Key Takeaways:
- A comprehensive VAPT report provides a structured view of your organization’s security posture, with identifying vulnerabilities, exploitation risks, and their potential business impact.
- Understanding the key sections of a VAPT report such as executive summary, scope, findings, CVSS scores, remediation guidance, and compliance mapping helps to prioritize security actions effectively.
- CVSS scores indicate vulnerability severity, but the priority to focus on the actual business risk depends on the criticality of the affected asset within your organization.
- A phased remediation strategy ensures VAPT findings lead to measurable security improvements, covering immediate fixes, systematic remediation, and long-term security hardening.
- A well-documented VAPT report supports regulatory and audit readiness for Indian organizations aligning with DPDPA, CERT-In guidelines, RBI cybersecurity frameworks, and ISO 27001.
Table of Contents
Toggle- From Findings to Action: A VAPT Report Guide Built for Indian Enterprises
- A Practical Guide to Understanding What a VAPT Report Covers
- Breaking Down the Structure: What a Strong VAPT Report Contains
- Reading CVSS Scores Without Getting It Wrong
- Turning VAPT Findings into a Practical Remediation Roadmap
- Why Compliance Mapping in a VAPT Report Matters
- Why VAPT Has Become Essential for Indian Enterprises
- Mobile App Penetration Testing: India’s Fastest-Growing Security Gap
- Strengthening Security Posture with Wattlecorp’s Expert Support
- VAPT Report Guide FAQs
From Findings to Action: A VAPT Report Guide Built for Indian Enterprises
Most Indian organisations conduct VAPT because they have to or a client requested it, a regulator expects it, or an internal policy requires it. Far fewer treat the resulting report as the compliance and risk management resource it genuinely is.
That distinction matters. A VAPT report done right captures far more than a list of vulnerabilities.
It documents the security posture of your organization at a specific point in time, maps weaknesses against recognised control frameworks, and provides the remediation evidence that auditors and increasingly, insurers and enterprise clients expect to see.
In India’s current regulatory climate, where the DPDPA, RBI guidelines, and CERT-In mandates are creating overlapping accountability requirements, that documentation has real business value beyond the security team.
The VAPT report guide is written for the professionals responsible for making that value tangible like CISOs building a defensible risk narrative, GRC teams preparing for audits, and security heads translating technical findings into organised remediation programmes.
The goal is straightforward, a VAPT report complete guide helps your organisation get more out of a VAPT engagement than a one-time vulnerability list.
A Practical Guide to Understanding What a VAPT Report Covers
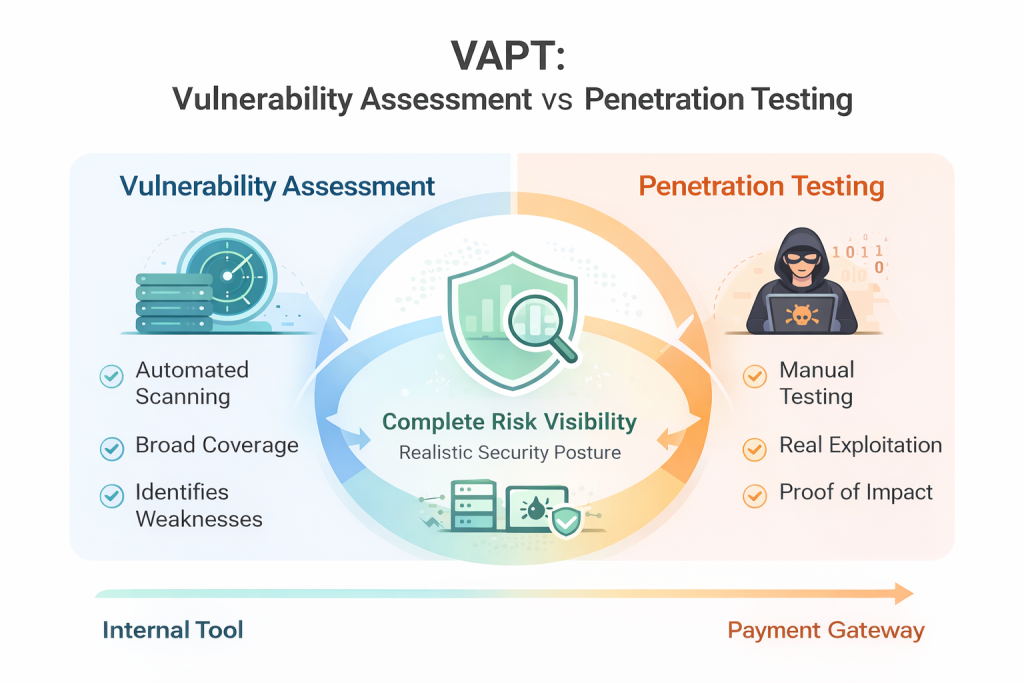
A VAPT report guide is not just a list of bugs. It is the output of a structured, expert-led exercise that combines automated vulnerability discovery with manual penetration testing and the two are very different things.
