Table of Contents
ToggleIntroduction
The evolving cyber threat landscape of today’s digitalized world holds even the technically advanced systems like IoT and surveillance as continuous high-value targets for attackers. CVE-2021-36260 offers a perfect example for critical unauthenticated Remote Code Execution (RCE) vulnerability discovered in a wide range of Hikvision IP cameras and NVRs.
This article outlines our in-depth analysis of the vulnerability, how the same can impact enterprise infrastructure, and how you can secure your business environments once these are affected.
Understanding the Vulnerability
CVE-2021-36260 is a severe command injection vulnerability that exists in the web server interface of Hikvision devices. Unauthenticated attackers can then execute system-level commands with root privileges via specially crafted HTTP requests.
The vulnerability occurs secondary to improper user input validation. This allows attackers full control of the device by sending messages that contain malicious commands. Actions like these do not require any credentials or user interaction.
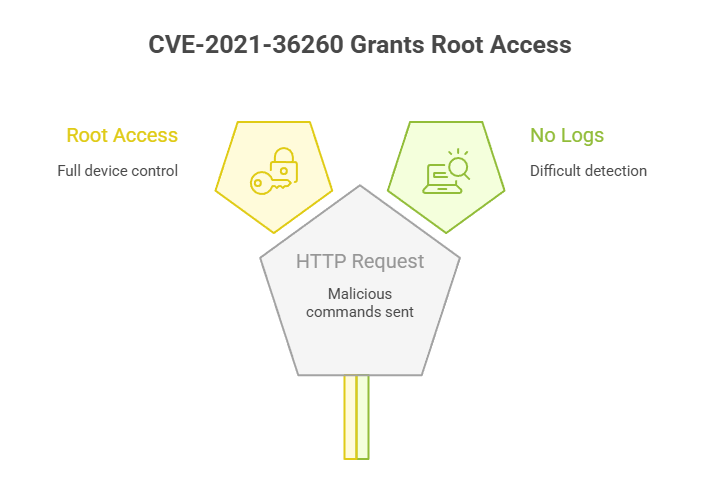
The flaw is exploitable over the network and does not generate device side logs, which makes detection extremely difficult.
Risk Assessment
| Category | Description |
| Exploitable Remotely | Yes |
| Requires Authentication | No |
| User Interaction Required | No (Zero-click) |
| Device Impact | Full Root Access |
| Log Visibility | Not Logged Locally |
| Critical Infrastructure Risk | Yes, if deployed in production |
Technical Overview
The vulnerability or command injection gets triggered when Hikvision’s web server running on ports 80/443, processes an unsanitized HTTP input. An attacker can thus pass malicious commands through parameters in a GET or POST request. The server executes it with root-level privileges.
Also Read : 5 Signs Your Business Needs VAPT Immediately
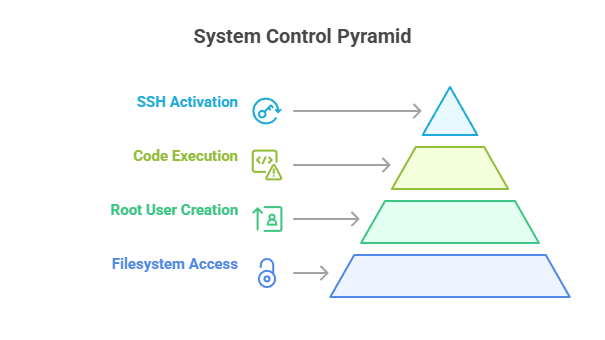
What happens next is that these commands bypass Hikvision’s psh (protected shell), designed to restrict admin-level operations. An action like this enables attackers to:
- Access and modify the filesystem
- Create a user with root privileges
- Execute arbitrary code
- SSH daemon activation for persistent access
Proof of Concept (PoC)
A PoC demonstrating real-world exploitability was safely executed on a consented testing device. We attempted:
This demonstrates how a threat actor can achieve full control of the device and potentially use it to gain entry into your internal network.
