Key Takeaways:
- A simple URL change can reveal valuable financial information. The most frequent vulnerability that leads to an incident of data breach within SaaS platforms is Broken Object Level Authorization (BOLA) flaws, particularly when in a multi-tenant setup.
- Filtering manually does not completely secure your data; hackers can go round faulty logic, and it is essential to protect the sensitive information in high-growth platforms.
- Web app penetration testing will be necessary to make sure that your isolation layers stand the test, where ethical hackers pretend to attack it, in order to discover its vulnerabilities before real threats come in.
- When the physical data isolation of Row-Level Security and tenant-specific encryption are invested in, security can become a competitive advantage, earning the trust and enterprise contracts.
Table of Contents
Toggle- When SaaS Scale Becomes a Security Risk: Why Indian Platforms Struggle with Tenant Data Isolation
- Understanding Multi-Tenant Data Isolation in SaaS
- Common Security Risks in Multi-Tenant SaaS Platforms
- Advanced Data Isolation Controls for SaaS Security in India
- Securing 50K+ Records by Eliminating Tenant Data Exposure in an HR-Tech Platform
- How Web App Penetration Testing Secures Multi-Tenant Platforms
- Compliance and the Indian Regulatory Landscape
- Building for the Future of Indian SaaS
- Multi-Tenant Data Isolation FAQs
When SaaS Scale Becomes a Security Risk: Why Indian Platforms Struggle with Tenant Data Isolation
Imagine an Indian Fintech SaaS platform waking up to a nightmare: a Tier-2 tenant discovers they can view the financial statements of a Tier-1 enterprise client simply by changing a single digit in the URL.
Broken Object Level Authorization (BOLA) is a security issue where a system does not properly verify a user’s permission to access specific data objects, which can allow unauthorized access when object IDs are exposed in URLs or API parameters.
As the SaaS world in India explodes with some experts predicting a $50 billion valuation by 2030 the “blast radius” of one tiny security slip-up has never been bigger.
For any platform handling sensitive info, multi-tenant data isolation has moved from a “nice-to-have” feature to a strict legal and operational must.

The Digital Personal Data Protection (DPDP) Act 2023 has completely flipped the script on data responsibility.
As a “Data Fiduciary,” an Indian SaaS provider is now legally on the hook for any breach.
Under DPDP Act 2023, Data Fiduciaries remain responsible for ensuring compliance, including actions performed by Data Processors on their behalf. However, processors also have defined obligations and contractual accountability mechanisms.
For platforms trying to manage 50K+ records, the jump from a “scrappy startup” setup to an enterprise-grade environment often breaks down at the isolation layer.
Early-on, developers usually just filter by ID and a single logic bug can bypass that check, leading to a total cross-tenant mess.
Understanding Multi-Tenant Data Isolation in SaaS
Multi-tenant data isolation acts as a digital privacy wall, allowing different companies to share the same tech infrastructure while staying completely invisible to each other. In India’s evolving landscape, this is a strategic backbone.
Isolation is one technical safeguard that supports DPDP compliance, Indian SaaS providers usually weigh two options. There’s Logical Isolation and Physical Isolation. Logical Isolation shares a database to keep costs down, which is great for start-ups, but heavily reliant on perfect code.
Also Read : From Code to Cloud: How VAPT Secures SaaS Platforms at Every Stage
Physical isolation generally involves separate database instances, compute resources, or infrastructure boundaries per tenant. Separate schemas within one database are stronger logical segregation but not full physical isolation.
Physical isolation provides a significantly stronger privacy foundation, making it the preferred architecture for high-stakes SaaS environments.
Common Security Risks in Multi-Tenant SaaS Platforms
SaaS vendors are under constant pressure to secure data of their customers and ensure compliance. Ignoring basic security precautions can expand your vulnerability to tremendous proportions. To remain safe, it is necessary to avoid the following four traps:
- Weak Encryption: Using outdated or unauthenticated encryption modes leaves tenant data vulnerable to both decryption and tampering. Use authenticated encryption modes such as AES-GCM or ChaCha20-Poly1305, which provide confidentiality and integrity in a single operation.
- Cloud Misconfigurations: Open storage buckets or weak access controls are common due to the use of a cloud infrastructure. Audits of your cloud environment should be carried out regularly in order to avert illegal exposure.

- Inadequate Access Control: Without strict identity management and Multi-Factor Authentication (MFA), platforms are exposed to both insider threats and external attacks.
- Insecure APIs: As the backbone of SaaS connectivity, APIs are prime targets for cybercriminals. Protect your ecosystem by performing rigorous security testing to block injection attacks and other common vulnerabilities.