Vulnerability assessment finds the gaps. Penetration testing proves they can be exploited. Together, they give you a realistic picture of where your defences stand right now.
For businesses in India, this matters more than ever. The Digital Personal Data Protection Act, CERT-In’s mandatory reporting guidelines, and RBI’s IT framework for banks have collectively raised the stakes around cybersecurity accountability.
Organisations that treat VAPT as a one-time audit exercise rather than a continuous risk management tool are leaving themselves exposed on multiple fronts.
The purpose of a VAPT report guide is to provide clarity on what is covered and excluded in a VAPT report.
Breaking Down the Structure: What a Strong VAPT Report Contains

The effectiveness of a VAPT report depends heavily on its structure. Poorly organized reports obscure critical findings with unnecessary technical noise, while well-constructed reports deliver clear, actionable insights for both technical experts and executive stakeholders.
Here is what every credible VAPT report guide recommends including:
- Executive Summary: Risk posture at a glance, written for leadership, not engineers. Critical findings, business impact, and top-line recommendations.
- Scope and Methodology: What was tested, how it was tested, and what was deliberately excluded. This section is more important than most people realise.
- Vulnerability Findings: Each issue documented with affected asset, root cause, evidence, and a proof-of-concept where relevant.
- CVSS Scores and Severity Ratings: Standardised scoring that allows your team to prioritise without second-guessing.
- Remediation Guidance: Specific, technically actionable steps. Not “patch your systems.” Rather, which patch, applied where, verified how.
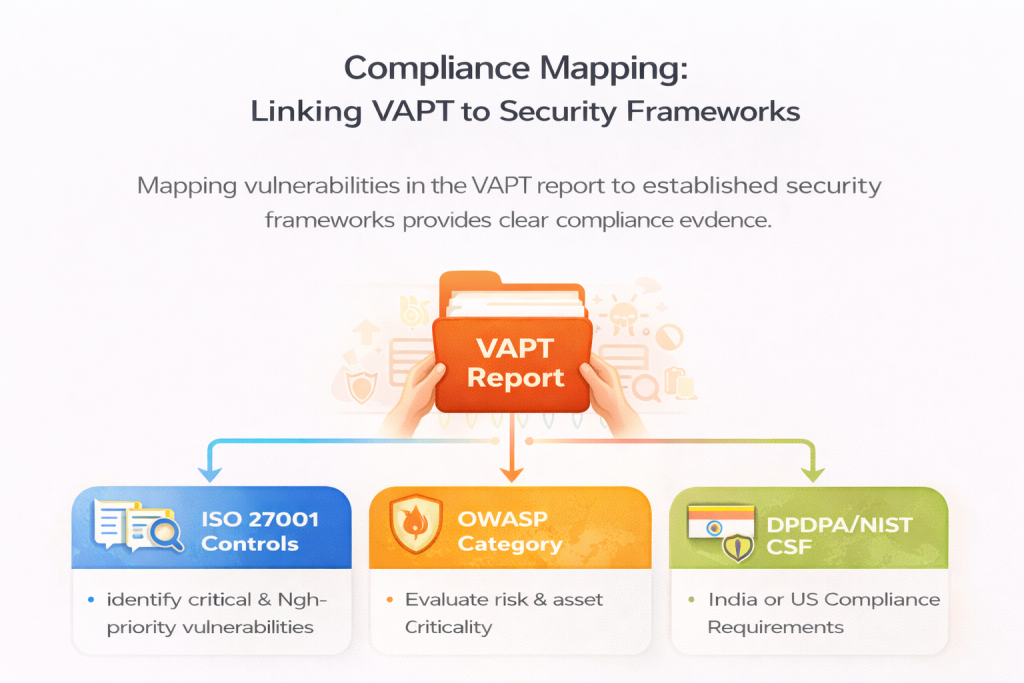
- Compliance Mapping: Linking findings to ISO 27001 controls, OWASP categories, or India-specific regulatory requirements.
