to run crypto-miners on their cloud. A misconfiguration. A costly one.
VAPT would’ve caught that during a routine cloud config review.
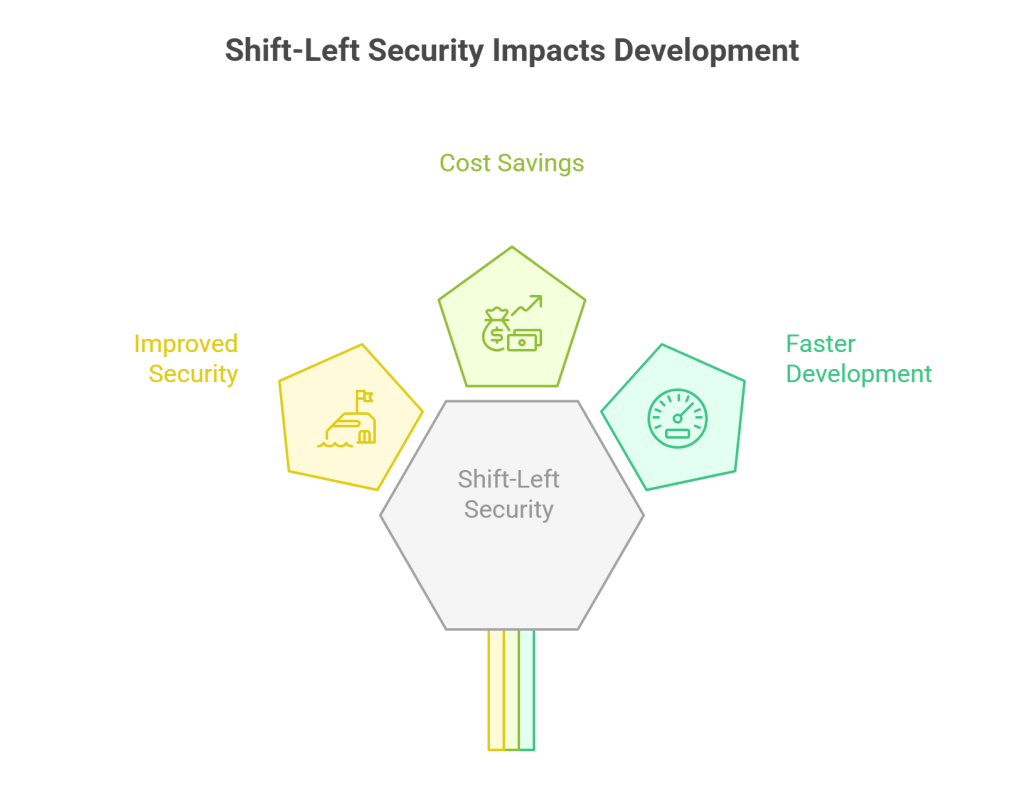
Shift-Left Security With VAPT as a Game Changer For Indian DevOps Teams
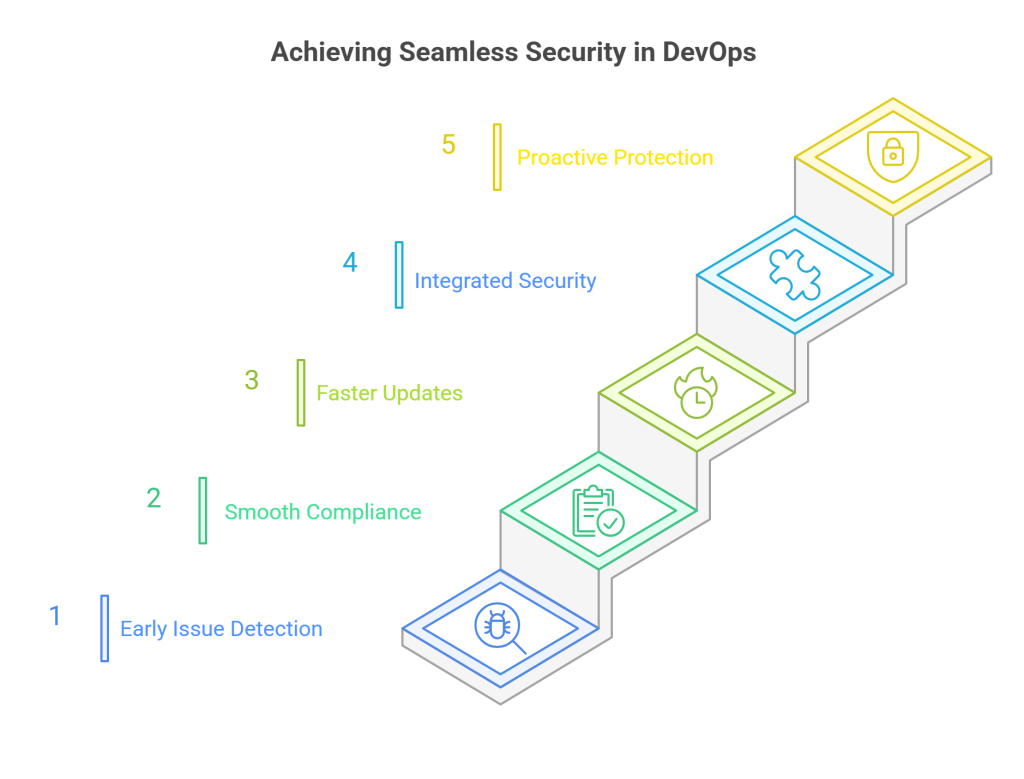
Spotting issues early doesn’t just reduce risk it changes how teams work. It makes compliance smoother, updates faster, and security feel like part of the build not a blocker.
According to NIST research, security defects can cost 30-60 times more to fix in production than during the development phase, with the multiplier increasing exponentially through each stage of the SDLC.
It helps you meet standards like ISO 27001, SOC 2, GDPR, PCI-DSS without scrambling before audits.
And it means your cloud, your APIs, your containers all of it is protected before release, not after an incident.
Through DPDP Act 2023 and DPDP Rules 2025, India further reinforces the need to input proactive security controls like VAPT as part of its mandatory Data Protection Impact Assessments (DPIAs), breach notification timelines, and data security accountability for fiduciaries and significant data processors.
Securing Your DevOps Using Shift-Left Security with VAPT
DevOps is fast. But attackers move faster.
The only way to stay ahead? Make security part of the process not a patch you apply later.
Shift-Left Security backed by proactive VAPT is how you keep your team building at speed without leaving doors open.
Are your codes, systems, and applications secure and resilient enough to keep up with upcoming threats? Connect with Wattlecorp to know where you stand in terms of your security posture. As a cybersecurity service provider offering vulnerability assessment and penetration testing services in India, we suggest you to integrate VAPT to secure your SDLC.
