Table of Contents
Toggle- Understanding ISO 27001 Surveillance Audits for Companies in Saudi Arabia
- Certification, Surveillance and Recertification Audits: Major Differences.
- What Makes Surveillance Audits Are Important?
- Frequency & Scope of Surveillance Audits under ISO 27001
- Key Stages in the Surveillance Audit Process
- Common Findings in Surveillance Audits & Its Remedies
- Surveillance Audit Reporting: What Should Be in the Report?
- Preparing for Surveillance Audits in Saudi Arabia
- Why Penetration Testing Matters in Saudi Arabia?
- Choosing Best Practices for Maintaining Compliance Between Audits
- ISO 27001 surveillance audit FAQs
Understanding ISO 27001 Surveillance Audits for Companies in Saudi Arabia
ISO 27001 is not just a certification, it is a commitment.
ISO 27001 is an internationally accepted standard for managing information security using an Information Security Management System (ISMS).
Do you know how leading businesses really secure their data?
It enables organisations to systematically handle data protection, risk management, and regulatory compliance. However, the certification is only the beginning, and to maintain the ISO 27001 certification organisations must undergo surveillance audits, which confirm the ISMS remains functional and is continuously improved.
When was your ISMS’s real health checkup done?
These audits serve as annual checkpoints between the initial certification and the next recertification.
Why surveillance audits matter, especially in KSA.
The authorities or regulators locally, like the National Cybersecurity Authority (NCA) and the SAMA believe that certified entities are required to be in ongoing compliance.
Moreover, there’s another side too.
To remain compliant is beneficial in establishing customer trust, tenders, and enhancing digital resilience for businesses aligned with Vision 2030.
Certification, Surveillance and Recertification Audits: Major Differences.
The preparation of the audit lifecycle of ISO 27001 consists of three key stages.
Understanding the differences makes a huge impact.
Have you ever checked what’s the next thing after getting ISO certification?
It is not only about getting the certificate.
But your ISMS should consistently show its efficiency by three main audits.
Certification Audit, Surveillance Audit and Recertification Audit.
● Certification Audit: There are 2 Steps in Certification Audit.
- Document review
- Onsite assessment
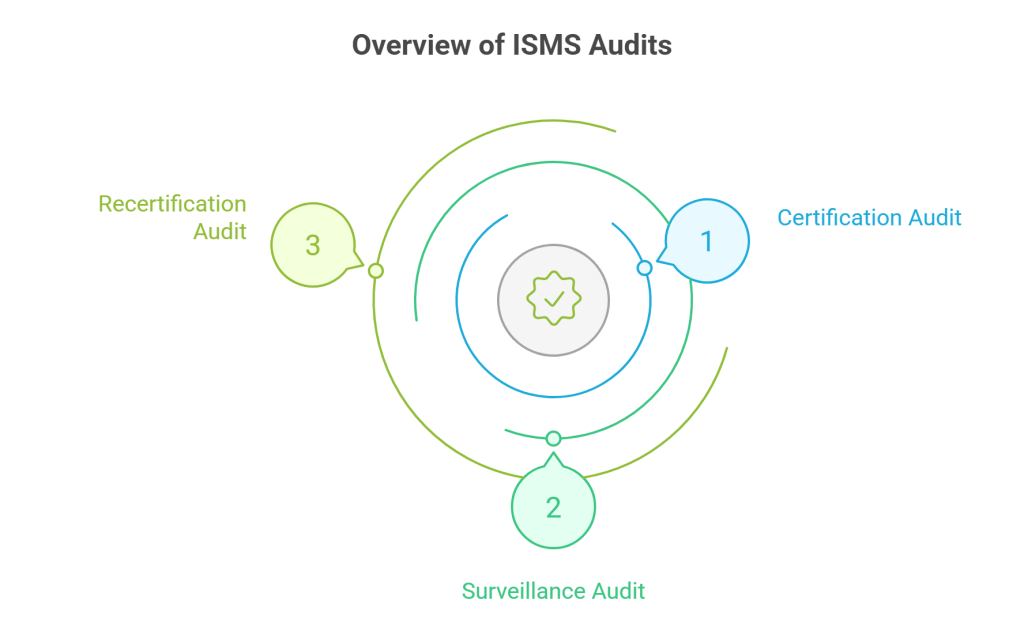
It ensures that documents are matched and how it works according to.
● Surveillance Audits: It ensures that your ISMS operates as required and that results of the last audits are addressed accordingly.
● Recertification Audit: This audit is implemented after the completion of the three years cycle in order to re-certify the overall ISMS.
The ISO 27001surveillance audit is not as exhaustive as the certification process but it is equally significant in maintaining the compliance and operational assurance.
What Makes Surveillance Audits Are Important?
Surveillance audits assist to protect organisations from lapses that may go unnoticed after the initial certification.
It actually serve as structured reviews to ensure:
- The security policies that remain up to date.
