Key Takeaways:
- SAMA requires financial institutions in Saudi Arabia to have strict management of third-party risk to safeguard sensitive information and business continuity.
- The most critical risks associated with the vendor are the data breach, poor access controls, and compliance gaps that can be translated into significant disruptions.
- The best practices include risk-based assessment, contractual security provisions and continual monitoring in accordance with the cybersecurity framework of SAMA.
- Saudi Penetration testing services can be used to find vulnerabilities in vendor systems, which fulfills the annual testing need of SAMA.
- Wattlecorp offers customized SAMA third party risk management compliance consulting to simplify the third party risk management and vendor compliance.
Table of Contents
Toggle- Understanding Third-Party Risk Management Requirements Under SAMA in KSA
- The Critical Role of SAMA in Cybersecurity and Vendor Compliance
- Top Third-Party Vendor Risks to Watch Under SAMA
- Proven Best Practices for Managing Third-Party Risk with SAMA Compliance
- How Penetration Testing Reduces Third-Party Risks Effectively
- How Wattlecorp’s Expertise Drives SAMA Compliance Success
- Creating a Strong and Resilient Third-Party Risk Management Strategy
- SAMA Third Party Risk Management FAQs
Understanding Third-Party Risk Management Requirements Under SAMA in KSA
What if your entire financial operation was harmed by a breach from one vendor?
Third-party risk management under SAMA addresses this reality by requiring Saudi Arabian financial institutions to implement structured controls for external vendors to prevent data threats.
SAMA third party risk management focuses on visibility into vendor cybersecurity postures, closing regulatory compliance gaps, and preventing data protection failures that threaten business continuity.
SAMA requires all financial institutions in Saudi Arabia to follow the cybersecurity standards, particularly for managing through third-party vendors through its Cybersecurity Framework.
This SAMA framework demands formal risk assessments, review and ongoing audits to mitigate Sama Third Party Risks effectively.
Organizations may face insufficient cybersecurity maturity if it fails to meet these SAMA third party risk management measures, which exposes them to third-party breaches that disrupt operations across BFSI sectors.
The Critical Role of SAMA in Cybersecurity and Vendor Compliance
The purpose of SAMA regulations is to create clarity about the businesses using third-party vendors and to specify that cybersecurity controls must be integrated into their contracts and operations.
And the SAMA third party risk management tries to secure sensitive information with the help of risk-based oversight, ongoing evaluations and is consistent with wider enterprise risk management solutions.

The NCA provides compliance with cybersecurity in critical sectors in Saudi Arabia, including fintech, healthcare and more, which focuses on the third-party risk management to increase investor trust and data security in the financial sectors.
It mandates the vendor due diligence and assessment such as encryption requirements, multi-factor authentication, and data flows as the means of ensuring that the data does not fall in the wrong hands and that the violation of SAMA risk management frameworks is avoided.
Top Third-Party Vendor Risks to Watch Under SAMA
Does SAMA third party risk management warn about hidden vulnerabilities in the systems of your vendors?
Top SAMA Third Party Risks include data breaches through unauthorized access, unpatched software exploits and supply chain attacks etc lead organizational exposure.
All these threats probably developed from vendors’ lagging cybersecurity maturity that led to compliance gaps under SAMA regulations.
Also Read : How to Automate SAMA CSF Compliance: Tools, Tips & Real‑World Use Cases
In the Saudi government, they focus on improving cybersecurity to safeguard economic infrastructure, which directly affects vendor management practices through Vision 2030 initiatives.
Therefore, it is essential to be aware of the common challenges that are involved in third party vendor risks. Insufficient visibility into vendor controls, third-party cyber risk management failures and having disruptions from weak incident response in partner ecosystems are the most common pitfalls.
Proven Best Practices for Managing Third-Party Risk with SAMA Compliance
Ready to fortify your vendor ecosystem against SAMA scrutiny?
Here are the proven SAMA third party risk management practices that start with the selection of risk-based vendors using detailed vendor security assessment checklists that are used to evaluate cybersecurity controls, financial stability and compliance history.
