IoT, or the Internet of Things, has made tasks interconnected and innovative,e with measures to improve communication of potential objects using the power of the Internet. IoT plays a significant role in our daily lives, from smart homes and domestic systems to industrial intelligence. However, the increased usage of IoT devices has also given birth to serious security challenges that need attention.
For an effective solution that addresses these challenges, the Open Web Application Security Project (OWASP) has identified the top 10 vulnerabilities that can compromise the security of IoT devices and ecosystems. These vulnerabilities are based on real-world incidents that demand the best methods to detect flaws and adopt suitable mitigation approaches.
OWASP IoT Top 10 vulnerabilities list was developed with a detailed methodology after an in-depth study of real-world IoT security challenges. In this blog, let’s understand every vulnerability and the ideal strategies you can adopt to mitigate them.
Table of Contents
Toggle- What is the OWASP Top 10 IoT ?
- OWASP IoT Top 10 Vulnerabilities
- 1. Weak, Guessable, or Hardcoded Passwords
- 2. Insecure Network Services
- 3. Insecure Ecosystem Interfaces
- 4. Lack of Secure Update Mechanism
- 5. Using Insecure or Outdated Components
- 7. Insecure Data Transfer and Storage
- 8. Absence of Device Management
- 9. Insecure Default Settings
- 10. Lack of Physical Hardening
- Practical Steps to Overcome The Common Challenges
- Frequently Asked Questions
What is the OWASP Top 10 IoT ?
The OWASP Internet of Things (IoT) Top 10 is one of OWASP’s Top Ten Projects. It is a security risk that can make IoT devices vulnerable. These challenges could be a lack of security in web interfaces, lost authentication, and authorization risks.
OWASP IoT project is focused on helping manufacturers, developers, and users understand the security risks of IoT devices and provide guidance on how to get rid of these risks.
OWASP IoT Top 10 Vulnerabilities
Here are the security risks reported in the OWASP IoT Top 10,
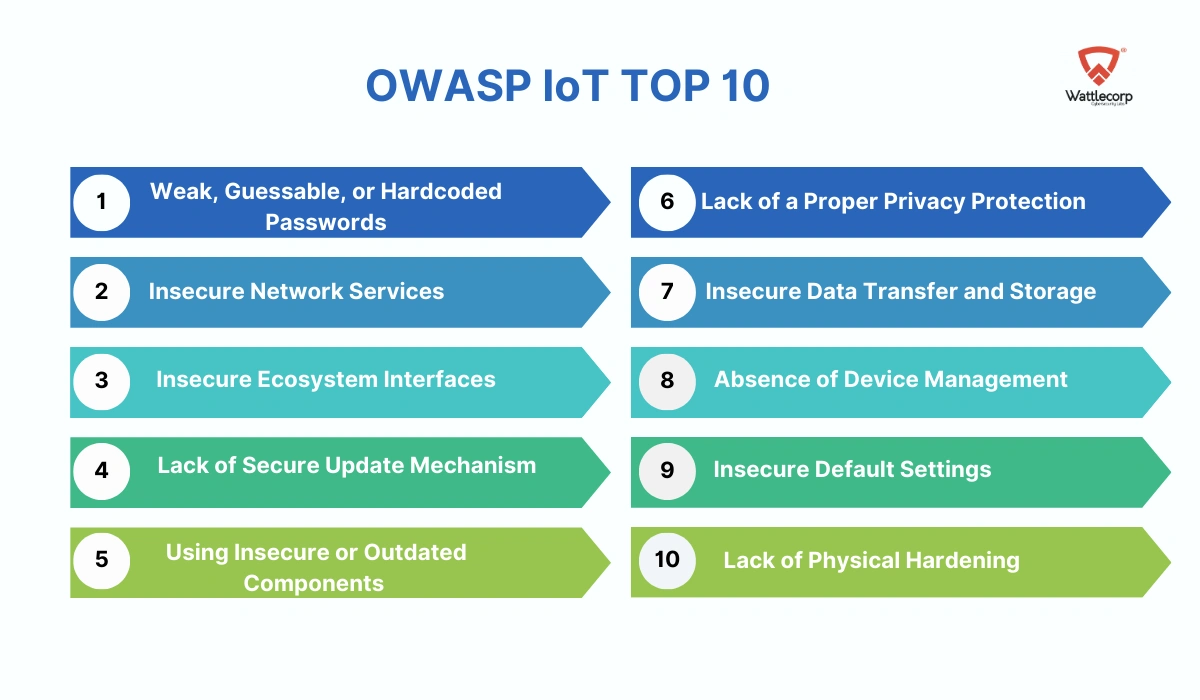
- Weak, Guessable, or Hardcoded Passwords
- Insecure Network Services
- Insecure Ecosystem Interfaces
- Lack of Secure Update Mechanism
- Using Insecure or Outdated Components
- Insecure Data Transfer and Storage
- Absence of Device Management
- Insecure Default Settings
- Lack of Physical Hardening
1. Weak, Guessable, or Hardcoded Passwords
IoT devices usually have web-based interfaces used to perform configuration and management accompaniment,e authentic tasks in the device like network services, serial console, etc. When these interfaces are not configured appropriately, attackers could access the sensitive information and cause unauthorized changes to the device’s configuration.
