Key Takeaways:
- Air-gapped assumptions are outdated. IT/OT convergence has significantly expanded the attack surface of industrial control systems (ICS) in Saudi Arabia.
- OT cyberattacks cause physical consequences. Unlike IT breaches, ICS compromises can result in equipment damage, production shutdowns, environmental harm, and risks to human life.
- Legacy protocols increase exposure. With industrial protocols like Modbus and DNP3 lacking encryption and authentication, they tend to become vulnerable to interception and manipulation.
- Flat networks and weak remote access serve as major entry points, making way for lateral movement from IT into OT through poor segmentation and unsecured vendor connectivity.
- Traditional IT security alone is insufficient. OT environments require security controls that respect real-time operations, uptime, and safety constraints.
- Frameworks like NIST SP 800-82 and IEC 62443) provide structured guidance. This helps build risk-based, defense-in-depth OT security programs.
- Continuous visibility is critical. Asset inventory, ICS-aware monitoring, and protocol-level inspection are foundational to OT resilience.
- Risk-based VAPT strengthens validation. Integrated into OT security endeavours, it helps identify exploitable weaknesses without disrupting plant operations.
Industrial organizations once believed their plants were safe because “air-gapped” control networks kept cyber risk at bay. That assumption is now dangerously outdated given the pace at which cyber risks are rising.
Modern industrial control systems (ICS) and supervisory control and data acquisition (SCADA) environments are increasingly connected to IT networks, remote vendors, cloud platforms, and analytics tools. While connectivity to this extent helps improve efficiency and visibility, it carries significant risks of exposure to sophisticated cyber threats for critical physical processes, especially in Middle-East lands like Saudi Arabia.
From power grids and oil refineries to water treatment plants and manufacturing lines, operational technology (OT) is now a frontline cyber battlefield.
Notable attacks by Stuxnet and TRITON have demonstrated how critical ICS protocols and devices, such as PLCs (Programmable Logic Controllers) and the safety instrumented systems (SIS) can be dangerously manipulated to cause high-impact operational disruptions and life-threatening events through complex interactions. Where incidents like these highlight vulnerabilities within the OT environments, exploiting them through advanced techniques, say manipulation of firmware and system logic do produce disruptive impacts of a higher magnitude.
This article explains why OT/SCADA security has become crucial to protecting industrial control systems from evolving cyber threats in Saudi Arabia. It mentions the sophisticated attack vectors that adversaries use, the real-world consequences of a successful breach, and how frameworks like NIST SP 800‑82 and IEC/ISA 62443 can guide a practical, continuous security program.
Table of Contents
ToggleUnderstanding the Real OT/SCADA Threat Landscape
OT and SCADA systems were predominantly (and historically) designed to prioritize reliability, availability, and most importantly, safety above anything else. Even cybersecurity was an afterthought in these efforts. Many still rely on legacy hardware and protocols such as Modbus, DNP3, and ICCP that lack basic protections like encryption and authentication, making them vulnerable to interception, spoofing, and replay attacks.
At the same time, IT/OT convergence has fundamentally changed the risk profile. Plants that were previously isolated are now connected to enterprise networks, remote operations centers, vendor support portals, and sometimes directly or indirectly to the internet. An expanded connectivity like this tends to create more paths into control networks and more opportunities for attackers to get a foothold into OT from IT.

Threat actors targeting ICS and SCADA are not limited to script kiddies and can also include:
Nation-state groups that seek strategic disruption of critical infrastructure or industrial espionage.
Cybercriminals deploying ransomware to halt production or threaten safety to force payment.
Insiders or contractors with knowledge of systems and privileged access.
Notable real-world examples have included campaigns like Stuxnet, which sabotaged Iranian centrifuges by reprogramming PLCs, and TRITON targeting Schneider Triconex’s safety instrumented systems. Both these incidents highlight the sophistication and patience at which modern ICS-focused adversaries commit to cyberattacks. These are not theoretical risks; but are proven, repeatable attack patterns that others can now copy.
The Common Attack Vectors that Target Industrial Control Systems
– Legacy and unpatched systems
OT assets tend to run frequently on unsupported operating systems and firmware for 10–20+ years. A situation like this cannot be practically reverted because of costly downtimes, making security patches delayed or even skipped altogether. All these leave enough known vulnerabilities that lie exploitable for years.