- Integrate comprehensive contractual safeguards.
- Data Protection Agreements for encryption.
- Audit rights for inspections.
- SLAs tying performance to SAMA standards.
- Implement continuous monitoring.
- Automated tools for threat detection.
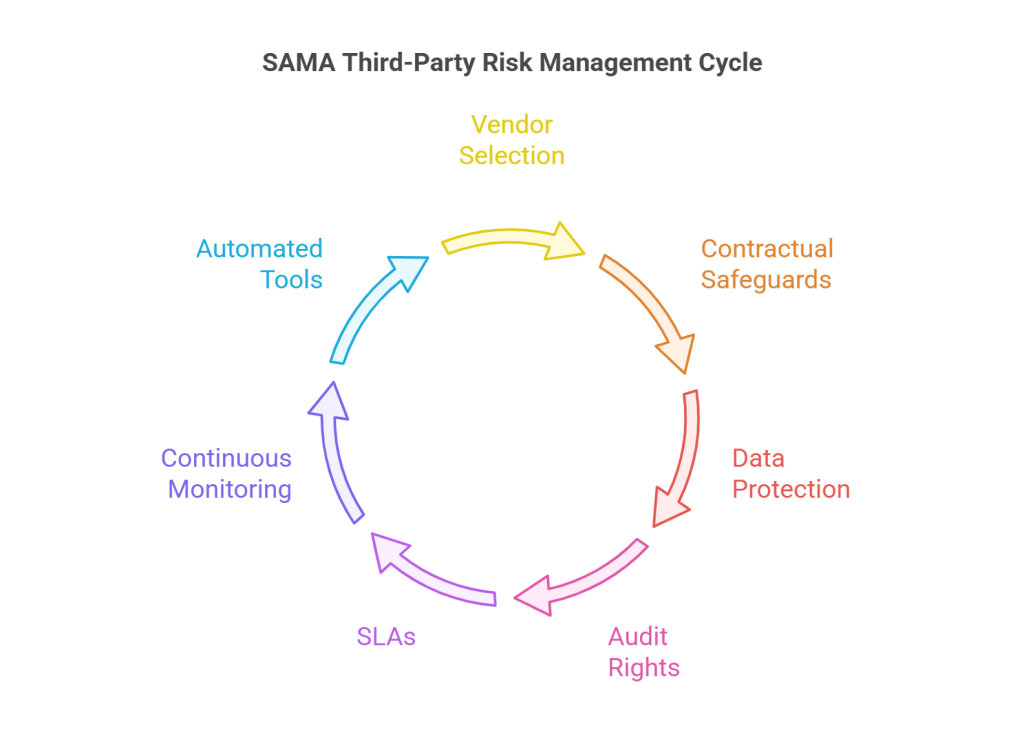
Alongside maintain a structured controls based process on vendor’s firms criticality to align with SAMA third party risk management framework.
Through conducting regular cybersecurity checks, reviews, and remediation processes supports tracking to combine third party risk management guide principles into operations.
This SAMA-compliant system assists to minimize the compliance challenges, improve resilience and integrates vendor risk management Saudi Arabia best practices like annual audits and KPI-driven oversight.
How Penetration Testing Reduces Third-Party Risks Effectively
Simulated attacks identify vendor weaknesses before real threats strike.
Penetration testing services in Saudi Arabia play an essential role in SAMA third party risk management. It follows adversary tactics on vendor systems to expose vulnerabilities like misconfigurations and privilege escalations.
This testing validates compliance with SAMA cybersecurity requirements, including mandatory annual audits of internet-facing platforms required for financial institutions in KSA.
Also Read : Internal vs External Penetration Testing: Which is Right for Your Business?
Through the identification of gaps in vendor defences such as weak APIs or unencrypted data, penetration testing helps to prevent breaches and ensures to meet NCA ECC and SAMA outsourcing circulars.
At Wattlecorp, our dedicated penetration testing service in Saudi emphasizes on red team exercises, vulnerability assessments and supports reducing third-party risks through prioritized remediation and evidence for regulatory reporting.