IoT security testing assessments have proven that a majority of IoT devices tested include guessable passwords and username lists. Embedding fixed passwords acts as another major concern, where the developers accommodate hardcoded credentials in IoT device components, say, for example, firmware.
Solution:
- Manufacturers should adopt appropriate authentication and password management mechanisms to make sure that the passwords are secure and not easy to guess.
- Also, users must be encouraged to change the default passwords on devices and use unique, strong, and difficult-to-guess passwords while performing device setups.
2. Insecure Network Services
The vulnerabilities in security protocols or configurations, such as unencrypted communication protocols, lack of proper network security configurations, and using outdated or vulnerable software, refer to insecure network services.
Attackers could exploit these vulnerabilities to access sensitive data, release attacks against other systems, or earn unauthorized permissions to the device. It was also found that an insecure File Transfer Protocol (FTP) service in IoT devices used hardcoded credentials, which helped users read/write arbitrary areas and the device.
Solution:
- Secure network protocols like Transport Layer Security (TLS) and regularly updating the network services can mitigate this concern.
- Implementing periodic network vulnerability assessments helps to detect crucial security flaws in IoT networks.
3. Insecure Ecosystem Interfaces
The vulnerability arises from insecure interfaces between various components existing within an IoT ecosystem. Different IoT devices have badly secured web, API, or mobile interfaces with external systems like traditional IT systems, cloud services, and other IoT devices. Intruders can use these interfaces to gain access to sensitive data, cause attacks against other systems, or manage the device and its functions.
The API that has no authorization can lead to the generation of a user’s UUID (Universally Unique Identifier) and could be utilized to fetch the user’s location, password, the devices connected to the application, email address, and more. The vulnerability points in terms of security of the IoT devices point to the lack of ideal authorization measures.
Solution:
Consistent patching of APIs, implementing stringent access controls to limit access to sensitive interfaces and APIs, deploying secure communication channels between various components of the IoT ecosystem, and adopting encryption are the best strategies you can use to avoid the aforementioned threats.
4. Lack of Secure Update Mechanism
IoT devices are secure cost-effective, low-power, and easy to use, which causes security to be overlooked in many situations. The lack of a particular update mechanism could make IoT devices prone to specific exploits or vulnerabilities.
The intruders can benefit from the outdated software or firmware to compromise the overall device’s security. The vulnerability in IoT payment systems can lead to major consequences, which include financial loss, unauthorized access to sensitive data, and disruption of critical systems.
Solution:
Implementing features like digital signatures, secure delivery, anti-rollback mechanisms, and firmware validation on devices helps manufacturers effectively address the vulnerabilities.
5. Using Insecure or Outdated Components
A major issue that arises in IoT devices is the use of outdated or insecure parts in the device. Many IoT devices are built with the help of third-party components which can result in vulnerabilities. These components can be exploited by attackers, thereby degrading the device’s security.
Manufacturers using open-source components to build IoT devices develop a complex supply chain that is difficult to track. These components could inherit vulnerabilities known to the intruders, and create a threat landscape that might lead the device to be compromised.
Solution:
- Regularly update and patch each component and software in IoT devices (for instance, the piece ovaries, firmware, and frameworks)
- Track and get notifications about the security vulnerabilities in the components you use in the IoT system.
Also Read: OWASP Top 10 Vulnerabilities
6. Lack of Proper Privacy Protection
Different IoT devices receive and store sensitive personal information, but, these stand behind without appropriate privacy or data protection. This can be data collection without the user’s consent, data storage without adequate security controls, and data sharing with third parties without appropriate permissions.