– Unsecured remote access and vendor connections
Remote maintenance via VPN, RDP, or vendor-specific tools if not properly configured or authenticated, can significantly increase exposure risks by potentially bypassing security controls. Misconfigured or shared accounts, weak authentication, and exposed services allow attackers to walk into OT networks once IT defenses are breached.
– Flat or poorly segmented networks
Many ICS environments do not come with strong network security features like segmentation, one that can distinctly separate IT and OT or different process zones. Flat networks and weak DMZ architecture can make way for easy lateral movement to critical ICS segments like PLCs, HMIs, historians, and engineering workstations once an attacker compromises one system.
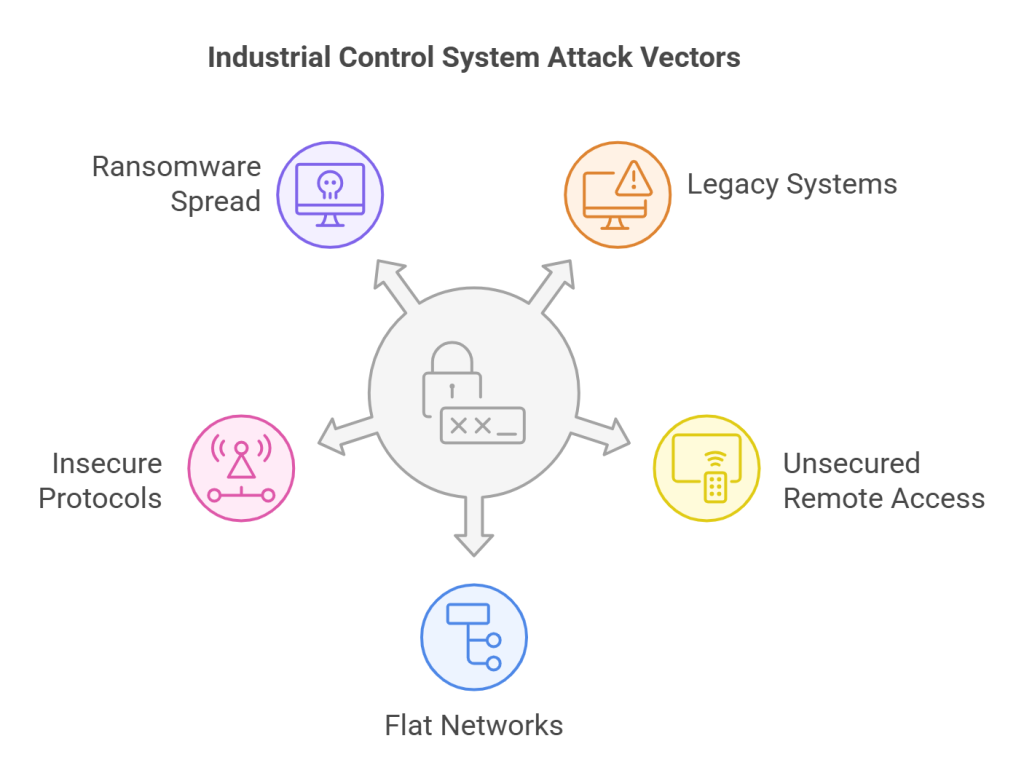
– Insecure industrial protocols and device interfaces
There exist some industrial protocols, such as Modbus and DNP3 that transmit commands and telemetry in clear text without undergoing integrity checks, making them vulnerable to interception. With the attackers constantly monitoring network communication channels, flaws like these can enable them to map critical processes.
The Stuxnet case of 2010 is a prime example for physical operational disruptions due to ICS compromise. The lack of proper authentication and encryption of the Modbus and DNP3 protocols gave enough opportunity for the attackers to inject and replay malicious commands. This led to manipulated and malfunctioning centrifuge operations at the Natanz Nuclear Facility.
– Ransomware and commodity malware spread
As OT and IT converge, ransomware that enters through corporate email or endpoints can propagate into ICS environments, encrypting HMIs, servers, and even engineering workstations. Operators may lose visibility and control despite the knowledge that PLCs are untouched or uninvaded.
Effective OT/SCADA security focuses on breaking this killer chain. This can be done through hardening initial entry points, limiting lateral movement, and detecting anomalous activity on ICS assets and protocols.
Real-World Consequences that Interrupted Industrial Operations
Operational Technology-based incidents are more dangerous than IT counterparts. While the latter primarily involves data breaches and financial fraud, for the former, the impact can be fatal enough to endanger life in terms of:
– Operational downtime and lost production
A successful attack within the OT environment means shutting down of lines, disruption in batch processes, or one that triggers emergency shutdown of essential systems. In TRITON for instance, the misbehaving SIS controllers caused an unplanned shutdown, thus exposing malware presence.