Integrating it into vendor security assessment transforms risk reality checks into proactive defenses that are critical for SAMA compliance third party risk management.
How Wattlecorp’s Expertise Drives SAMA Compliance Success
Having a hard time working through the vendor complexities at SAMA?
The SAMA compliance consulting services provided by Wattlecorp offer specialized third party risk management frameworks, beginning with vendor onboarding evaluations up to ongoing monitoring aimed at BFSI and SaaS clients.
Our team of specialists perform quick and comprehensive gap assessments on SAMA regulations in KSA focused and provide introduction of cybersecurity controls and execution of penetration testing to the mitigation of SAMA Third Party Risks are effective mechanisms.

We simplify the management of SAMA with the help of established rules to improve contracts and automated compliance tools, as well as data protection issues.
Working with Wattlecorp guarantees a secured third-party cyber risk management as well as staff training and audit preparation. And guarantee that you are ahead of regulatory requirements in Saudi Arabia in terms of business position.
Creating a Strong and Resilient Third-Party Risk Management Strategy
The regulatory framework of third-party risks by SAMA is not a compliance issue only.
It is a necessity factor for the protection of operational integrity and data security of your organization.
The need to have an extensive third-party risk management strategy in Saudi Arabia is very essential as financial institutions and businesses in Saudi Arabia continue to rely on external vendors.
By conducting thorough vendor evaluations with ongoing observation, contractual security and periodic penetration testing, an organization can become well-informed about vulnerabilities and effectively protect data, so that they are not utilized by complex cyber threats.
This will maintain the interaction with the changing SAMA cybersecurity framework and ensure resilience against advanced cyber threats.
Collaborating with professionals such as Wattlecorp enables the company to navigate through the complexity of the SAMA compliance with a sense of confidence based on its specialization in consulting services tailoring to local regulatory requirements.
Finally, the active approach to third-party risk management does not only meet regulatory requirements but establishes reputable relations with vendors and enhances the business continuity in general within the dynamic cyber environment in Saudi Arabia.
To make your defenses strong and make compliance smooth, contact Wattlecorp by use of our SAMA compliance consulting services to seek expert advice and assistance.
SAMA Third Party Risk Management FAQs
1. What is SAMA’s role in third-party risk management in Saudi Arabia?
SAMA requires financial institutions to evaluate, monitor, and audit third-party vendors by its Cybersecurity Framework to maintain alignment of cybersecurity and risk reduction. This is also applicable to all the contracts of the vendors where the Saudi Arabia financial ecosystem is safeguarded against third party vulnerabilities that cascade. Failure to comply may lead to fines and operational limitations according to the SAMA laws.
2. How does third-party risk management affect SAMA compliance?
Third party risk management can be effectively applied to KSA enterprise governance to avoid breaches and fines through the implementation of the due diligence and monitoring requirements of SAMA. It also creates a proactive security culture which enhances the overall organizational resilience to changes in cyber threat.
3. What are the key aspects of SAMA’s cybersecurity framework for vendors?
The key aspects involve risk evaluation, encryption requirements, yearly audits, incident response, and SLA compliance validation on all third-party relationships in KSA. All these elements with detailed defense based -in-depth programs support to protect sensitive data across the vendor lifecycle.
4. How can organizations ensure vendor compliance with SAMA regulations?
Compliance in organizations is through vendor security assessment checklists, contractual audit rights, continuous monitoring tools and cybersecurity exercises based on SAMA standards. Also, it is essential to establish an open communication and accountability with the vendors in order to ensure compliant partnerships.
5. Why is penetration testing crucial in managing third-party risks under SAMA?
Penetration testing is the process of simulating attacks to identify vulnerabilities in vendors, in accordance with the yearly testing requirements of SAMA and avoiding exploits that may destabilize financial activities. This will give real information on areas of weaknesses that can be rectified before the rivals can take advantage of the vulnerabilities hence strong third parties security.








