Mitigation of security threats can be made much simpler with a guide. Mobile devices and applications have already taken vital roles in our daily lives. Office jobs, entertainment, personal communications, or financial transactions the applicability grows day by day.
Gaining visibility into mobile risk may be a challenging but achievable task, particularly if, like most businesses, your workforce uses a combination of supervised and unsupervised iOS and Android devices.
Mobile app security is essential to your overall security posture, whether it is dealing with vulnerabilities at the level of the mobile operating system, app dangers, or phishing and network threats.
Table of Contents
Toggle- Top 10 mobile app security Best Practices
- 1.Strong cryptography
- 2.Consistent security policy enforcement
- 3.Tamper detection
- 4.Continuous risk assessment
- 5.Strict authentication and authorization
- 6.Implement binary protection
- 7.Use Google Cloud Messaging instead of SMS
- 8.Identify common data leakage points
- 9.Ensure up-to-date security patches are installed
- 10.Use secure APIs
- Importance of regular security testing and updates for mobile app security
- Role of mobile app penetration testing towards security
Top 10 mobile app security Best Practices
We have listed some mobile app security best practices in 2024, they are
- Strong cryptography
- Strict authentication and authorization
- Tamper detection
- Continuous risk assessment
- Consistent security policy enforcement
- Implement binary protection
- Identify common data leakage points
- Use Google Cloud Messaging instead of SMS
- Ensure up-to-date security patches are installed
- Use secure APIs
1.Strong cryptography
Cryptography acts as a trusted guardian, ensuring data integrity and secrecy. By incorporating SHA into your mobile app, you are taking a significant step toward improving the security of your app. After all, encryption in mobile app security is about more than simply keeping data safe—it’s also about making it real and trustworthy.

The National Security Agency (NSA) created the SHA family of cryptographic hash algorithms. These routines accept an input (or ‘ message ‘) and return a string of bytes of a defined length. The output is a ‘digest’ that is unique to each unique input and is commonly presented as a text string. Even little changes in the input will result in such a large change in the output that the new digest will look uncorrelated.
However, incorrect cryptographic implementation disrupts overall mobile security too.
Many prominent cryptographies, such as MD5, MD4, and SHA1, have been discovered to be vulnerable in the face of increased cybercrime. Using the most recent APIs helps to ensure the highest cryptographic security.
2.Consistent security policy enforcement
Securing mobile apps helps to prevent various threats that commonly affect mobile applications. Mobile application management policy enforcers ensure policies such as authentication, encryption, data loss prevention, and access controls are in place.
This helps to keep the mobile application and devices secure from various security threats such as malware attacks, data leakage, insecure authentication, rooting or jailbreaking, and insecure APIs and third-party components.
3.Tamper detection
It is the feature that helps the developers or the application owners to be informed when there is an unauthorized attempt to compromise or modify the data within a device or the device itself. It comes in handy in taking necessary preventive measures to fix the threat at the right time eliminating or reducing its impact.
In mobile app security, tampering can be modifying either the app environment, running process, or the compiled app. Detecting a tampering attempt helps to ensure that no recompilation has been done by unauthorized personnel without the knowledge of the owner prior to app release.
Code obfuscation, check-summing, and digital signatures are some of the common anti-tampering features in mobile applications. Taking such necessary security measures makes it difficult for bad actors to alter your code and alerts you of any potential tampering efforts.
4.Continuous risk assessment
It helps to understand the data stored by your business, where it is stored, and who has access to it. This helps take necessary actions to reduce the data-related threats and to minimize its access only to the necessary ones by the mobile application owners. Also, this approach monitors the information security controls and vulnerabilities for the business to make risk management decisions.
5.Strict authentication and authorization
Authentication and authorization are processes for verifying that a legitimate user is accessing the mobile application.
Simply authentication verifies the user’s identity, which is usually done using unique login credentials or biometrics or tokens. This helps to confirm that a person is who they are claiming to be.
On the other hand, authorization is about setting restrictions to levels of operation in the mobile application. This allows or denies access to specific data or functions based on the role of the user.
Once implemented properly, authentication and authorization help to improve the information sharing and security of the application. Also, they help in fraud prevention, customer data protection, and in enforcing strict access control measures in the mobile application.
6.Implement binary protection
They are a set of actions that prevent the tampering of applications and make it much more complex for bad actors to alter the application code or its functioning. Suitable tools and methodologies are implemented as an extra layer to protect binary files from exploitation with reverse engineering.
7.Use Google Cloud Messaging instead of SMS
SMS protocol is neither secure nor encrypted. SMS may also be viewed and read by any other app on the user’s smartphone. GCM aka Google Cloud Messaging is a feature by Google in which the communications are authenticated on the client side by registration tokens that are reset regularly, and on the server side by a unique API key.
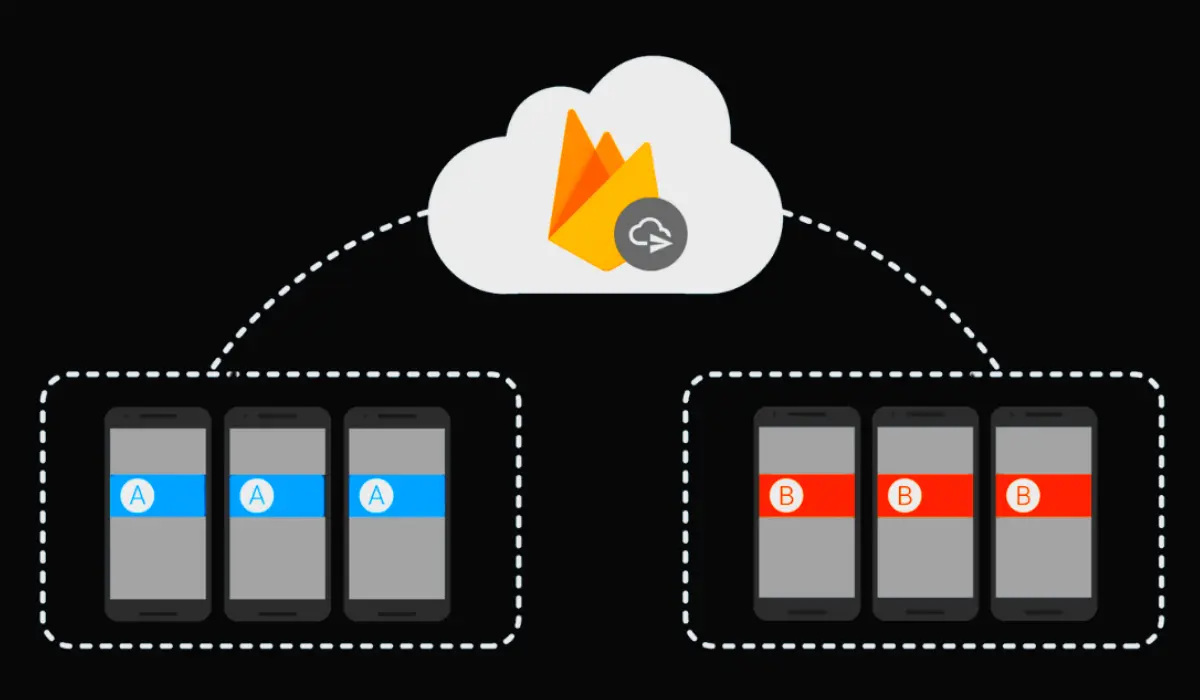
Switching from SMS to GCM improves the security of the message communications being received and sent. This includes financial details, passwords, OTPs, and even personal details.
8.Identify common data leakage points
Storing sensitive mobile app data in insecure file locations on the mobile device is one of the major reasons for data breaches. Monitoring typical data leakage areas including logging, app background, caching, browser cookie objects, and HTML5 data storage helps to secure the data from threats.
9.Ensure up-to-date security patches are installed
More than the addition of new features, mobile app upgrades also aim to improve its security. An obsolete application is perhaps more susceptible. The majority of developers maintain the security of their software with patches and deliver them to user devices via secure installation channels such as the Play Store on Android and the App Store on iOS platforms.
10.Use secure APIs
While APIs are incredibly helpful, they also come with a significant security risk. APIs often employ an API key to ensure that the call to the API server comes from an actual instance of your mobile app.