A short outage, be that in critical infrastructure or high-throughput manufacturing, is enough to result in massive financial losses.
– Damage to equipment and infrastructure
Malware like Stuxnet altered PLC logic to change centrifuge speeds, causing physical stress on equipment.
At the same time, refineries, pipelines, or power plants manipulations can give rise to high-impact catastrophes like equipment failure and fires.
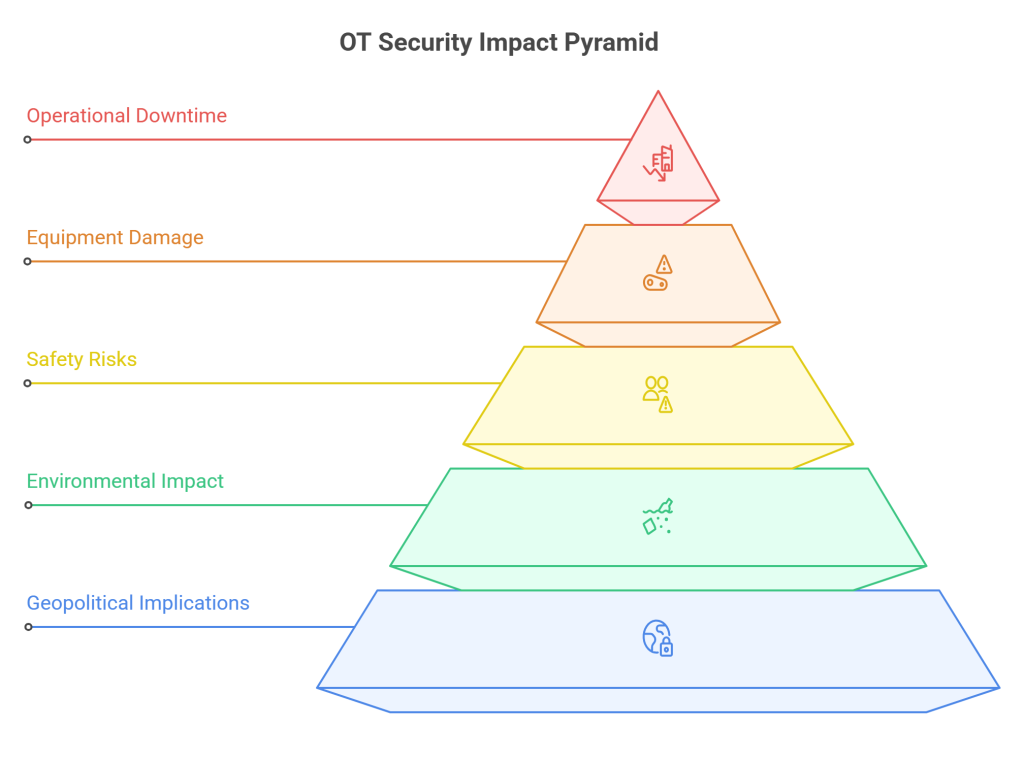
– Compromised safety and risk to human life
The most alarming aspect of TRITON was its focus on safety instrumented systems that were designed to protect people and assets. However, attackers could sneak into to create unsafe conditions by disabling or manipulating SIS logic, without triggering alarms, putting workers and nearby communities in danger.
– Environmental and regulatory impact
Disrupted control of chemical processes, pipelines, or water treatment have resulted in massive spillage, contamination, and uncontrolled releases, further resulting in environmental damage, regulatory penalties, and long-term reputational harm.
– Strategic and geopolitical implications
Attacks on power grids, transportation, or oil and gas infrastructure can have national security implications and influence geopolitical negotiations. All these can eventually and drastically undermine public trust in critical services.
OT/SCADA security moves beyond being just a cybersecurity issue to a core business, safety, and regulatory priority.
Why Industrial Control Systems Need OT/SCADA Security
Because OT systems come with unique characteristics, traditional IT security controls alone cannot secure ICS environments.
Strict real-time and availability requirements: Security controls should be dynamic (time-bound) and reliable enough to effectively prevent disruption of critical industrial processes.
Legacy and proprietary technologies: Many devices lack built-in security agents or support only limited updates.
Safety and reliability priorities: Operations teams are rightly focused on keeping the plant running safely. Any security strategy proposed, should be implemented on this understanding.
