Cybersecurity is a need in today’s linked world, safeguarding the crucial digital assets of all sizes of enterprises. It is not an extravagance. Businesses need to constantly strengthen their security since cyberattacks are becoming more sophisticated and common. Not all organizations, though, have the means or know-how to do this internally. This is the point where outsourcing cybersecurity becomes a critical business decision, particularly for startups and small enterprises with constrained IT staff.
Cybersecurity Ventures estimates that by 2025, the global cost of cybercrime damages will have increased from $3 trillion in 2015. This sharp rise highlights the necessity for strong cybersecurity measures and the expanding threat landscape.
As a result, you must outsource cybersecurity to a trustworthy cybersecurity partner. If you do this and correspond with financial responsibility, your security posture will improve, allowing you to concentrate more on your core business operations while we handle the intricacies of cyber threats.
We explore the advantages of outsourcing cybersecurity for your company and also discuss how to choose the right cybersecurity partner and the importance of service-level agreements to the success of these alliances.
Table of Contents
Toggle- What is Cybersecurity Outsourcing?
- Top Benefits of Outsourcing Cybersecurity
- When to Consider Outsourcing Your Cybersecurity Needs?
- How to Choose the Right Cybersecurity Outsourcing Partner?
- Ensuring Service Level Agreement (SLA) Compliance and Trust
- Best Practices for Outsourcing Cybersecurity
- Frequently Asked Questions
What is Cybersecurity Outsourcing?
The process of managing and improving an organization’s security measures through the use of outside expertise is known as cybersecurity outsourcing. It’s a calculated move where companies assign their cybersecurity responsibilities to specialized service providers rather than managing these activities themselves. Small and medium-sized businesses are more likely to engage in this activity because they lack the means or know-how to handle complicated cybersecurity operations properly.

Cybersecurity outsourcing can include a wide range of services, including managing compliance with different security standards, responding to security incidents, and continuous network monitoring and threat detection. With this strategy, businesses may have access to cutting-edge security technologies and seasoned knowledge without having to pay the high overhead of creating and managing a sizable internal cybersecurity team.
Top Benefits of Outsourcing Cybersecurity
We have listed some of the top benefits of outsourcing cybersecurity services and they are
- Access to Specialized Expertise
- Cost-Benefit Analysis
- Scalability and Flexibility
- Enhanced Focus on Core Business Functions
- Strategic Cybersecurity Partnerships
1. Access to Specialized Expertise
It is more crucial than ever to have specialist knowledge to navigate these problems as cyber threats continue to change and become more complex and diverse. Managed Security Service Providers (MSSPs) work with experts who are often involved in cybersecurity. So, they are not only up to date on the newest threats but also know the best ways to defend against them.

Because of their extensive industry experience, these professionals employ best practices and creative solutions customized to certain risks or legal obligations. Your company doesn’t need to organically develop this high degree of competence to improve its security posture by utilizing the specific capabilities of these individuals.
2. Cost-Benefit Analysis
When weighed against the costs of assembling and sustaining an internal cybersecurity team, the cost-benefit analysis of outsourcing cybersecurity is substantial. The budgets of many firms, especially SME enterprises, may be strained by the significant expenditures in salary, training, and state-of-the-art technology that come with building an internal team.
When cybersecurity is outsourced, these fixed expenditures become variable costs, giving rise to a more adaptable financial model. This method spares companies from having to pay for services they don’t use or require, saving money on continuous operations.

Outsourcing allows businesses to more effectively use their resources. This, in turn, guarantees them professional cybersecurity support customized to their unique requirements without the costly overhead of full-time employees and technology expenditures.
To successfully manage financial restrictions and preserve a strong security posture, thoughtful financial planning is essential.
3. Scalability and Flexibility
Your company will inevitably need more sophisticated cybersecurity as it grows. This could be because it is expanding into new markets, dealing with more stringent rules, or handling more data overall.
By outsourcing cybersecurity, you can increase your security measures quickly and effectively without having to deal with the usual difficulties and hold-ups that come with hiring and onboarding additional employees.
Cybersecurity partners have the means and know-how to swiftly adjust to your shifting requirements. This is done by offering more coverage or specialized knowledge as needed. This degree of flexibility is essential for preserving strong security in a fast-paced corporate setting, ensuring that your defences can change to meet the appearance of emerging risks.
4. Enhanced Focus on Core Business Functions
By delegating security difficulties to cybersecurity professionals, your company may focus on its core competencies, such as innovation, market expansion, and customer service. This division of labor not only frees up your internal teams but also improves productivity and encourages creativity in your main tasks.
Employees may better apply their knowledge to support business development as long as they are not diverted by activities that are beyond their area of knowledge, such as handling the intricacies of cybersecurity management.
This strategic focus can result in more notable developments and successes in your primary company sectors while also facilitating greater efficiency.
5. Strategic Cybersecurity Partnerships
Strategic cybersecurity service collaborations are essential cooperative efforts that bolster your company’s strategic stance. They go beyond the simple economic relationship of employing an outside vendor. When you outsource cybersecurity, you collaborate with a company that functions as a component of your staff rather than merely hiring a service provider.
This synergy creates a safe environment that supports and facilitates your core operations, ensuring that the security tactics you deploy are in line with your larger business objectives. These collaborations also offer the vital advantages of round-the-clock monitoring and quick response times.
Therefore, it is critical to reduce losses due to cyberattacks. This round-the-clock watchfulness guarantees that any security problems are dealt with immediately, greatly lowering the chance and consequences of breaches.
Hence, connect with the right outsourcing cybersecurity partner.
When to Consider Outsourcing Your Cybersecurity Needs?
1. Determining Your Cybersecurity Needs
The first step in deciding whether to outsource your cybersecurity is to identify and evaluate your unique cybersecurity requirements. This entails determining which assets—private client information, creative works, and internal correspondence—must be protected.
It also entails evaluating the degree of internal security expertise that is currently accessible, as well as possible weaknesses. Small organizations may discover that the complexity of today’s cybersecurity requirements is more significant than what their internal resources can handle.
Outsourcing can quickly and effectively close any holes in your cybersecurity protections or deep knowledge that your study may have revealed.