Security teams in India who understand sections of the VAPT report guide, rather than forwarding the PDF to development and hoping for the best consistently achieve faster remediation and cleaner audit outcomes.
Reading CVSS Scores Without Getting It Wrong
Security teams often treat CVSS scores as the final word on priority. In practice, they are a starting point and misreading them is one of the most common mistakes organisations make when working through a VAPT report guide.
CVSS scores are only the starting point; true prioritization requires weighing asset value and potential business disruption. A vulnerability on a public-facing server carries more weight than the same flaw on an isolated system because the business impact is significantly greater.
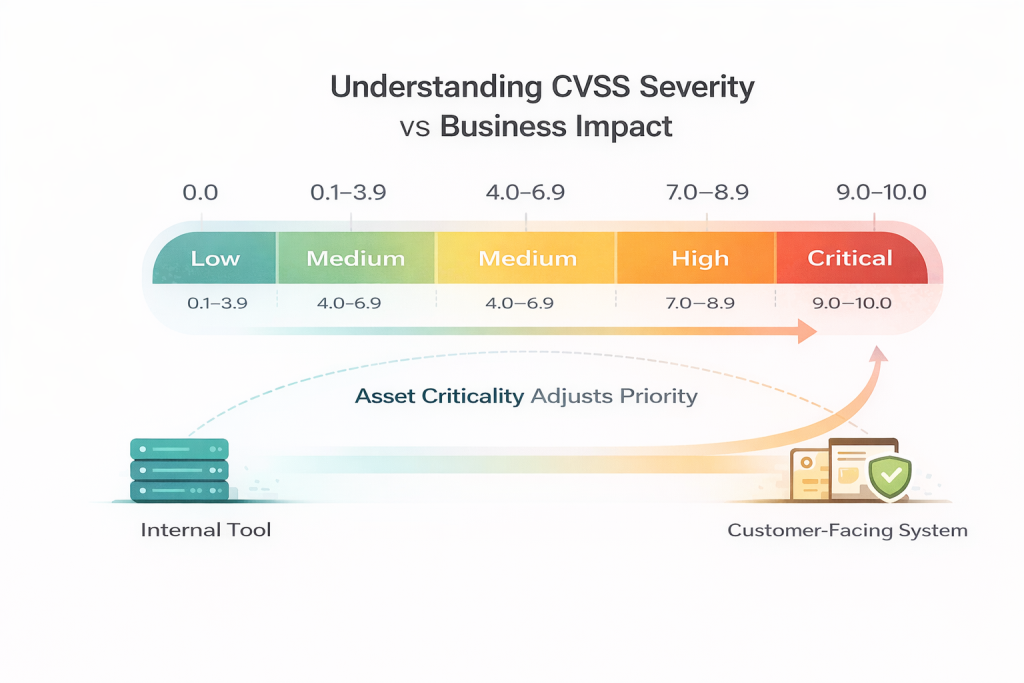
This framework assigns every vulnerability a score between 0.0 and 10.0, grouped into four severity bands. Each band carries a different remediation expectation:
- Critical (9.0–10.0): Requires immediate attention. Vulnerabilities in this range are typically remotely exploitable, need no authentication, and carry significant potential for damage.
- High (7.0–8.9): Should be addressed within seven to fourteen days. Exploitable under reasonably common conditions and not something to defer without a compensating control in place.
- Medium (4.0–6.9): Plan remediation within thirty days. Exploitation generally depends on specific conditions being met, but these findings should not be deprioritised indefinitely.
- Low (0.1–3.9): Schedule within your standard maintenance cycle. Limited exploitability and impact, but worth tracking over time.
The scoring system works well when it is used correctly. Where teams run into trouble is treating the number in isolation.