Also Read : Firewall Security Explained: How to Protect Your Network from Cyber Threats (2025 Guide)
OT/SCADA security understands the above limitations and tailors cybersecurity practices to the industrial environments unique needs. It incorporates:
Comprehensive ICS asset, configuration, and communication visibility
Protocol-specific Modbus, DNP3, PROFINET, and other industrial protocol monitoring
Process and safety interdependencies risk-based segmentation
IT, OT, Engineering, and safety collaboration
In short, OT/SCADA security ensures that plants can safely embrace digitalization, remote operations, and data-driven optimization without leading to untoward cyber-physical risks.
Essential Frameworks & Standards (Enablers, Not Checklists!)
NIST SP 800-82 and IEC/ISA 62443 have emerged as the two primary references to anchor OT security programs. Used in conjunction, both of them help build a comprehensive, structured, and risk-based Operational Technology Security Program for industrial organizations.
NIST SP 800‑82, the OT Security Guide
This publication supports understanding of the OT-specific risks, applying risk management to ICS, and designing architectures that balance security with performance and safety. It also emphasizes:
- OT Cybersecurity Policies and Oversight Processes.
- Vulnerability Assessment with Risk Management for OT/ICS.
- Secured Remote Access with Defense-in-Depth Architectures.
- Incident Response in OT Contexts.
Also Read : Key Cybersecurity Threats Addressed By VAPT In 2025
IEC/ISA 62443: Industrial Automation and Control Systems Security
IEC/ISA 62443 introduces the concepts of security zones and conduits. Grouping assets with similar risk profiles is the prime intent here, defining controlled communication pathways between them simultaneously. Then follows setting security levels against different threat capabilities with equal attention placed on safeguarding the OT lifecycle (design, integration, operations, and maintenance).
NIST 800‑82 provides the risk management lens and high-level program structure, while IEC/ISA 62443 offers detailed technical controls and architectural patterns.
When treated as enablers rather than checklists, these standards:
- Support regulatory and customer assurance without encouraging “compliance-only” thinking.
- Help align IT, OT, and management around a common language for risk.
- Guide prioritization of controls based on process criticality and threat levels.
The goal is not “ticking all boxes,” but to use these frameworks to make informed, defensible trade-offs that keep people safe and operations resilient.
Key Challenges and How OT/SCADA Security Helps Solve Them
Industrial organizations, most of them, face similar obstacles when securing their ICS environment:
– Legacy systems and long asset lifecycles
Challenge: Devices that remain unpatchable or cannot be upgraded without major downtime.
Solution: Compensating controls, such as network segmentation, mandate list-based firewalls, protocol-aware intrusion detection, and strict physical security to reduce exposure for unpatchable assets.
– Limited insight into OT assets and traffic
Challenge: Limited asset listing, unidentifiable firmware versions, and obscure communication.
Solution: Continuous network discovery and deep-packet inspection of ICS-protocols to pattern device, firmware, logic alterations, and normal baseline without operational disruptions.

– Organizational silos between IT and OT
Challenge: Presents via differing priorities;-security for some, uptime for others, further complicating things with varied terminology and governance structures.
Solution: Building a cross-functional OT security team, one that integrates engineering, operations, safety, and cybersecurity for efficiently handling shared risk assessments and workflows.
– Resources and Specialized Skills Constraints
Challenge: Appointing professionals with practical knowledge of ICS and cybersecurity operations.
Solution: Manage OT security services and vendor solutions built for plant environments, combined with training for operators and engineers on OT-specific cyber risks.
– Managing Third Party and Supply Chain Risk
Challenge: Vendors, integrators, and remote support providers need access into control network down to root-level.
Solution: Onboarding process standardization for vendors, segregating (segmenting) network access at remote sites, implementing strong authentication, real-time monitoring of vendor activities, and facilitating security contractual requirements in a uniformed manner.
A mature OT/SCADA security program directly addresses these challenges by combining technology, process, and governance tailored to industrial realities.
Best Practices for Continuous Security
OT/SCADA security isn’t a one-time project; rather it’s an ongoing discipline that moves in accordance with the industrial assets and processes lifecycle. Key best practices in this regard include:
1. Build and maintain an accurate OT asset inventory
Discover and manage operational technology assets continuously by utilizing specialized non-intrusive and automated tools. These include PLCs, RTUs, HMIs, and engineering workstations, network devices, and their firmware/OS versions.
Facilitate risk-based controls through assets classification based on the latter’s criticality, impact, and connectivity.