- Risks are actively monitored and mitigated.
- Employees continue to follow ISMS procedures.
- Better compliance with regulatory and client expectations.
In addition to that, as per KSA law, surveillance audits are an essential for your company’s ongoing development, and here comes the list of Surveillance Audits importance.
- Ongoing Compliance: Guarantees that your ISMS keeps up with ISO 27001 requirements.
- Risk management: Frequent audits assist in locating and reducing the possible security threats.
- Stakeholder Confidence: To gain the confidence of partners, clients and regulators, there must be regular adherence to it.
- Process Improvement: Audits can assist a continuous improvement culture by exposing the areas for development, audits support a continuous improvement culture.
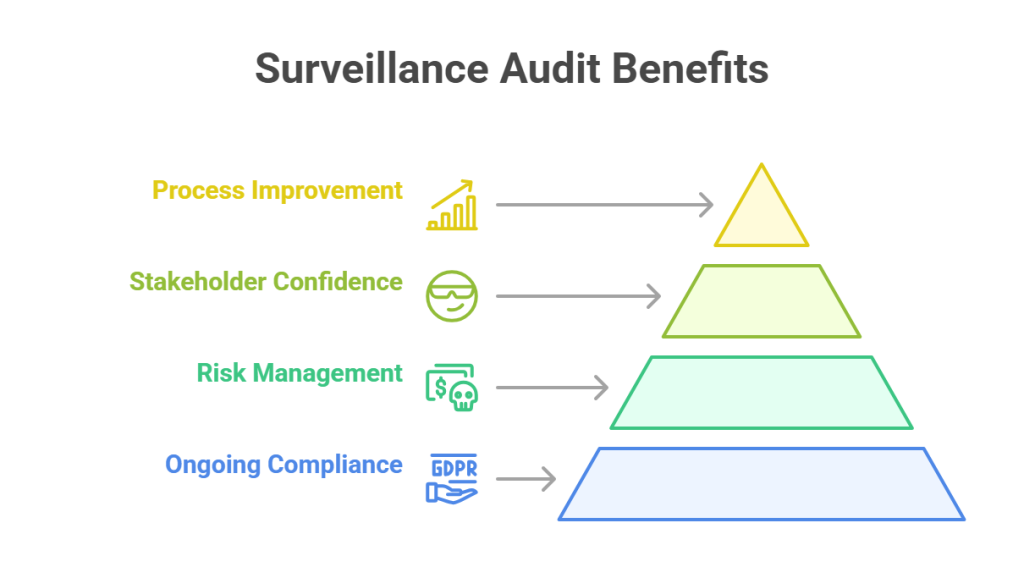
In this rapidly evolving threat landscape, choosing the right ongoing scrutiny helps organisations in KSA to demonstrate accountability and confidence in their security posture.
Think of it this way, when the certification is done, you get recognised, but surveillance audits keep that recognition more alive and credible.
Frequency & Scope of Surveillance Audits under ISO 27001
The ISO 27001 certification in KSA is valid for three years, during which surveillance audits occur annually. Depending on the organisation’s size and scope, the audit body may examine all ISMS areas or focus on selected, high-risk domains.
Typical review areas include:
- Implementation of corrective actions.
- Updated risk assessments and treatment plans.
- Results from internal audits and management reviews.
- Incident response measures and training records.
Also Read : What Are the ISO 27001 Requirements in 2025?
Maintaining readiness throughout the year assists to ensure your audit process remains smooth and predictable.
Key Stages in the Surveillance Audit Process
The ISO 27001 surveillance audit process involves a few steps such as preparation, audit execution and closing and reviewing the audit.
- Planning and Scoping: It includes preparation for defining audit boundaries, timing, and required evidence.
- Documentation Review: Verifying ISMS policies, control logs, and security incident records.
- On-site Inspection: Assemble audit team and interviewing staff for reviewing the samples and checking control implementation.
- Audit Planning: Audit planning includes listing the conformities, non-conformities, and potential improvements.
- Reporting and Follow-up: Producing the final surveillance audit report and tracking corrective actions.

Each of these stages ensures that the ISMS continues to operate efficiently and it aligns with both ISO and the local cybersecurity standards.
Common Findings in Surveillance Audits & Its Remedies
- Identify outdated documentation or policies.
- Delay in the follow-up for identified problems.
- Lack of proper training or awareness sessions.
- Missing risk reassessment records.
These are common mistakes and to avoid these, conduct regular internal audits, update documentation promptly, and maintain visible records of each action. Continuous monitoring helps to demonstrate the control maturity during audits.
Surveillance Audit Reporting: What Should Be in the Report?
A standard surveillance audit report contains:
- Audit scope and objectives.
- Evidence reviewed.
- Non-conformities and suggested betterments identified.
- The unresolved issues require follow-ups.