CVSS scoring includes an Environmental metric that allows the organization to adjust the score based on the asset’s criticality to the business. This provides context to the technical severity.
It is important to consider that a medium-severity finding on an internal tool used by three developers carries a very different risk profile than the same score on a customer-facing payment gateway processing transactions daily. The number is identical. The business impact is not.
This is why asset criticality must sit alongside every CVSS score when your team is building a remediation plan.
A vulnerability’s severity tells you how dangerous it could be. Asset criticality tells you how dangerous it is for your organisation, your data, and your customers in India specifically. Read together, they produce remediation decisions that are both technically sound and commercially sensible.
Turning VAPT Findings into a Practical Remediation Roadmap
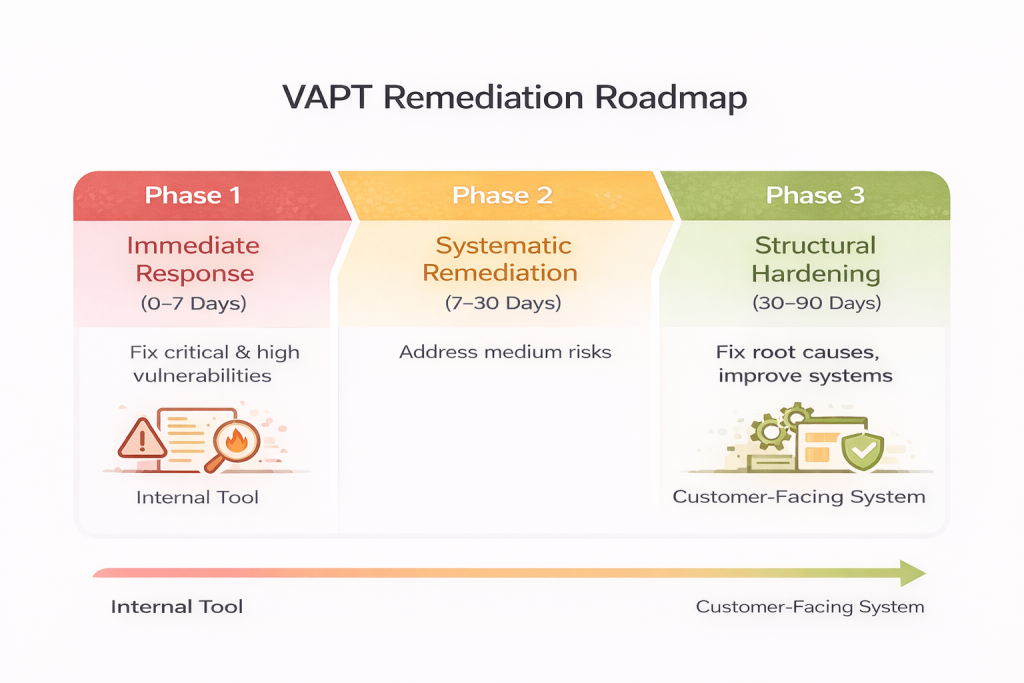
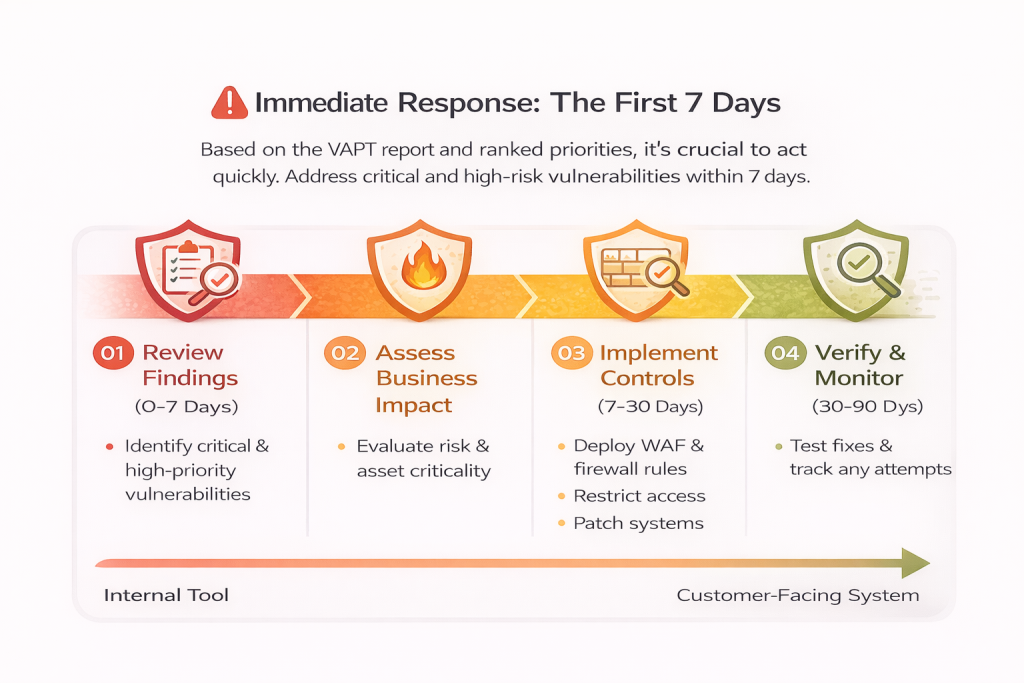
A VAPT report that sits unused quickly becomes a wasted investment. The real value lies in how effectively the findings are translated into remediation and security improvements once the report reaches your team.
However, many organizations make the same mistake and they focus only on fixing critical vulnerabilities and gradually lose momentum on the remaining issues.
A well-structured VAPT report guide emphasizes the importance of a phased remediation strategy that ensures all findings are addressed systematically.
In a VAPT report complete guide, remediation is not treated as a one-time patching exercise but as a continuous and structured process that prioritizes risk, assigns clear ownership, and ensures vulnerabilities are resolved without leaving gaps in the security posture.
Phase 1 – Immediate Response (Days 0–7): Isolate and remediate all critical and high findings. If a fix is not immediately deployable, apply compensating controls like firewall rules, access restrictions, or WAF (Web Application Firewall) policies to reduce exposure while the permanent fix is prepared.
Phase 2 – Systematic Remediation (Days 7–30): Work through medium-severity findings methodically. This phase is where a lot of teams stall. Assign clear ownership, set realistic deadlines, and track progress in your vulnerability management platform.