But what happens if an attacker obtains the API key? Also, keeping API keys in a mobile application makes it easier for threat actors to use reverse engineering tools to find and exploit them.
Also Read: Top 10 Mobile App Security Threats in 2024
Importance of regular security testing and updates for mobile app security
Since we already discussed about some of the best mobile app security best practices, we know that mobile application security testing is essential for preventing security breaches, data theft, and other vulnerabilities that could harm users. Personal information, financial information, and login credentials are all stored in mobile applications. Mobile application security testing ensures that the data is secure and not at risk of data theft.
Cyber attacks from malware can also cause serious harm to mobile devices. Mobile application security testing can aid in the identification of possible malware attacks offering solutions to avoid them. Mobile application security testing helps prevent data breaches protecting user data, and preserving the company’s reputation.
This is largely because a lot of personal applications have dangerous permissions. From an individual perspective, permissions like location, local files, and address book access may appear harmless, but they could compromise the security of business data accessed from that device.
Role of mobile app penetration testing towards security
Since mobile applications are becoming more prevalent, cyber attackers have more opportunities, which is why many are actively installing app-specific malware and why smishing, MITM attacks, and firmware assaults are on the rise. Organizations must eliminate as many of these routes as feasible. The easiest way to accomplish this is to identify vulnerabilities before the bad guys exploit them. This is when penetration testing comes into play.

The key advantage of pen testing is the detection of vulnerabilities in your mobile application. This includes defects in coding, design problems, and configuration oversights. Identifying these vulnerabilities is the first step toward resolving them and improving your app’s security. It can help you understand the possible effects of certain vulnerabilities. Some vulnerabilities are more dangerous than others. Understanding this allows you to prioritize which issues to solve first based on their risk level.
The findings allow firms to address identified risks early in the development lifecycle. Pen testing may also reveal flaws in security ecosystems, therefore businesses should surely use this potent weapon in the fight against the bad guys and you can follow above mobile app security best practices for preventing your app from breaches.
Regular mobile app penetration testing and continuous security hardening may boost user trust in your software. They are more likely to continue using your app and suggest it to others if they feel you take their security seriously.