OT Security And Risk Assessment Services
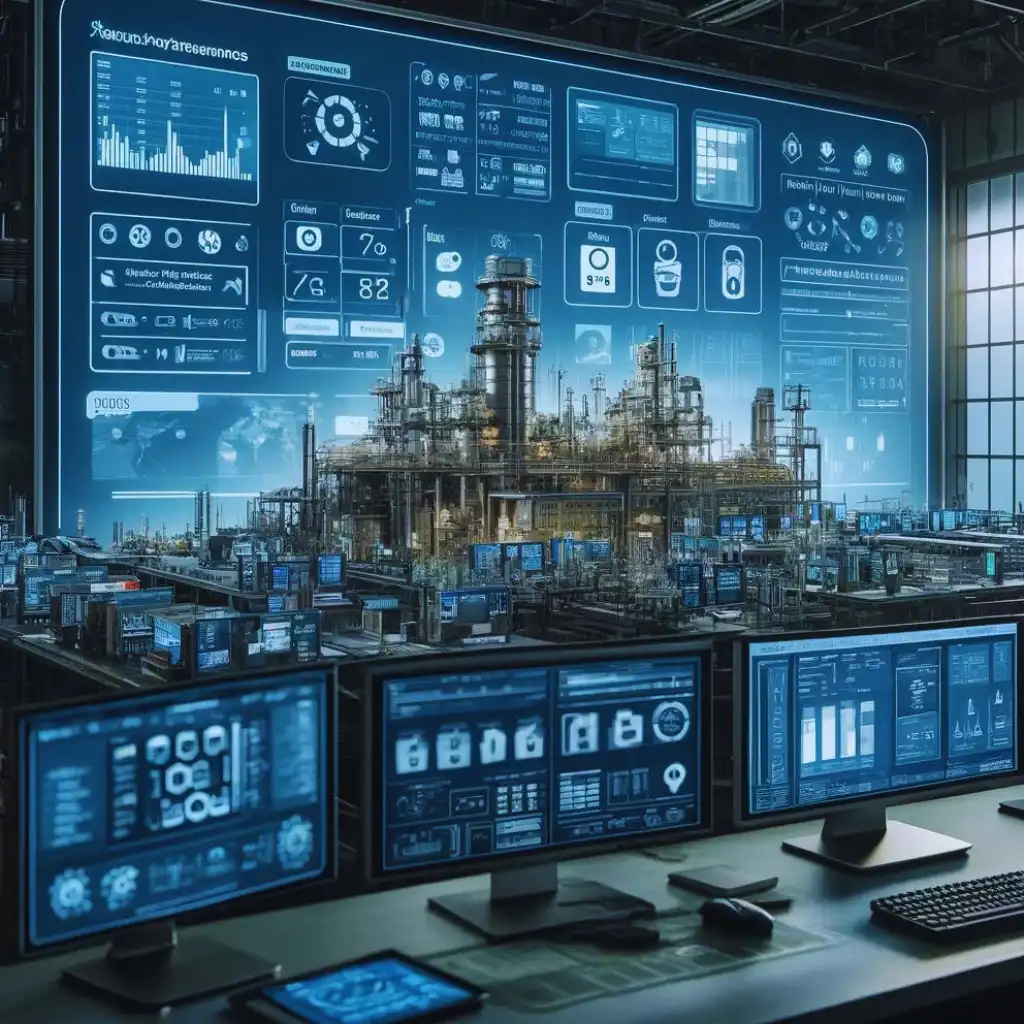
Secure people, assets, and information about your Qatar’s industrial networks and critical infrastructures with experts at Wattlecorp
What is OT Security Assessments
Operational Technology security effectively utilizes software and hardware to assess and secure the processes, divides, and infrastructures. They are usually found across asset-intensive platforms that perform operations from monitoring critical infrastructures constantly to controlling heavy machinery. Next-generation firewalls and security information and event management (SIEM) systems are used in this process to identify access and management.

Benefits of conducting OT Security Assessments
A small incident in critical infrastructure would be a catastrophe for the environment, the public, and the nation’s economy.
Implementing the right operational technology security with the assistance of experts helps to enhance safety and reliability through the adoption of preventive measures against intrusions and cyberattacks.
Preventing costly disruptions and damages while complying with various global data privacy standards is yet another benefit of the same. Customer trust and maintaining brand reputation also come with it.
Scoping
The first stage is to determine the parameters and needs. To ensure end-to-end assessments, the assets that fall under the operational technology category are identified. These assets range from network devices to sensors and controllers.
Vulnerability assessment
The devices, applications, and networks are examined for vulnerabilities using a standardized threat checklist with decision-makers consent and a defined scope.
Impact analysis
Vulnerabilities in your operational technologies are evaluated and then examined to see how they affect your business and estimate possible damages. Determining the probability of being exploited and the extent of access that an attacker would be able to obtain in an actual incident is helpful.
Documentation
The findings, appropriate screenshots, and techniques and procedure used to find the vulnerabilities, along with practical remedial recommendations for effective remediation are summarized as a report tailored according to your business requirement.
Listen to People
We help companies to protect their online assets.
Checkout our Services
F.A.Q
We have something for everyone, including pricing and answers.
Tip • Book a consultation to get personalised recommendations.
Start OT Security Assessments Now!
All you need to do is fill the form below.
Recommended Cybersecurity Services
Officially recommended by Hackers.
ICS SCADA Security Testing
Protect your industrial control systems and SCADA networks with our specialized security testing services, mitigating the risk of cyber attacks.
Qatar Cybersecurity Framework
Achieve compliance with the Qatar Cybersecurity Framework by implementing robust security measures tailored to protect your digital assets.
Personal Data Protection Law
We assist you in achieving compliance with Qatar's Personal Data Protection Law, safeguarding personal data and ensuring legal adherence.
ISO 27001 Consulting
Achieve ISO 27001 compliance with our expert guidance, implementing best practices to safeguard your information assets and ensure data security.
Recent Articles
stay up to date with recent news.

Internal Penetration Testing: Why It’s Essential for Organizational Security

The Business Impact of Compliance Failures in SaaS