2. Utilize Zones and Conduits to Segment Networks
Separate (segment) Industrial automation and control systems (IACS) specific to their risk, function, and consequences by applying IEC/ISA 62443’s zone-based model and conduits. This will help prevent cyber threats via lateral spread.
Use industrial firewalls and data diodes where felt necessary with strict policy control over protocol and command types.
3. Harden remote access and vendor connectivity
Adopt a defense-in-depth approach, preferably a Zero-Trust Architecture to set up stronger authentication, principle-of-least privilege, and time-bound access for remote sessions, effectively balancing cybersecurity rigidity and operational uptime.
Centralize, log, and monitor remote entry points to OT assets for preventing unauthorized access, thus averting ransomware attacks and operational disruption.
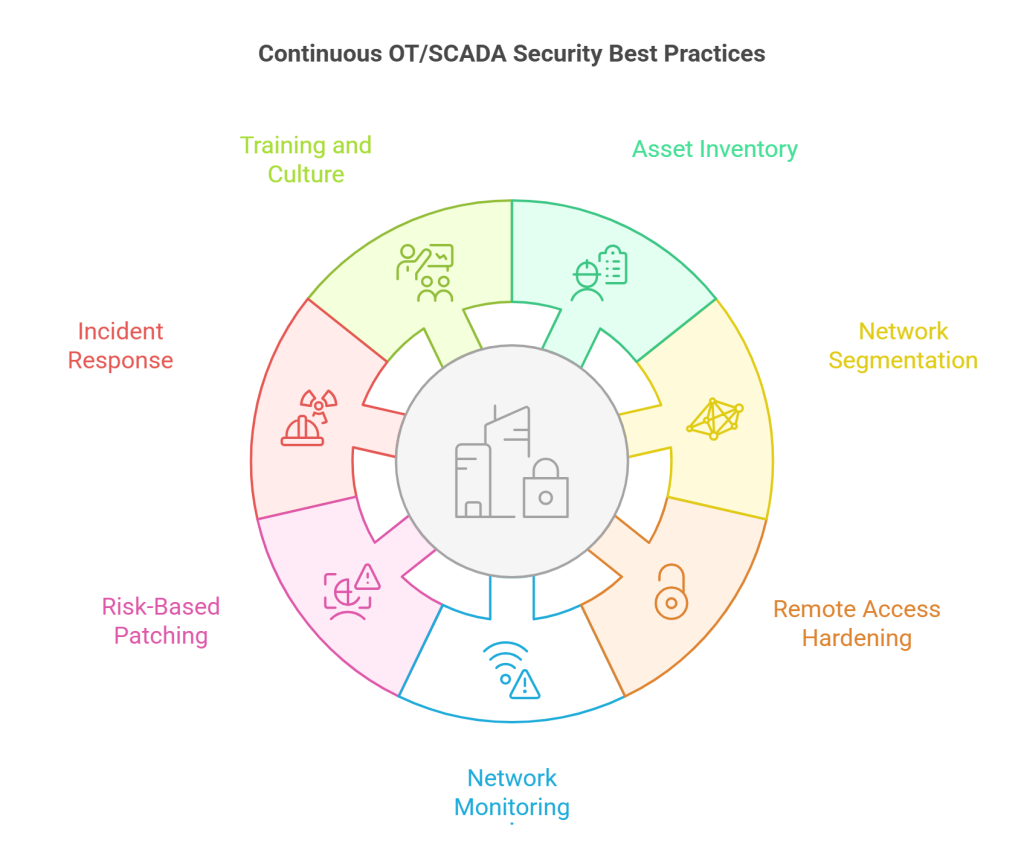
4. Monitor OT networks with ICS-aware tools
Utilize network sensors that help establish passive monitoring and also detect anomalous commands, new devices, or unauthorized configuration changes within the industrial protocols.
Integrate OT telemetry into a broader SOC or specialized OT security operations function.
5. Adopt risk-based patching and compensating controls
Prioritize vulnerabilities based on their exploitability and process impact by utilizing NIST 800‑82 guidance.
Adopt risk-based strategy covering segmentation, access control, and continuous monitoring until planned maintenance window if patching is not immediately possible.
6. Integrate OT into incident response and resilience planning
Develop OT-specific playbooks for predominantly enabling operational continuity via safe shutdown or manual override procedures. These should be carried out in close coordination with engineers, plant operators, and the safety teams.