Consider a home automation device that collects information such as payment data and live location. While the device permits all operations concerning payment, every data could be sent over the post to every piece of encrypted channels.
Solution:
Adopting privacy-by-design principles, utilizing encryption to protect sensitive data in storage and transmission, and gaining user consent for data collection or usage are certain effective solutions.
7. Insecure Data Transfer and Storage
Data transfer or date storage in plain text with no encryption is a serious concern of IoT devices. The devices collect both sensitive data and user information. The intruders can manipulate the data while under transit or exploit weak it is inge spaces.
For instance, in some cases, where the device uses File Transfer Protocol (FTP) for file transfer, the attacker can access the traffic and modify it. An insecure HTTP protocol that routes every communication with the web could lead to this vulnerability.
Solution:
Secure protocols like HTTPS for file transfer, encryption of sensitive data, deploying robust data access controls, and auditing data storage practices regularly help secure data transfer and data storage in IoT devices.
8. Absence of Device Management
Failure to manage IoT devices effectively can compromise the whole network. Lack of effective device management causes attackers to manipulate or control IoT devices virtually. Lack of management can lead to unauthorized access, device manipulation, or firmware tampering.
For example, the expired SSL certificates in the devices can cause communication to the web to move along HTTP. The SSL certificates are not updated as the device fails to give updates, making the device vulnerable.
Solution:
Adopting strong authentication mechanisms like unique device credentials and implementing access controls to limit the device management functionalities to the concerned experts can resolve this risk.
Also Read: OWASP Mobile Top 10 Vulnerabilities
9. Insecure Default Settings
Default settings are usually insecure settings, which make the IoT devices vulnerable to high-security risks. They include the default configurations used initially but left unchanged. These settings could be default usernames, passwords, open ports, unencrypted communications, etc. Often, default settings adopt a “bare-minimum” approach or can also introduce security vulnerabilities, like say, hardcoded passwords, exposed services that operate through root permissions, etc.
Solution
The changes in default usernames, configurations, and passwords during initial device setup, and disabling unwanted services and ports to minimize the attack surface can help mitigate the vulnerability.
10. Lack of Physical Hardening
The absence of physical hardening could be a barrier to ensuring physical security. This makes embedded devices vulnerable to different hardware attacks or firmware tampering, which gives unauthorized access to hackers such as root login, extraction of sensitive information, etc; which could be helpful for remote—attacks or control of the IoT device.
Solution
Certain measures that can be adopted to harden devices such as disabling or isolating devices, debugging ports, utilizing them for firmware validation, adopting tamper detection mechanisms, and not storing sensitive data on removable memory cards, are examples.
Practical Steps to Overcome The Common Challenges
As IoT devices begin proliferation, protecting against proliferating vulnerabilities and risk mitigation play a crucial role. OWASP IoT’s Top 10 vulnerabilities offer the best insights into the possible security errors that need to be well addressed.
By identifying these vulnerabilities and executing effective mitigation strategies, both individuals and organizations can build an excellent security posture that secures their IoT ecosystems, privacy, and data.
Here are the steps to follow to help you mitigate those biosecurity concerns:
- Educating the workforce about IoT security and developing a culture of cybersecurity awareness.
- Frequently update and patch every IoT device and related components.
- Deploy reliable authorization and authentication mechanisms.
- Track network traffic and device interactions against suspicious activities.
- Limit access to necessary services and trusted entities.
Mitigating IoT device security vulnerabilities is a significant task that demands a multi-faceted approach. Manufacturers and security experts should consider OWASP IoT’s Top 10 risks while designing and developing the products or executing security controls to prevent these risks in the early phase. Implementing timely IoT penetration tests in different contexts ranging from mobile application security to cloud-hosted APIs can let you ensure your IoT network security. If you need any assistance in improving your IoT device security, let us know.
Frequently Asked Questions
OWASP IoT Top 10 is an online publication that offers manufacturers, companies, security experts, and developers insights into the loopholes in the system based on the collective identification of threats and a holistic review of the current state of affairs. This enables them to focus on taking corrective action to enhance security before the exact product launch.
Insecure IoT devices can make it easier for unauthorized users to access IoT devices. It leads to data breaches, network intrusions, unauthorized device controls, etc. Data breaches can also expose personal information such as names, addresses, SSNs (Social Security Numbers), and medical records.
You can secure your IoT devices and applications using strong passwords, encryption, and multi-factor authentication. Also, manage both active and inactive IoT devices, make sure to patch up the ones you use and disconnect the ones you don’t.