It is not a paper work report, but a performance picture of your ISMS that outlines the way forward to improve on the same.
Preparing for Surveillance Audits in Saudi Arabia
Preparation should start months before the scheduled audit. Saudi organisations should ensure:
- Alignment with NCA Essential Cybersecurity Controls and SAMA frameworks.
- Closure of all prior non-conformities.
- Updated ISMS risk registers and control records.
- Conduct of management reviews and internal audits.

Making compliance procedures localised to comply with Saudi regulations will make sure that there are no discrepancies between the global standards and the national requirements.
Working with an expert such as Wattlecorp assists in closing the regulatory or technical loopholes prior to the date of the audit.
Why Penetration Testing Matters in Saudi Arabia?
What if your ISO 27001 audit beyond just checking the security.
That is exactly what penetration testing does.
Its results are tangible evidence of evaluating what auditors can do in order to evaluate control effectiveness.
And proves that controls are not only documented, but tested. It aids in the determination of weaknesses at an early stage and assists in the correctional planning.
Also Read : How To Choose The Right Penetration Testing Company For Your Business?
It demonstrates the capability of ISMS to adjust to the changing cyber threats.
In Saudi Arabia, organisations increasingly integrate penetration testing services as part of their surveillance audit readiness strategy.
Wattlecorp’s penetration testing service in Saudi Arabia delivers these insights while aligning results with ISO 27001’s Annex A controls and NCA requirements.
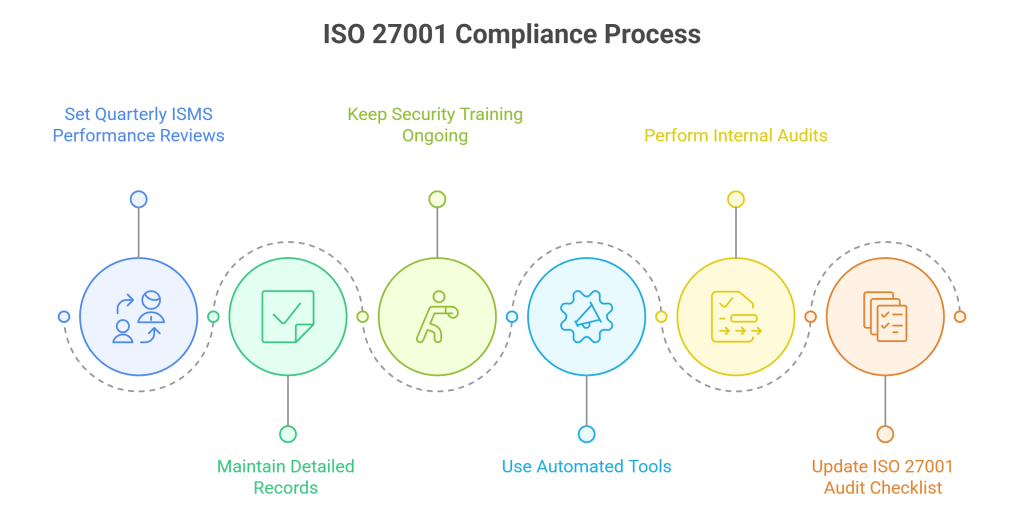
Choosing Best Practices for Maintaining Compliance Between Audits
- Set quarterly ISMS performance reviews.
- Maintain detailed records of incidents and actions.
- Keep security training and awareness ongoing.
- Use automated tools to track corrective actions.
- Perform internal audits ahead of external ones.
- Regularly update your ISO 27001 audit checklist.
The best practices for maintaining compliance between audits is not about scrambling before an audit because it is more about weaving security discipline into everyday operations.
ISO 27001 surveillance audit isn’t just as a security checkpoint, it’s more like a chance to prove your security really works.
In fact, it is important that your information security system is reliable, efficient and capable of dealing with emerging challenges.
So you need to be confident with every audit.
Step ahead with reviewing your ISMS regularly and doing internal checks.
Wattlecorp assists Saudi companies with this process-providing guidance on the ISO 27001 compliance auditing, preparedness, documentation, and penetration testing services to enhance the resilience of the ISMS.
To remain audit ready and to retain the confidence of clients and regulators, contact Wattlecorp to address a gap analysis or ISO 27001 surveillance audit preparation service.
ISO 27001 surveillance audit FAQs
1.What is the difference between surveillance audit and recertification audit for ISO 27001?
A surveillance audit checks ongoing compliance during the certification period, while a recertification audit renews the certification after three years.
2.How often must surveillance audits occur under ISO 27001?
Surveillance audits typically occur once a year and though some certification bodies may set a different schedule based on the risk or organisational complexity.
3.How should organisations in Saudi Arabia prepare for their surveillance audit?
Organisations in Saudi Arabia should close non-conformities, review documentation.
It ensures their ISMS aligns with NCA and SAMA cybersecurity requirements for their surveillance audit.