Regularly test scenarios to ensure OT security. Advanced security testing methodologies like vulnerability assessment and penetration testing (VAPT) effectively help in this regard.
From identifying vulnerabilities to simulating real-world attacks, VAPT significantly helps prevent attacks through ransomware that may hamper HMIs (Human-Machine Interfaces), causing unauthorized logic changes to PLCs (Programmable Logic Controllers) and loss of visibility into key systems.
7. Invest in training and culture
Train operators, engineers, and maintenance teams on recognizing-cum-reporting cyber-physical risks, phishing attempts, and unsafe workarounds.
Reinforce the message that safety, reliability, and security are mutually reinforcing objectives, not competing ones.
Closing Thoughts
In an industrial setting, operational continuity, uptime, and security matter the most. Hence, relying on legacy systems solely is no longer a sustainable strategy. As far as safe handling of critical equipment is concerned, an extensive integration of OT into high-profile security testing methodologies like VAPT is the key.
With adversaries continuing to target the ICS environment by refining ICS-focused tools and techniques to exploit critical infrastructure, these significantly herald expanding attack surfaces, especially as IT and OT continue to converge.
By embracing frameworks like NIST SP 800‑82 and IEC/ISA 62443 as practical guides industrial organizations can gain a more customizable and flexible approach to securing OT. Such a protection should respect the uptime requirements of plant operations.
However, the effectiveness of these frameworks depends on how well they are validated against real-world scenarios. Here is when it becomes critical to undertake a structured, risk-based security testing.
Wattlecorp supports identifying exploitable weaknesses for industrial organizations by applying OT-based VAPT methodologies across PLCs, SCADA systems, industrial networks, and remote access pathways. Aligned with the concerned frameworks, VAPT assessment (done regularly) helps ensure optimal security without disrupting plant operations.
With OT/SCADA security and risk assessment has now become central to protecting industrial control systems from cyber threats, we prioritize vulnerabilities for the operational and safety impact they carry. This helps us undertake remediation efforts that while strengthening cyber resilience for the OT environment, also assists in preserving availability.
With continuous visibility gained for ICS assets, followed by network segmentation, OT-aware monitoring, and close collaboration between IT, OT, and safety teams, these combined with the proposed VAPT-led security approach help transforms cybersecurity from a reactive cost center into a proactive enabler of safe, reliable, and digitally empowered industrial operations.
Validate your OT/SCADA security controls with a risk-based, OT-aware VAPT aligned with NIST SP 800-82 and IEC/ISA 62443.

OT/SCADA Security FAQs
1.What is OT/SCADA security?
OT/SCADA security primarily serves to protect industrial control systems by handling critical physical processes.
By involving its key components, i.e., PLCs (Programmable Logic Controllers), HMIs (Human-Machine Interfaces), RTUs (Remote Terminal Units), and SCADA (Supervisory Control and Data Acquisition) platforms. OT/SCADA security helps prioritize availability, safety, and process integrity, also serving to mitigate cyber risks in industrial environments on a simultaneous basis.
2.Why is OT/SCADA security critical to protecting industrial organizations?
OT/SCADA systems help control critical infrastructure that includes manufacturing, oil and gas, power, and water utilities. With Cyber incidents rising stupendously in these environments, predominantly to cause operational disruption, these can simultaneously lead to equipment damage, safety risks, regulatory impact, and even loss of life. All these are critical concerns that make OT security a core operational requirement.
3.How is OT/SCADA security different from traditional IT security?
As opposed to the traditional IT security, OT environments are reliant on both legacy technologies and real-time operations that promote system uptime to a great extent. OT security is equally focused on maintaining operational continuity and safety by requiring specialized controls, tools, and testing approaches that exclusively cater to the industrial environments.
4.What role does OT-aware VAPT play in securing OT/SCADA environments?
The OT-aware Vulnerability Assessment and Penetration Testing (VAPT) intervention is pivotal to helping identify exploitable weaknesses across the industrial networks, control systems, and remote access pathways. By validating security controls using controlled, non-disruptive methods aligned with operational and safety requirements, the OT-aware VAPT involves a proactive cybersecurity approach that emphasizes operational continuity, process integrity, and safety.
5.What are the frameworks that guide effective OT/SCADA security programs?
NIST SP 800-82 and IEC/ISA 62443 are the key reference frameworks that offer a structured guidance to securing industrial control systems. By helping organizations design, implement, and validate risk-based OT security programs, both NIST SP 800-82 and IEC/ISA 62443 assist with balancing cyber resilience with uptime requirements.