Consider these points:
- Resource Limitations
- Need for Specialized Expertise
- Enhanced Security Measures
- After a Security Breach
2. Comparing Outsourced vs. In-House Security
Evaluating the advantages and disadvantages of outsourcing versus in-house security is crucial. Although they can be expensive and challenging to expand, in-house security teams give you direct control over your security procedures and instant access to the team.
However, compared to in-house security, outsourcing security gives you access to a group of professionals committed to staying abreast of emerging security risks and technology. This means that you can receive a broader spectrum of security knowledge.
Consider these points:
- Cost Efficiency
- Compliance and Regulatory Requirements
- Size of your business
- Rapid Growth or Scaling
- Focus on Core Business
How to Choose the Right Cybersecurity Outsourcing Partner?
Making the proper choice of cybersecurity outsourcing partners is essential to guaranteeing the protection of your company’s digital assets. When making this choice, keep the following crucial things in mind:

1. Expertise And Reputation
Seek out a collaborator with a solid background in cybersecurity. Review their experience managing security for companies like yours, looking for case studies and client endorsements.
2. Range of Services
Verify that the supplier provides an extensive selection of cybersecurity services, ranging from proactive threat detection to incident response and recovery, to meet your unique requirements.
3. Technological Capabilities
Consider the instruments and technologies that the supplier employs. Modern technology that can adjust to changing cyber threats should be used.
4. Industry Knowledge
The cybersecurity partner has to possess knowledge unique to your industry, including an understanding of frequent dangers that your sector’s enterprises encounter, as well as compliance difficulties.
5. Agility and Adaptability
Depending on your company’s expansion and evolving needs, the supplier must be ready to modify its services, either up or down.
6. Reporting and Communication
Good communication is essential. Make sure the supplier provides periodic updates on your safety record along with transparent reporting.
Ensuring Service Level Agreement (SLA) Compliance and Trust
When outsourcing cybersecurity, service level agreements (SLAs) are essential since they specify the parameters of participation and establish delivery standards. What should be included in an SLA with your cybersecurity supplier is as follows:
- Agreements to Reliability and Uptime
- Performance Metrics
- Response Times
- Criteria for Privacy and Compatibility
- Remediation and Penalty Clauses
- Data Management and Security
Best Practices for Outsourcing Cybersecurity

