Technology has come a long way since its inception. Especially the way it deals with the generation and manipulation of new and existing content. From setting filters and tweaking the nature of a photograph to make it more aesthetic to playing around with a video to feature the presence of someone else who isn’t in the video by exchanging it for someone who is, it is actually quite impressive. The technology that I mentioned is called deepfake. Let us look at what deepfake is.
Table of Contents
ToggleWhat Is Deepfake?
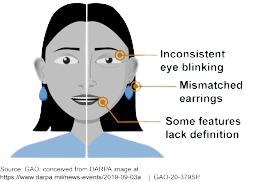
Deepfake is a technology that is used to impersonate people with a high level of accuracy. Used mainly in video content, it is difficult to distinguish from real ones. The authenticity of deepfakes has gotten better over time.
Read More: Understanding Blueleaks
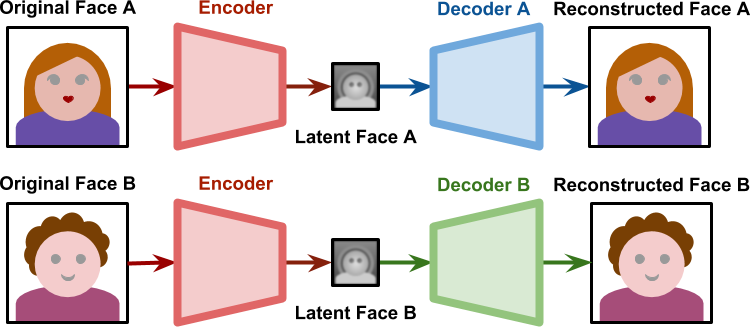
How does Deepfake Work?
Read More: WhatsApp Pink Scam: How Clicking On A Link Gets Your Phone Hacked
Malicious Use of Deepfakes
Reports on deepfakes state that around 96% of deepfakes on the internet are nonconsensual pornographic content. This might seem like deepfakes affect the only 
Interested to learn more about other kinds of cybercrime? Follow our blog to keep yourself updated with the latest trends in cybersecurity.
Contributors: Adithya Amarnath