One of the two major mobile operating systems in terms of users and popularity, Android has a lot of perks. The open-source nature of Android makes it a wonderful playground for all kinds of mobile applications. While the number of malicious applications on Android outweighs the ones that can be used for security, there is a good number of hacking applications found on Android. Not all of them are noteworthy, but some of them are impressive enough to leave a mark. Here are the top 10 hacking applications on Android.
1. AndroRAT
Just like any RAT (Remote Access Tool), this one also comes with the same features but is focused on Android devices. The name is made by combining Android and RAT. This client/server application allows you to gain remote control of any Android device and fetch information from it. The application needs to be generated and configured using a computer.

The application needs to be installed on the victim’s computer and once the device is connected to the Internet, you will obtain remote control of the device. The app runs in the background after boot, once installed. The server connection is triggered by a call or an SMS. Once the device is connected, you can obtain access to the following information:
- Capture pictures using the rear/front camera
- Stream video
- Dump SMS
- Dump the Call log
- Dump contacts
- Stream live audio via the microphone
- Generate vibrations on the phone
- GPS location
2. WiFiKiLL Pro
As the name suggests this application is used to revoke WiFi access to devices connected to the same network. It blocks access by stopping the internet packets directed to the device over the network.

The app displays all the devices connected to the network including the MAC addresses, data transfer rates, and the device names for each of them.
3. zANTI
One of the most popular penetration testing tools on Android, zANTI is used for simulating and executing attacks on a network. It is used for MAC address spoofing,

MITM attacks, password auditing, vulnerability testing, and much more. zANTI brings the power of Backtrack on your Android device, as it maps the entire network and sniffs the websites being visited along with their cookies.
Features provided by zANTI
- Creating a malicious WiFi hotspot.
- Checking a device for shellshock and SSL vulnerabilities.
- Changing the MAC address of a device.
- Modifying HTTP requests and responses.
- Exploiting routers.
- Auditing passwords.
Read More: How To Create Strong Passwords
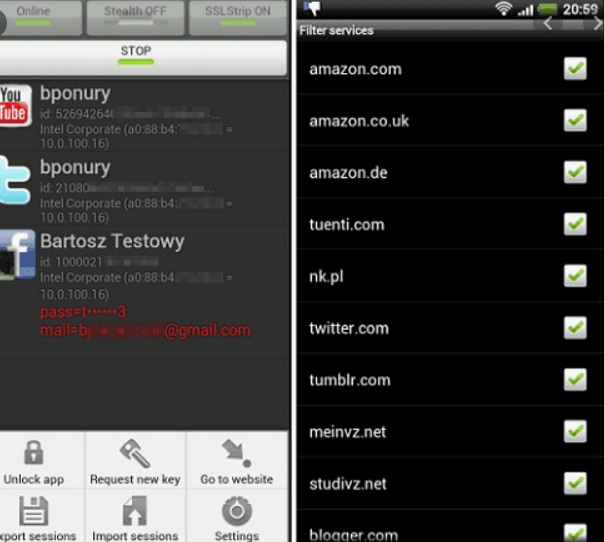
4. DroidSheep
An efficient tool for web session hijacking, DroidSheep acts analogously to a router that monitors and intercepts all WiFi data transmitted between devices inside a network. It listens to the HTTPS packets sent via the WiFi network and extracts the session id, making it reusable.

While intercepting WiFi network traffic, it fetches the profiles of active sessions. DroidSheep makes interception of all kinds of Internet activity, including social media usage, and web browsing among other kinds of Internet surfing.
Also Read: Android Penetration Testing Guide 2024
5. SSHDroid
SSHDroid is an Android application that converts your Android device into an SSH server. It allows you to securely connect to your device from a computer and execute terminal commands or edit files.

This app provides features like shared-key authentication, WiFi autostarts whitelist, and extended notification control.
6. Hackode
Nicknamed the Hacker’s Toolbox, Hackode earned the name by proving to be a common tool in various different hacking processes. This application is used by penetration testers, ethical hackers, IT administrators, and cybersecurity professionals.

The versatile nature of Hackode allows it to be used for scanning, reconnaissance, performing exploits, and many other tasks.
The various tools in Hackode allow the following activities:
- Port scanning
- Reconnaissance actions
- Whois
- Traceroute
- DNS and IP searches
7. Kali NetHunter
Kali NetHunter’s compatibility with Android devices running earlier software versions has allowed it to become a popular open-source Android penetration testing software.

The app comes with a few functions including wireless injection, an AP mode, MITM attacks, and the functionality to execute HID keyboard attacks. Kali NetHunter basically runs as an overlay on your device and picks up Internet traffic.
Read More: Top Kali Linux Steganography Tools
8. cSploit
With a built-in Metasploit framework, cSploit is a powerful Android application used for hacking. Apart from the built-in framework, the friendly user interface also gives it bonus points in the hacker’s toolbox.

It can map the local network, forge TCP or UDP packets, detect open ports, fingerprints of the host’s operating system and perform MITM attacks. The Metasploit framework helps in finding vulnerabilities present in the network and devices connected to it.
9. Network Mapper
A frontend for the Nmap scanner, Network Mapper brings the interface to an Android platform.
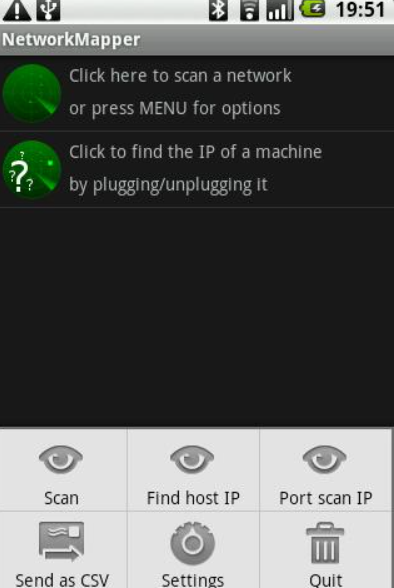
Once the app is installed, it lets you check out open ports, protocols, hosts, services, and other sensitive information about any network you’re connected to.
10. FaceNiff
FaceNiff is an Android application that lets you monitor and intercept the profiles on a live web session on the same WiFi network that you are connected to. It works exclusively on the native Android browser and when somebody logs into Facebook, Youtube or Twitter, FaceNiff hijacks the session and you can steal their credentials.
Interested to learn more about other good hacking apps on Android and master their usage? Follow our cybersecurity blog to keep yourself updated with the latest trends in cybersecurity. We also provide training programs for those interested in starting a career in this field.







1 thought on “Top 10 Hacking Apps & Tools On Android 2024”
hi…..
I got such a good information on this topic its very interesting one.