- Enumeration of internal device data
- Reading sensitive system files (/etc/passwd)
- Creation of unauthorized root users
- Activation of dropbear SSH server
- Web interface access bypass using arbitrary credentials
Also Read : VAPT as a Service (VaaS): A Cost-Effective Solution for Cyber Risk Reduction
Remediation & Patch Analysis
Hikvision responded by releasing a firmware update (e.g., v5.5.800 build 210628). Our verification process confirmed:
● Removal of unauthenticated command injection vectors
● Input validation was enforced and in place
● Root shell bypass was made impossible
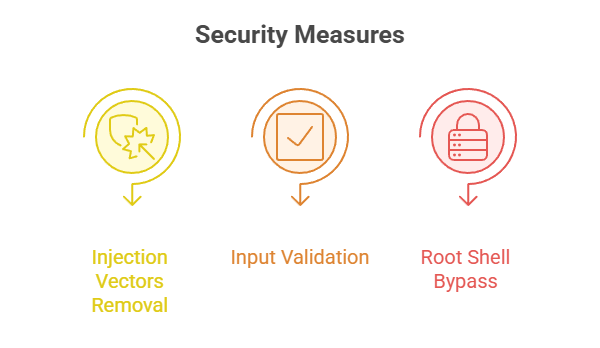
We also came across regional inconsistencies in patch availability, which led to uneven remediation across global deployments.
Security Observations
In exploiting the RCE (Remote Code Execution) vulnerability that was detected, we found security gaps that were critical enough to warrant immediate remediation. When ignored, they can potentially and increasingly cause breach to be undetected with prolonged attacker presence within a network.
● No logs generated during exploitation
● Devices remain operational, masking the breach
● Attack vectors persist unless patches are applied
● Compromised devices leveraged for network reconnaissance and data exfiltration by threat actors.
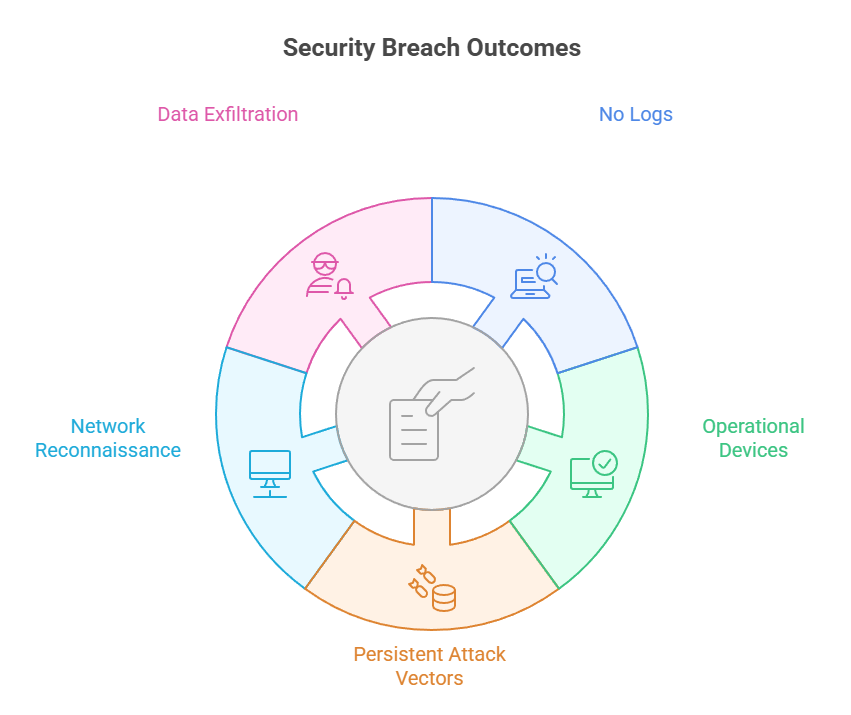
We recommend that organizations treat these devices as potential internal threat vectors unless properly segmented and monitored.
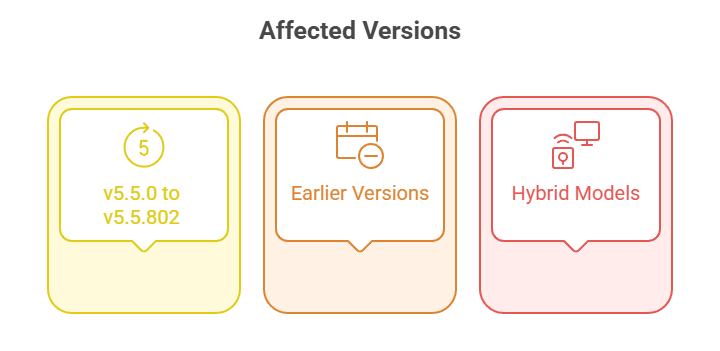
Affected Firmware Versions
The vulnerability affects numerous firmware builds across several product lines. These include:
● v5.5.0 to v5.5.802 (IPC_G3)
● Earlier versions dating back to 2016
● Potentially impacted hybrid NVR and DVR models.