Phase 3 – Structural Hardening (Days 30–90): Go beyond individual patches. Address the root causes such as insecure configurations, outdated development practices, gaps in access control design. Integrate findings into your DevSecOps pipeline so the same class of vulnerability does not reappear in the next release cycle.
For organisations in India operating under CERT-In obligations, this documented phased approach also serves as evidence of due diligence during any regulatory inquiry.
Why Compliance Mapping in a VAPT Report Matters
Most of them only read the findings, assign remediation owners, and close the report. The compliance mapping section is usually tucked toward the end and gets skipped entirely. It is an easy oversight, but in India’s current regulatory climate, it is an increasingly costly one.
The DPDPA, RBI cybersecurity guidelines, SEBI’s cyber resilience framework, and CERT-In mandates do not just expect organisations to fix vulnerabilities.
They expect documented proof that security practices align with recognised standards. That proof does not need to be built from scratch, it already exists inside a properly structured VAPT report.
Also Read : VAPT Remediation Verification: How to Ensure Vulnerabilities Are Properly Fixed
When findings are mapped to ISO/IEC 27001, NIST CSF, or OWASP controls, your GRC team gains some genuinely useful audit-ready evidence that connects specific vulnerabilities to specific compliance obligations. No last-minute evidence gathering. No gaps in the control narrative.
For organisations pursuing SOC 2 Type II or ISO 27001 certification, this section is particularly significant. Auditors want to see that security weaknesses are identified, documented, and tied to a recognised control framework. A VAPT report with thorough compliance mapping does exactly that and it does it in a format that holds up under scrutiny.
Why VAPT Has Become Essential for Indian Enterprises
There is a recurring conversation in boardrooms across India: “How do we justify the VAPT spend?” The better question is: “How do we justify not having it?”
Consider the cost of ignoring VAPT, a delayed enterprise deal because the prospect’s security team flagged unresolved critical vulnerabilities in your assessment.