- Cross-Tenant Data Leakage: A classic authorization failure where User A can access User B’s data (e.g., via a guessed ID). Without strict logical boundaries, your data isolation is non-existent.
- Shared Resource Exploitation: In shared cloud clusters, a noisy neighbor or malicious actor can drain CPU/database resources. Effective isolation must protect both data privacy and system performance for all users.
Without tight multi-tenant data isolation, you run the risk of tenant bleeding, where data leaks through the cracks.
Advanced Data Isolation Controls for SaaS Security in India
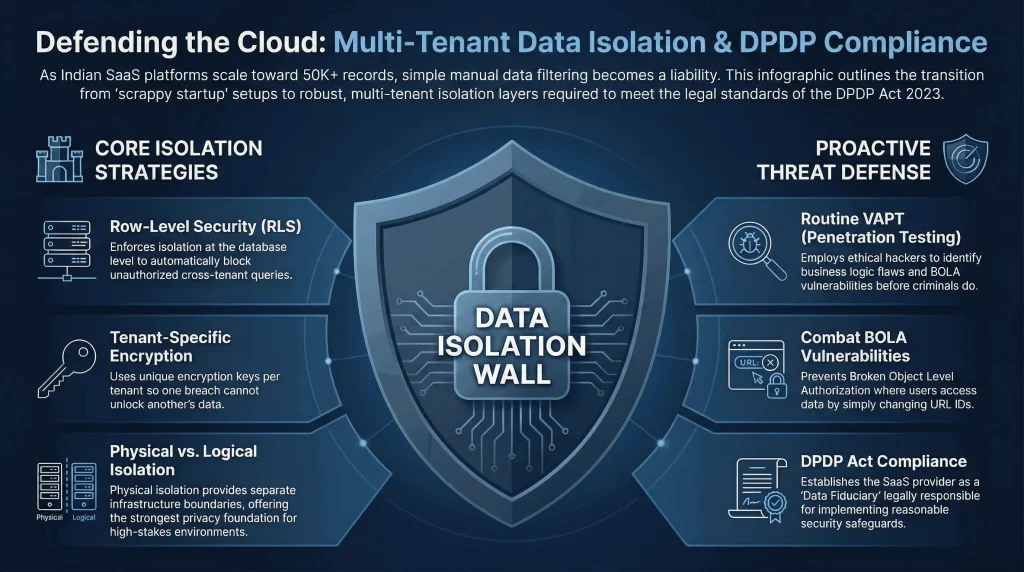
To meet the high security standards of the Indian market, SaaS security providers must move beyond basic filtering and adopt Row-Level Security (RLS) enforces access policies directly within the database engine (e.g., PostgreSQL RLS policies), ensuring query-level enforcement independent of application-layer logic.
- Row-Level Security (RLS): Instead of relying on manual code, RLS enforces isolation at the database level (e.g., in PostgreSQL). It automatically blocks queries that don’t match the active tenant’s ID, providing a high-performance safety net against cross-tenant leaks.
- Tenant-Specific Encryption: Standard encryption is no longer enough to keep strong security. By using unique encryption keys per tenant, you ensure that a breach of one client’s data cannot unlock another’s. This “individual lock” approach is essential for protecting sensitive enterprise data.

- Routine VAPT: Don’t wait for a breach. Schedule regular penetration testing to identify and patch vulnerabilities before they are exploited.
- Strict Access Control: Implement MFA and Role-Based Access Control (RBAC). This ensures users only access data necessary for their specific functions.
- Constant Oversight: Use real-time monitoring tools to instantly flag unauthorized logins or suspicious data movements, allowing for immediate intervention.
- Employee Training: Human error is a top leak source. Regular training on phishing and password hygiene transforms your staff into a primary line of defense.
To secure a platform for the Indian market, SaaS providers must move beyond basic defenses toward a proactive VAPT (Vulnerability Assessment and Penetration Testing) strategy that rigorously validates multi-tenant data isolation.
Securing 50K+ Records by Eliminating Tenant Data Exposure in an HR-Tech Platform
We recently worked with a major Indian HR-Tech player managing over 50,000 sensitive employee records. They hit a wall when their Shared Schema setup started failing audits; big enterprise clients simply didn’t trust their manual data separation.
To fix this, they moved away from shaky, code-based filtering and switched to PostgreSQL Row-Level Security (RLS).
This moved the safety net directly into the database engine. Beyond database-layer isolation, SaaS platforms typically rely on JWTs (JSON Web Tokens) to carry tenant identity from the application layer.