From cloud pen testing to API validation to CI/CD pipeline reviews it’s all part of the system.
Shield while you build to steer clear of vulnerabilities and subsequent attacks.
VAPT In DevOps FAQs
1.Why Does DevOps Recommend Shift-Left Security For Indian Tech Teams?
Indian tech teams should consider Shift-Left security because it will allow them to develop software securely from the start without affecting the speed of the process. It will also enable them to effectively lower the cost associated with threat detection and mitigation that emerge later on in the Software Development Lifecycle (SDLC).
In addition to these, Shift-Left security implementation can also help the Indian tech team efficiently manage the increased velocity associated with the modern DevOps environment This is all due to the cheap, smart, and fastness that comes with the same.
Not only these, Shift-Left Security brings with it better communication and collaboration that lead to developing high-quality and secure software as per client and market demands.
2.How Does VAPT Help Indian DevOps Teams in Shift-Left Security?
With VAPT integration, the Indian DevOps teams can effectively automate early and continuous detection of security vulnerabilities. These simultaneously lead to appropriate mitigation and remediation of those flaws and associated risks within the SDLC.
3.How Does VAPT Enhance Cloud DevOps Security For Indian Business Applications?
For Indian business applications to derive enhanced Cloud DevOps Security, this should include:
● Adopting Cloud-specific security testing approaches.
● Look for best possible ways to expertly handle misconfigured cloud services.
● Start integrating VAPT into CI/CD pipelines to ensure secured and faster release of software on a continuous basis.