A cyber insurance claim rejected because the insurer found your last VAPT was two years old. An M&A (Mergers and Acquisitions) deal renegotiated downward after due diligence uncovered infrastructure exposure you were unaware of.
A current, clean VAPT report guide assists to remove friction from all of these scenarios. It tells customers, auditors, insurers, and acquirers the same thing: this organisation actively manages its security posture.
For businesses in India pitching to international enterprises or regulated clients, that signal can mean the difference between winning and losing on a shortlist.
Mobile App Penetration Testing: India’s Fastest-Growing Security Gap
India runs on mobile. And yet mobile application security remains one of the most consistently underfunded areas in enterprise VAPT programmes.
The OWASP Mobile Top 10 covers issues like insecure data storage, improper authentication, and unprotected API endpoints, which maps directly to vulnerabilities regularly found in Indian consumer and enterprise apps.
Also Read : Ultimate Mobile Application Security Checklist For Indian Businesses
A VAPT report complete guide emphasizes the importance of a structured, risk-based remediation strategy that should be prioritized based on risk, operational disruption, and available resources. It involves immediate fixes, compensating controls, and long-term improvements.
If your current VAPT scope does not include mobile, it is time to revisit the conversation with your service provider.
Strengthening Security Posture with Wattlecorp’s Expert Support
Receiving a VAPT report is straightforward. Knowing what to do with it and having the right team to support that process is where most organisations need genuine expertise.
Wattlecorp works with Indian businesses at every stage of that journey. From scoping and testing through to remediation advisory, compliance mapping, and ongoing vulnerability management, the engagement does not end when the report is delivered.
It continues until your organisation has measurably reduced its exposure and built the internal confidence to manage risk on its own terms.
The work spans web application and network penetration testing, mobile app security assessments, red team exercises, and GRC advisory aligned to India’s regulatory frameworks including DPDPA, CERT-In guidelines, RBI directives, and ISO 27001.
Through specialised Penetration Testing Services in India, Wattlecorp helps organisations uncover security weaknesses and align their security programmes with regulatory expectations.
Each engagement is shaped around your environment, your compliance obligations, and the specific outcomes your security programme needs to achieve.
If your organization conducts VAPT but struggles to translate findings into lasting security improvement, that is the problem Wattlecorp is built to solve.
VAPT Report Guide FAQs
1.What is included in a VAPT report for Indian companies?
A standard report covers executive summary, testing scope and methodology, detailed vulnerability findings, CVSS scores, proof-of-concept evidence, remediation steps, and compliance mapping. For organisations in India, it should also reference CERT-In guidelines, applicable RBI frameworks, and ISO 27001 controls. Ask your provider for a risk heatmap, it makes board reporting significantly easier.
2.How is CVSS scoring calculated in a VAPT report?
CVSS v3.1 uses three metric groups: Base (how severe the vulnerability is in isolation), Temporal (whether active exploits exist), and Environmental (how critical the affected asset is to your organisation). Scores run from 0.0 to 10.0. Any proper VAPT report complete guide will explain how to apply these scores in your specific context rather than treating them as universal thresholds.
3.Is VAPT mandatory for RBI-regulated entities in India?
Yes. RBI’s IT and cybersecurity framework requires periodic VAPT for regulated financial institutions in India. SEBI’s cybersecurity circular and CERT-In’s incident response guidelines carry similar expectations. Falling behind on VAPT cycles puts you at risk of regulatory findings during inspections and that is a harder conversation to have than simply scheduling the assessment.
4.What is the difference between a vulnerability assessment report and a penetration testing report?
Vulnerability assessment identifies and catalogues weaknesses largely through automated tools. Penetration testing takes those findings further by actively exploiting them to establish real-world impact. A complete VAPT report complete guide brings both together: the broad coverage of scanning with the depth of manual exploitation. You need both perspectives to make sound risk decisions.
5.How often should Indian organisations conduct VAPT?
At minimum, once a year. In practice, any major infrastructure change, new product launch, or post-incident review should trigger an additional assessment. Organisations in India operating in BFSI, healthcare, or critical infrastructure sectors should aim for quarterly testing cycles both for regulatory alignment and because their threat surface changes faster than an annual schedule can keep pace with.