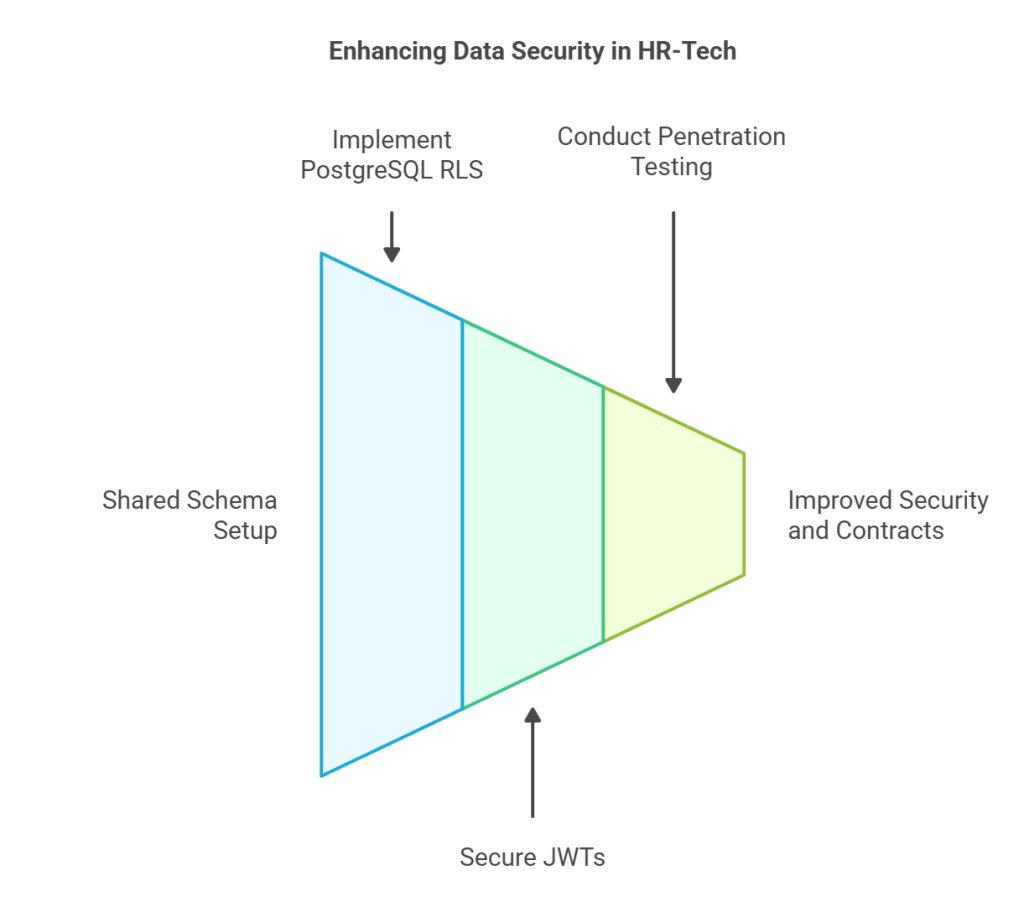
Securing these tokens through strong signing algorithms (e.g., RS256), strict signature validation, short expiration windows, and server-side claim verification significantly reduces tampering risk though it does not make it impossible.
To prove these new walls were solid, they brought in an expert team for web app penetration testing in India to try and poke holes in the system.
The shift paid off immediately. By turning their multi-tenant isolation from a liability into a core strength, they didn’t just pass their audits, they actually used their new security posture to win three massive enterprise contracts.
How Web App Penetration Testing Secures Multi-Tenant Platforms
You can’t just assume your code is perfect. In India, the only real way to know if your isolation and multi-tenant data isolation controls work is to try and break them.
Why multi-tenant testing is a different beast?
Automated scanners may miss business logic flaws unless configured with authenticated testing and role separation scenarios in India.
Also Read : Exploiting Firebase Database in a Web Application: A Security Analysis
For any SaaS company in India, regular penetration testing is no longer a luxury; it is a strong best practice and is often expected during enterprise due diligence. While it is not explicitly mandated by SOC 2, ISO 27001, or the DPDP Act, it plays a critical role in supporting compliance and demonstrating due diligence.
Compliance and the Indian Regulatory Landscape
The SaaS boom in India hasn’t gone unnoticed by the government. The DPDP Act is very clear and you must take reasonable security safeguards.
DPDP penalties are applied for failure to implement reasonable security safeguards or other statutory obligations, assessed by the Data Protection Board of India. Multi-tenant data isolation failure could contribute to such a breach, but penalties are case-dependent.