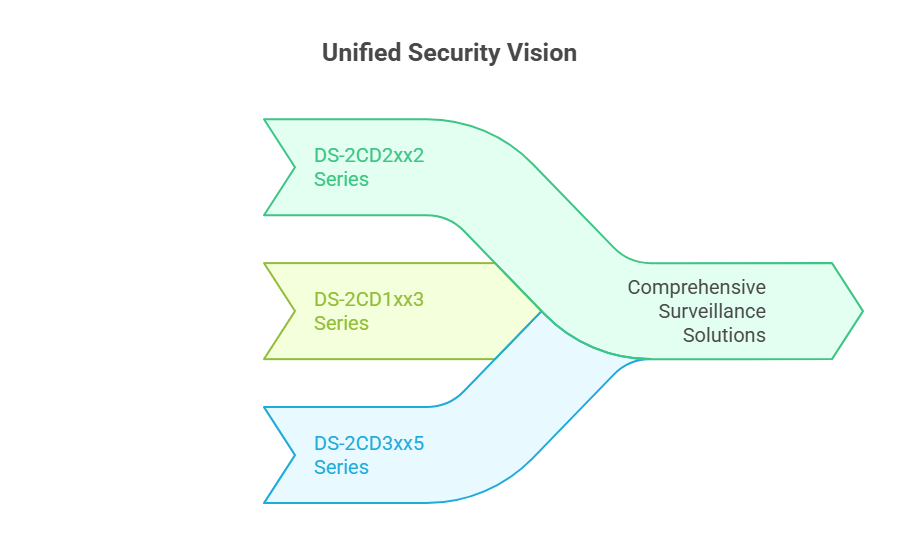
List of Affected Models
Confirmed vulnerable product lines include:
● DS-2CD2xx2 series
● DS-2CD1xx3 series
● DS-2CD3xx5 series
For a complete list, please refer to Hikvision official advisory.
The CVE-2021-36260 vulnerability exploitation in the realm of cybersecurity goes beyond proof-of-concept by allowing hackers, often remote attackers. to gain more control over the camera. It often and again reminds us of real-world threats that can surpass even the widely deployed security devices.
If these can become silent gateways for cyber intrusions, so can your network and connected systems too.
From failing to detect log-ins to persisting attack vectors, these are enough to provide threat actors enough chances to send malicious codes.
Now, these are enough alerts for organizations like you, who specifically rely on Hikvision or similar IoT/OT security solutions. Ignoring such vulnerabilities is definitely not an option, rather a critical necessity.
The path forward is clear and indispensable to applying security patches without any more delays, enforce network segmentation, enable robust monitoring, and treat every unpatched or exposed device as a potential internal threat vector.
Because cybersecurity in an era of increasingly sophisticated cyber threats shouldn’t be compromised on any device in your network. And this also includes the security systems you utilize. At Wattlecorp, we won’t let any such threats skip from our watchful eyes. You can always rely on us to achieve both security and continuity at one stretch through our extensive VAPT services.
Want to upgrade your security? Reach out to us and we’ll help you safeguard them, allowing you to focus on your core business while we secure it.
it’s better to be proactive than reactive.
Stay vigilant, stay patched. Get a VAPT assessment today!
RCE Vulnerability FAQs
1.What are Hikvision Devices?
They refer to a range of security products that include cameras, NVRs (network video recorders), and access control systems.
2.What makes Hikvision devices different from other security systems?
It is their capacity to offer advanced analytics that makes Hikvision devices stand out from other contemporary security devices. Also, for the high-resolution imaging they provide, combined with their varied features and scalability add to their reliability. Coupled with these features are the specific needs and budget they help meet for the organizations that adapt them.
3.How can I know whether my Hikvision security device is compromised or not?
To know if your Hikvision security camera is compromised or not, you need to follow the below steps:
Verify the firmware version against known vulnerable versions (the primary step).
Check if there’re any unusual notifications, such as changes in privacy settings, unusual logins, etc.
Monitor network traffic.
Review user accounts to look for any unauthorized access attempts, suspicious logins, etc.
Review if any unintended or unusual ports are open on the camera’s IP address.
4.What’s the best method to secure the Hikvision security camera?
A more proven practical way to secure your Hikvision security cameras is to start by isolating them by creating virtual LANS (VLANs). Being a virtual group of network devices, VLANs can be managed as if they are connected to a single network switch; while in reality, they’re not.