Let’s discuss some of the best practices that companies can use for outsourcing cybersecurity.
1. Managed Security Service Providers (MSSPs)
2. vCISO and Fractional CISO
3. Co-managed IT and Cybersecurity Partnerships
1. Managed Security Service Providers (MSSPs)
Companies trying to strengthen their cybersecurity position can find a wide range of security services from Managed Security Service Providers (MSSPs), who provide an extensive range of safety measures. Continuous risk tracking and identification, incident response, vulnerability oversight, and regulatory support are among the primary services provided by MSSPs.
These services are essential for companies without the internal manpower to monitor their networks for possible security breaches. MSSPs offer multilayer security defences that can dramatically reduce the risk of cybersecurity attacks by utilizing cutting-edge technologies and highly qualified staff.
Businesses that outsource to an MSSP might have access to advanced security knowledge and tools that would otherwise be too expensive to handle internally.
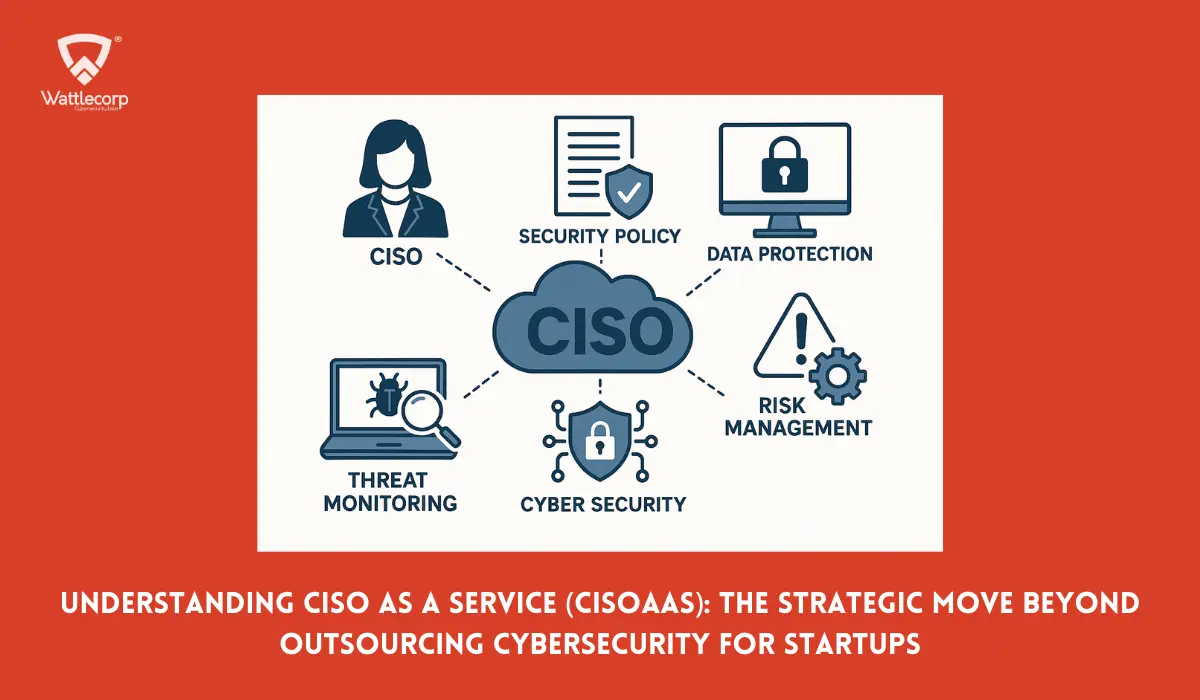
2. vCISO and Fractional CISO
When it comes to providing proactive cybersecurity leadership to companies that don’t need or can’t afford a full-time executive, the responsibilities of fractional CISO and virtual CISO are vital.
In order to match cybersecurity tactics with business goals, a virtual chief information security officer (vCISO) operates remotely and flexibly while providing the same high-level management and tactical analysis as a regular CISO.
In contrast, a fractional CISO offers strategic advice on a part-time basis, with an emphasis on crucial areas like risk evaluation, regulation, and the creation of cybersecurity policies.
These leadership roles are beneficial for small and medium-sized companies. This is because they allow them to gain executive-level knowledge without the corresponding full-time expenses. Thereby, it improves cybersecurity protection at a reasonable price.
3. Co-managed IT and Cybersecurity Partnerships
Co-managed IT refers to a cooperative approach whereby a business’s internal IT team collaborates with a third-party cybersecurity provider to augment its security competencies. In this strategy, the advanced knowledge and technology provided by outside professionals are combined with the skills of internal IT staff.

Co-managed IT has several advantages. This includes increased operational adaptability, specialist knowledge availability, and the capacity to scale safety measures. These are organizational requirements without requiring large capital expenditures.
Cybersecurity partnerships promote greater incorporation of security into operational procedures to guarantee that cybersecurity measures advance in step with business needs. Organizations that need a high degree of control over their IT systems but want the extra breadth and depth of knowledge that outside cybersecurity firms can offer may find this strategy very useful.
As this discussion has shown, there are numerous advantages to outsourcing cybersecurity. This acts as a catalyst to significantly improve the security posture of small enterprises and organizations with few IT resources.
Through the use of co-managed IT models, virtual or fractional CISOs’ strategic insights, and partnerships with MSSPs, organizations can obtain advanced technology and specialized knowledge without having to invest heavily in internal resources.
If your company is struggling to manage the intricacies of cyberattacks on a limited budget, it’s time to think about hiring a top cybersecurity outsourcing partner like Wattlecorp. Assess your cybersecurity requirements, consider your options, and select us, as we can provide customized solutions that strengthen your defenses against possible cyberattacks. We are in line with your business goals.
Frequently Asked Questions
Cybersecurity assignments that are essential to safeguarding an organization’s digital assets might be outsourced in several ways. The following are some typical cybersecurity duty areas that businesses frequently outsource:
1. Checking and recognizing risks
2. Addressing and Handling Incidents
3. Penetration testing and vulnerability analysis
4. Evaluations of Privacy and Adherence
5. Safety Audits and Assessments
6. Cybersecurity Awareness
You can outsource cybersecurity without sacrificing control. Instead, it entails establishing a collaborative relationship in which the parameters, responsibilities, and due dates are established through frequent communication and unambiguous agreements, guaranteeing congruence with your security protocols and corporate goals.
Examine the case studies, client endorsements, and certifications of your outsourced cybersecurity provider to confirm their credibility and trustworthiness. Make sure they adhere to industry norms and rules, and evaluate the transparency of their reporting and communication.