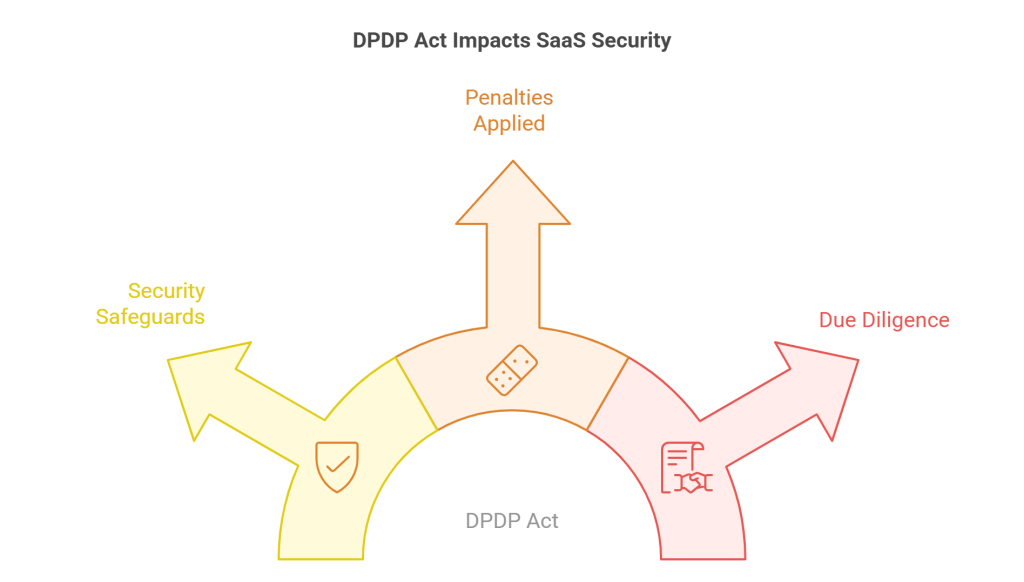
In a landscape where the Data Protection Board of India prioritizes preventative measures over damage control, strong multi-tenant data isolation stands as your most critical piece of evidence that your platform has acted with the requisite due diligence to protect its users.
Building for the Future of Indian SaaS
Solving multi-tenant data isolation is a journey, it is not a one-time fix. As your user base grows from 50,000 to 5 million, the pressure on those digital walls will only increase.
By layering database RLS, unique encryption keys, and continuous web app penetration testing india, you build a platform that people can actually trust.
Is your SaaS platform truly isolated? Don’t wait for a leak to show you the gaps. At Wattlecorp, we help Indian SaaS founders navigate the mess of data privacy and security architecture.
With expert support organizations can strengthen compliance, mitigate privacy risks, and protect sensitive data effectively by choosing Data Privacy Consulting Services in India.
Would you like me to run a quick security gap analysis on your current setup or give you a breakdown of how pentesting works in India?
Multi-Tenant Data Isolation FAQs
1.What is the role of multi-tenant data isolation?
Multi-tenant data isolation plays the major defense mechanism role whereby the data of each customer is logically or physically isolated on a common cloud platform. This isolation is useful in avoiding the accidental data leak, and also, proper multi-tenant isolation greatly reduces the likelihood that one user session can access sensitive data belonging to another tenant.
2.How does multi-tenant data isolation protect customer data?
The system prevents a tenant from querying the records of another tenant by placing technical obstacles such as Row-Level security (RLS) or even distinct database schemas. RLS acts as a critical fail-safe at the database level, ensuring that even if an application bug is exploited, the attacker can only access rows belonging to the tenant context set in the session, provided the application connects using a restricted, non-superuser role and RLS policies are correctly configured.
3.What are the risks of not isolating tenant data in SaaS?
The most short-term risks involve colossal data breaches, loss of client trust, and harsh legal consequences in accordance with the DPDP Act in India. Moreover, inadequate isolation may cause performance degradation in which the heavy usage by a single tenant affects the ease of access of the entire platform by other tenants.
4.How can SaaS platforms implement tenant isolation strategies?
Platforms have the option of logical separation by a single database with rigorous filtering, or physical separation by providing a schema or database instance per client. A significant number of recent SaaS solutions in India also use tenant-specific encryption keys so that information cannot be read by anyone, even in cases when the underlying storage is affected.
5.How does web app penetration testing help secure multi-tenant SaaS platforms?
It involves ethical hackers purposefully attempting to penetrate your isolation layers so as to determine vulnerabilities before the actual attackers. This preventive testing validates your authorization logic against known attack patterns and identifies exploitable gaps between tenant environments, providing a point-in-time security assurance that should be repeated after significant platform changes.







